When the name Cyber Islamic Resistance (CIR) appears, the most common reaction is fairly predictable. That predictability makes sense, because the instinct is to determine whether it is a real group or a more or less inflated coalition organizing a narrative around operations of mixed or uncertain provenance. It is a fair question, but probably not the most useful one. At this point, CIR’s importance does not seem to rest only on the sophistication of the attacks it claims or on the ability to verify, one by one, every incident it publicizes. What is becoming more important is the function it performs within a broader digital environment shaped by propaganda, ideological mobilization, and hybrid warfare.
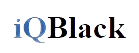
Cyber Islamic Resistance as a node connecting narrative, allies, targeting, and communication channels within a digital ecosystem aligned with the axis of resistance.
Seen from that angle, Cyber Islamic Resistance begins to look less like a conventional intrusion actor and more like a connective node. It acts as a hub capable of organizing discourse, campaigns, identity, and visibility within a pro-Iran, anti-Israel ecosystem aligned with the so-called “axis of resistance”. That feature changes the way the actor should be profiled. The question is no longer just how much it “hacks”, how advanced its tactical and technical capabilities may be, or how deep its TTPs really go. The more important issue is the role it plays in building a digital front that needs to appear unified, active, and expanding.
Recent signals point in that direction. In late March 2026, Unit 42 reported that several operations were associated with an “Electronic Operations Room” established on February 28, while SOCRadar documented that Cyber Islamic Resistance publicly announced on March 1 the creation of a joint operations room and a broader cyber mobilization effort through Telegram. That picture does more than suggest coordination. It also reveals a clear intention to project the image of a common front and operational continuity, clearly aimed at increasing the collective weight of the ecosystem within the contested space.
That is probably the most interesting aspect of Cyber Islamic Resistance. Its significance does not seem to be explained only by the technical damage it may be capable of causing, but by its ability to turn dispersed actions into a coherent narrative of digital resistance. It does not simply communicate operations; it helps frame them, give them political meaning, and project them publicly. That is where it begins to function as a social infrastructure of hybrid warfare rather than as a standalone group or an isolated propaganda channel.
That logic also helps explain why certain figures and channels matter within the ecosystem. The recurring appearance of the actor known as “Abo Omar”, also referenced as “Tito”, as a visible point of reference, together with the sustained circulation of messages and content through aligned Telegram channels, reinforces the impression of a communications architecture designed to sustain continuity, orientation, and a sense of belonging. Rather than an occasional sum of teams aligning out of convenience, what begins to emerge is an environment capable of distributing narrative, recycling legitimacy, and maintaining a shared identity even when its nodes operate with different levels of autonomy.
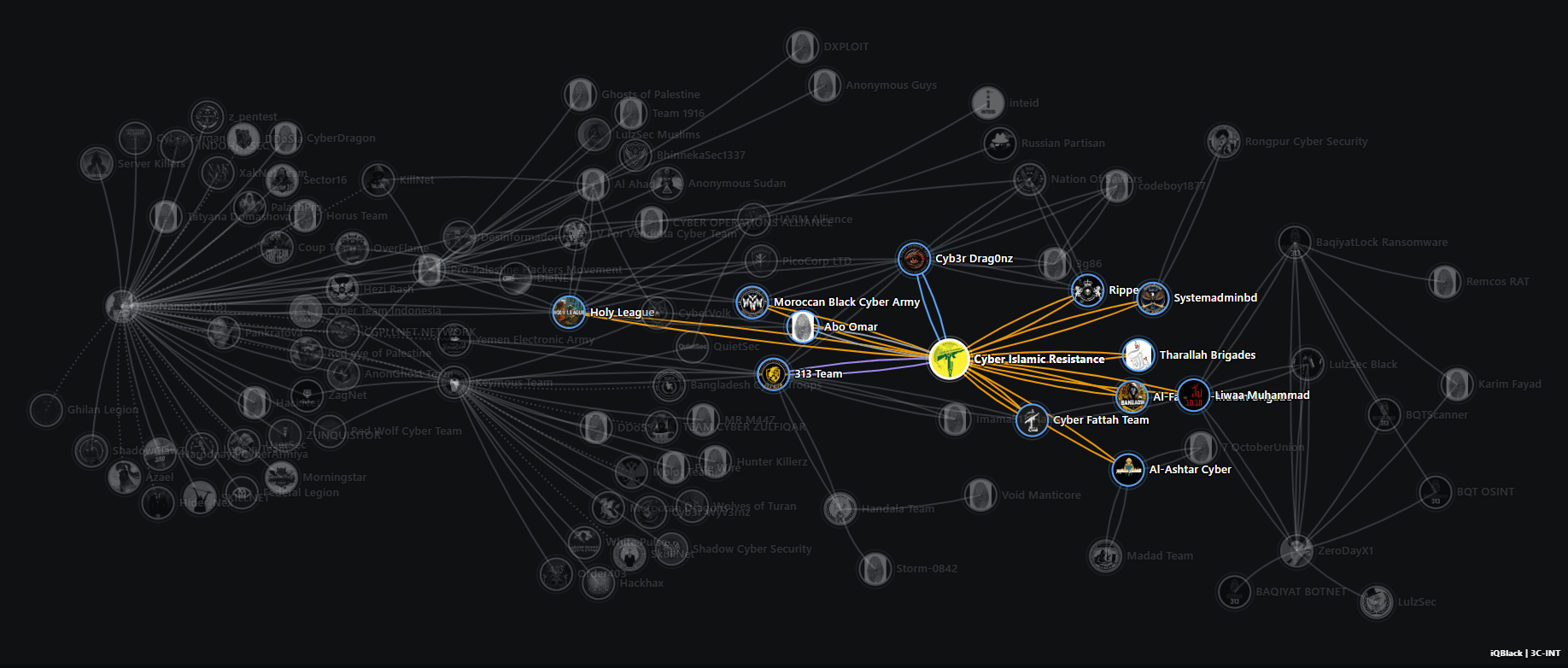
Expanded map of public relationships and visible affinities around Cyber Islamic Resistance, Holy League, and other nodes within the aligned hacktivist ecosystem.
