Not every actor deserves early attention because of scale. Some deserve it because they make their surroundings easier to read.
Morningstar fits that second category. Its public footprint remains limited, its structure is still diffuse, and there is not enough basis to treat it as a first-tier actor within the pro-Russian hacktivist space. That is precisely why it is useful to observe now. More than for any dense body of firmly corroborated operations, Morningstar matters because of what its behavior reveals about a layer of the Russia-aligned ecosystem where visible access, content circulation, mutual validation, and relational positioning can matter as much as individual technical capability.
That is probably the most useful way to read the case. The mistake would not only be to underestimate the actor for being “small.” The mistake would be to miss the fact that actors like this can function as early signals of how legitimacy is built inside certain hacktivist environments: what kinds of access are put on display, what kinds of targets are chosen for symbolic effect, which names are invoked to gain status, and which alliances are celebrated to project belonging.
In terms of observable activity, Morningstar is not starting from zero. Its public footprint had already shown a pattern centered on unauthorized access to cameras and exposed systems, with an emphasis on visible proof and psychological effect rather than quiet persistence or deep intrusion. That picture became somewhat denser with claims associated with cameras at Columbia University, visible systems in Israel, and other demonstrative forms of access. Taken together, the actor still looks less like a mature structure and more like an active node with a thin OSINT base, yet more embedded than it first appeared within a broader environment of pro-Russian affinity, propaganda, and mutual signaling.
What its public trail reveals first is not an obsession with technical depth, but with display. The actor’s communications function as a showcase of visible access, provocative messaging, international target “tours,” and proof-of-presence in cameras, urban environments, or exposed systems. The language is aggressive, theatrical, and openly propagandistic. The output does not appear designed to document operations for technically specialized peers, but to turn access into public presence, intimidation, and narrative noise.
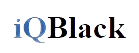
Morningstar’s visible geographic footprint. Geographic distribution of the countries associated with Morningstar’s publicly observable footprint. The visualization does not imply a uniform campaign or the same level of access in every case, but it helps illustrate the breadth of its visible target selection and narrative reach.
That does not automatically make Morningstar a superficial actor. But it does help place its value proposition more accurately. What appears so far is a profile that seems more comfortable in the register of visible access and performative gesture than in that of quiet intrusion or sustained, high-end capability claims. That trait alone already makes it interesting inside an ecosystem where usefulness is not always measured by sophistication, but also by the ability to produce recyclable material, exploit targets with symbolic value, and maintain a recognizable presence.
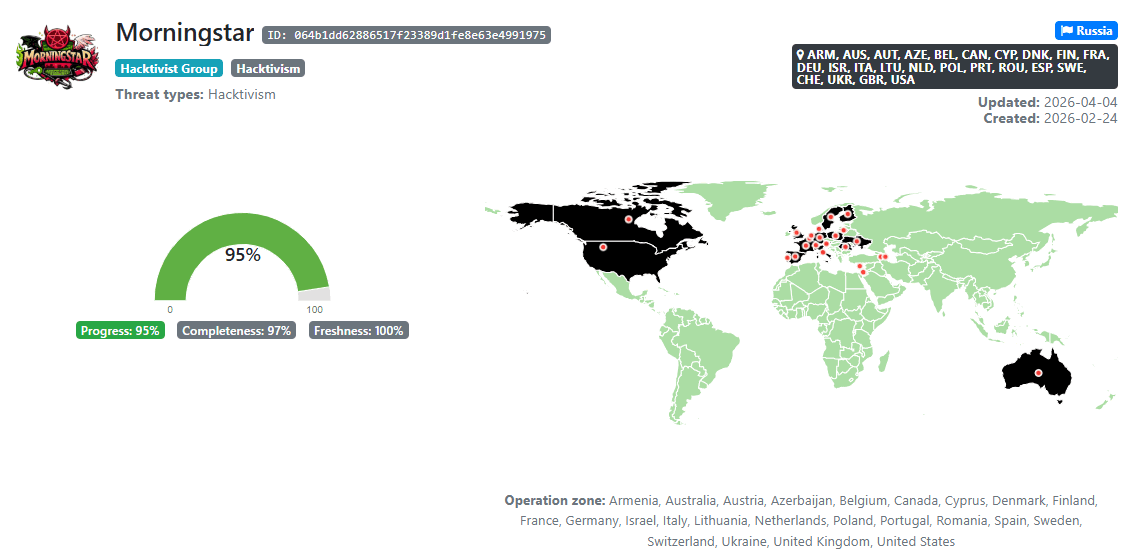
The relational side of the case is even more revealing. Morningstar mentions Z-Pentest Alliance far more often than any other name in its orbit. It also frequently forwards that group’s content, publicly thanks it for media support, and presents that relationship as a source of legitimacy, exposure, and learning. In several messages, the actor not only celebrates its alliance with Z-Pentest, but explicitly acknowledges that this proximity helped it gain attention from at least some media outlets. That detail shifts the reading away from “actor with its own established weight” and toward “actor building legitimacy through proximity, echo, and public validation.”