Viewed from this perspective, Cyber Islamic Resistance does not only help explain one actor. It also sheds light on a form of organization that appears to be gaining weight in today’s digital conflict environment. More broadly, it may reflect a wider transformation.
Across different militant and extremist environments, the centrality of a single geographic core or one dominant organization has increasingly given way to more distributed, modular, and adaptive models. In digital space, that logic translates into visible coalitions, shared branding, operations rooms, affiliated channels, and mobilization campaigns that can be activated quickly around a cause or a moment of escalation.
This matters in particular when trying to place Cyber Islamic Resistance within the digital environment of the “axis of resistance”. There is no need to claim that it is a formal arm of Hezbollah or Hamas to recognize a strong narrative, symbolic, and ideological alignment with that ecosystem. In fact, it is better not to overstate the point. Discursive and symbolic proximity is observable; an organic chain of command, by contrast, remains much harder to demonstrate. Based on the open evidence currently available, the first is a reasonable assessment. The second remains significantly more difficult to substantiate.
Another element that makes Cyber Islamic Resistance especially interesting is its ability to move within a zone of convergence with pro-Russian actors. This point should not be overstated, but it should not be minimized either. The overlap in targets, platforms, adversaries, and repertoires of agitation between certain pro-Iran actors and certain pro-Russian hacktivist spaces opens a zone of compatibility that deserves geopolitical attention. Not necessarily because a total alliance or deep operational integration exists in every case, but because functional convergence alone is enough to produce scale effects, reciprocal legitimization, and an expansion of digital conflict.
That matters more than it may initially seem. For years, parts of the security community tended to examine these ecosystems on relatively separate tracks: on one side, the pro-Iran front and the “axis of resistance”; on the other, the broader galaxy of pro-Russian actors. In practice, however, when political incentives align, those worlds can overlap, support each other, or at least share narrative space. Cyber Islamic Resistance appears able to operate with relative ease within that zone of contact, and that increases its value as a threat intelligence object.
For that reason, reducing the analysis to whether Cyber Islamic Resistance is technically “strong” or “weak” can be misleading. In hybrid warfare environments, relevance is not always defined by the sophistication of tools. Sometimes it is defined by the ability to organize belonging and sustain the perception of coordinated action. An actor may not have an exceptional technical ceiling and still be strategically useful if it can project cohesion, maintain mobilization, and give visibility to a coalition.
This also changes the actor’s analytical value. The issue is no longer just counting defacements. It is about observing activation cycles, escalation moments, public validation among groups, the persistence of branding, aliases and associated handles, recruitment patterns, shifts in campaign language, and changes in targeting. Put differently, an important part of what makes Cyber Islamic Resistance relevant lies not in technical telemetry alone, but in ecosystem telemetry.
If this reading is on the right track, then the future of the phenomenon does not depend only on the name Cyber Islamic Resistance. Even if the label changes, fragments, or becomes less visible, the function it seems to perform today may persist in other forms. That may be the most important point of all. More than a single group, it may be showing a broader mode of organizing digital conflict, one in which the boundaries between actor, platform, propaganda, and operation become increasingly blurred.
That, ultimately, is why it is worth watching closely. Not only because of what it claims to have done, but because of what it reveals about the evolution of the digital ecosystem aligned with the axis of resistance. In that sense, Cyber Islamic Resistance is not just another profile on the threat landscape. It is also a sign of the times.
Methodological
note:
This article draws on internal profiling
inputs developed in 3C-INT* on Cyber Islamic Resistance, analysis of
the actor’s public communication channels, and a review of Hezbollah and Hamas
profiles in 2C-INT**
* 3C-INT — [Cyber]Crime Characterization for
Intelligence. Category: Hacktivist Group.
** 2C-INT — Conflict Characterization for Intelligence. Category:
Terrorism.
Explore 2C-INT
Go deeper into criminal, extremist and hybrid structures through an intelligence environment built around context.
Get new publications
Subscribe to receive new articles and public updates from iQBlack without unnecessary noise.