The recurrence of those references makes Morningstar look less like a self-sufficient actor and more like a profile in a phase of legitimacy-building inside a field of uneven alliances. Its present relevance seems to come from a fairly specific combination of demonstrative access and a persistent search for validation through closeness to more established names in the ecosystem. There is no need to exaggerate this or present it as formal dependency. But there is no reason to blur it either. The asymmetry is visible: Morningstar looks upward, invokes, thanks, forwards, and leans on actors with greater reputational capital in order to reinforce its own position.
An assessment informed by HUMINT and cross-checked against public observables reinforces that reading. Morningstar does not present itself as a central or dominant actor, but as a still-young participant within the ecosystem, focused on “intelligent systems and devices,” willing to share part of the information it obtains with allies, and strongly invested in trust, mutual support, and practical usefulness within alliances. In that self-description, names such as Z-Pentest Alliance, PalachPro, APT Babushka, and NoName057(16) appear as relevant reference points in its environment. That does not confirm hard operational coordination, shared infrastructure, or a stable hierarchical architecture. What it does suggest is that Morningstar wants to be read as more than an isolated label. It wants to be seen as part of a network of useful, recognized, and ideologically compatible actors.
Morningstar and its visible relational environment. Relational map of Morningstar within the pro-Russian hacktivist ecosystem as tracked by iQBlack. The visualization reflects observed relationships, affinities, cross-references, or analytical associations, and does not by itself imply uniform operational coordination or equivalent structural dependence across all represented nodes.
It is important to distinguish between ideological affinity, tactical cooperation, and sustained operational coordination, because they do not describe the same kind of relationship. The public celebration of an alliance does not, by itself, demonstrate shared command, technical integration, or structural dependence. That caution matters because in these environments, cross-mentions, forwards, public thanks, and alliance announcements are part of the ecosystem’s own reputational economy. They help shape perception, raise status, extend reach, and organize affinities. Not every visible tie should be read as hard coordination.
At the same time, it would not be serious to strip those signals of analytical value. If one actor repeatedly mentions another, forwards its content, thanks it for media support, and even frames itself as a learner or useful ally, that relationship cannot be dismissed as decoration. The most prudent reading is to describe it as a form of reputational and functional proximity in which Morningstar appears to seek legitimacy, framing, and visibility through a more heavily weighted actor. That does not prove subordination. But it does show a clear direction of symbolic dependence.
That same pattern helps place Morningstar against other names in the environment. If public validation in the reverse direction does not appear with equal intensity, while Morningstar continues to mention and recycle part of the activity or narrative of more visible actors, the asymmetry becomes harder to ignore. The observable pattern suggests an uneven recognition dynamic in which Morningstar frequently invokes actors with greater reputational capital without receiving the same level of public reciprocity.
That pattern is also reflected in the way the actor communicates its own access. Target selection does not appear aimed only at obtaining access, but at obtaining access that can be shown. Cameras, surveillance environments, streets, commercial venues, public-facing spaces, and systems easily converted into screenshots or video fit neatly into that logic. When elements closer to ICS or SCADA appear, in several cases they do so in a context where Z-Pentest Alliance is strongly present, whether through forwarding, explicit reference, or openly stated inspiration. That suggests Morningstar is trying to move closer to a more technically dense aesthetic, while still maintaining a public identity heavily grounded in visibility and association with others.
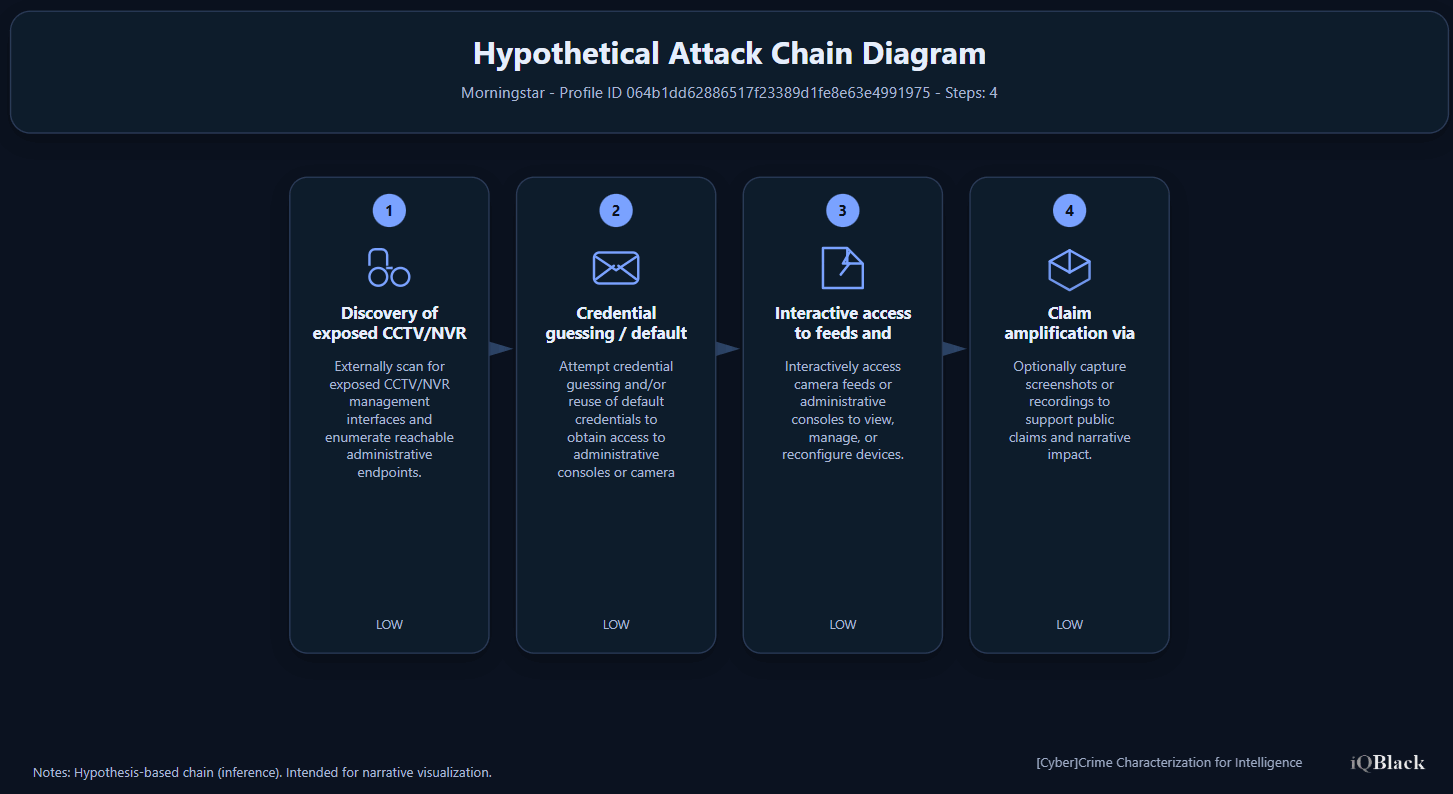
Most plausible operational chain behind Morningstar’s visible-access activity. Analytical hypothesis of the most plausible operating sequence behind Morningstar’s CCTV/NVR- and exposed-system–oriented activity. The sequence illustrates a reasonable model based on the available evidence, but it does not represent a confirmed forensic reconstruction of all incidents attributed to the actor.
In that sense, Morningstar matters less for what it can already prove about itself than for what it reveals about the ecosystem it is trying to belong to. It shows that in certain pro-Russian hacktivist spaces, status is built not only through action, but through being seen acting, being recognized by certain nodes, and knowing how to insert oneself into cycles of content, propaganda, and mutual support. It also shows that smaller actors can gain traction if they find a useful point of entry: visible access, narrative echo, and proximity to actors with greater weight.
Based on the evidence currently available, Morningstar appears to fit better as an active actor in a phase of legitimacy-building than as a central piece of pro-Russian hacktivism. Its apparent utility seems to rest less on exceptional technical maturity than on its ability to produce demonstrative access, speak the language of the environment, join propaganda cycles, and seek public validation through proximity to actors with greater reputational capital. That reading does not prove the actor lacks capability. It suggests something else. It suggests that its current weight appears to lie more in symbolic and communicational integration than in already consolidated operational centrality.
And that is probably the main value of watching it early. Morningstar is not yet a necessary reference point in pro-Russian hacktivism. But it may already be a useful reference for understanding how certain smaller actors try to become one.
Characterization:
3C-INT "Morningstar" ID: 064b1dd62886517f23389d1fe8e63e4991975
Explore 3C-INT
Expand actor, campaign and operational-link tracking through a structured intelligence layer.
Get new publications
Subscribe to receive new articles and public updates from iQBlack without unnecessary noise.