When iQBlack first analyzed Chronus Team, the Argentine dimension of the case was still in a phase of threat projection. The group had already shown increasingly visible activity against public-sector entities in Mexico and had begun to leave signs of expansion toward Argentina through its public messaging, exposure style, and at least one preserved defacement incident involving a municipal portal. At that stage, caution was essential: a public threat does not, by itself, amount to a confirmed intrusion.
That principle still holds. But the state of the case has changed.
The emergence of material publicly associated with the Chronus ecosystem in connection with Argentine institutions significantly alters the analytical reading of the case. Argentina no longer appears merely as a named target within a narrative of intimidation or regional expansion. It has become an active theater of public release and pressure. That shift matters. In intelligence terms, the difference between announcing and materializing affects how an actor’s operational credibility should be assessed.
The first step is to separate, as clearly as possible, what can be stated with confidence from what still requires restraint.
At this stage, it is reasonable to state that Chronus Team had already built a visible trajectory of targeting public institutions, with a strong concentration in Mexico and an operational model centered on exposure, humiliation, and reputational pressure. It is also reasonable to state that, in the Argentine phase, the case evolved from public threat messaging into the release of material purportedly linked to multiple institutions. That transition raises the analytical weight of the case and makes future public threats issued by the group or its ecosystem more relevant from a monitoring and early-warning perspective.
What still cannot be stated uniformly, at least not across every case, is that each published dataset necessarily corresponds to a recent, deep, and directly executed intrusion by the alias presenting it. That distinction is not technical hair-splitting. It is central. In leak, hacktivist, and doxing-oriented ecosystems, published material may come from very different sources: direct access, credential abuse, opportunistic exploitation of exposed systems, reuse of previously obtained data, aggregation of already compromised datasets, or mixed provenance. Treating every release as a fresh original intrusion would be a mistake. But dismissing everything as theatrics would be equally flawed.
That is precisely where one of the main analytical changes emerges: Chronus’ signaling has gained credibility.
Until now, the group’s threats against Argentina could reasonably be interpreted under several scenarios. One possibility was that Chronus had sufficient access or material to support a high-impact release. Another was that it was overstating its capabilities in order to amplify its brand, pressure institutions, and gain regional visibility. The materialization of releases associated with its ecosystem narrows the room for reading the case as propaganda alone. It does not remove the need to verify each claim independently, but it does require acknowledging that the group—or, more precisely, its operational space—has succeeded in converting threat into public-impact activity.
That does not automatically turn Chronus Team into a technically sophisticated actor or a tightly centralized structure. In fact, the available evidence continues to point in a different direction, one that is also more typical of the regional threat landscape: an operational brand or semi-decentralized cluster in which different aliases appear attached to specific releases, discrete campaigns, or partially overlapping narrative spaces. That reading was already present in iQBlack’s earlier assessment and the newer material reinforces it. More than a monolithic organization, Chronus appears to function as an ecosystem of operators converging under a shared identity when the propaganda or pressure value of a case is high enough.
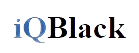
Relational map of aliases and nodes associated with the Chronus ecosystem as tracked by iQBlack. The visualization reflects observed or analytically associated relationships and does not, by itself, imply confirmed operational hierarchy.
It also matters to look at who is being targeted.
The set of Argentine institutions reportedly affected or named does not appear random. Health, education, security, justice, public finance, insurance, and government structures together form a target set with high symbolic, institutional, and reputational value. These are not just data-rich environments. They are environments capable of generating a broader narrative of state fragility, institutional weakness, or failure to safeguard sensitive information. In other words, the leak does not merely seek to expose data. It seeks to expose weakness.
That point is important because it moves the case beyond a purely technical frame. What is at stake here is not only whether exfiltration occurred, how recent it was, how deep access may have gone, or which access vector was used. What is also at stake is the strategic use of publication as an instrument of public pressure. Once an actor succeeds in inserting into the public conversation the possibility that it has accessed information from sensitive state institutions, reputational harm begins before any definitive forensic validation is available. It begins when institutions are forced to deny, explain, qualify, or remain silent while the attacker dominates the narrative with a simple and effective message: we got in, we have data, and we may do it again.
In this kind of scenario, the partial age of the material does not necessarily neutralize its strategic value. Data that is not entirely fresh, incomplete archives, or datasets of mixed provenance may still be highly effective for intimidation, access demonstration, media capture, and erosion of public trust. The impact of a release depends not only on novelty, but also on its ability to alter perceptions of security and institutional control. Reasonable analytical inference: even if some of the material did not stem from recent compromise, it could still serve the actor’s broader strategy of exposure and pressure. That inference is supported by the group’s prior pattern, by the centrality of propaganda to its operating model, and by similar regional hack-and-leak dynamics.
Another issue that still requires caution is persistence.
With the information currently available, it would not be professional to claim that Chronus retains active or sustained access across all the Argentine institutions mentioned. But there is also not enough basis to rule that out in every case. Some incidents of this kind follow an enter-collect-exit logic. Others involve longer access windows. Still others depend on repurposed material previously obtained by the same actor or by third parties. For now, the most disciplined approach is not to force a single explanation onto all the reported targets. Reasonable analytical inference: the observed behavior is more consistent with an opportunistic, modular, and access-capitalizing logic than with a uniform campaign of quiet, long-term persistence.
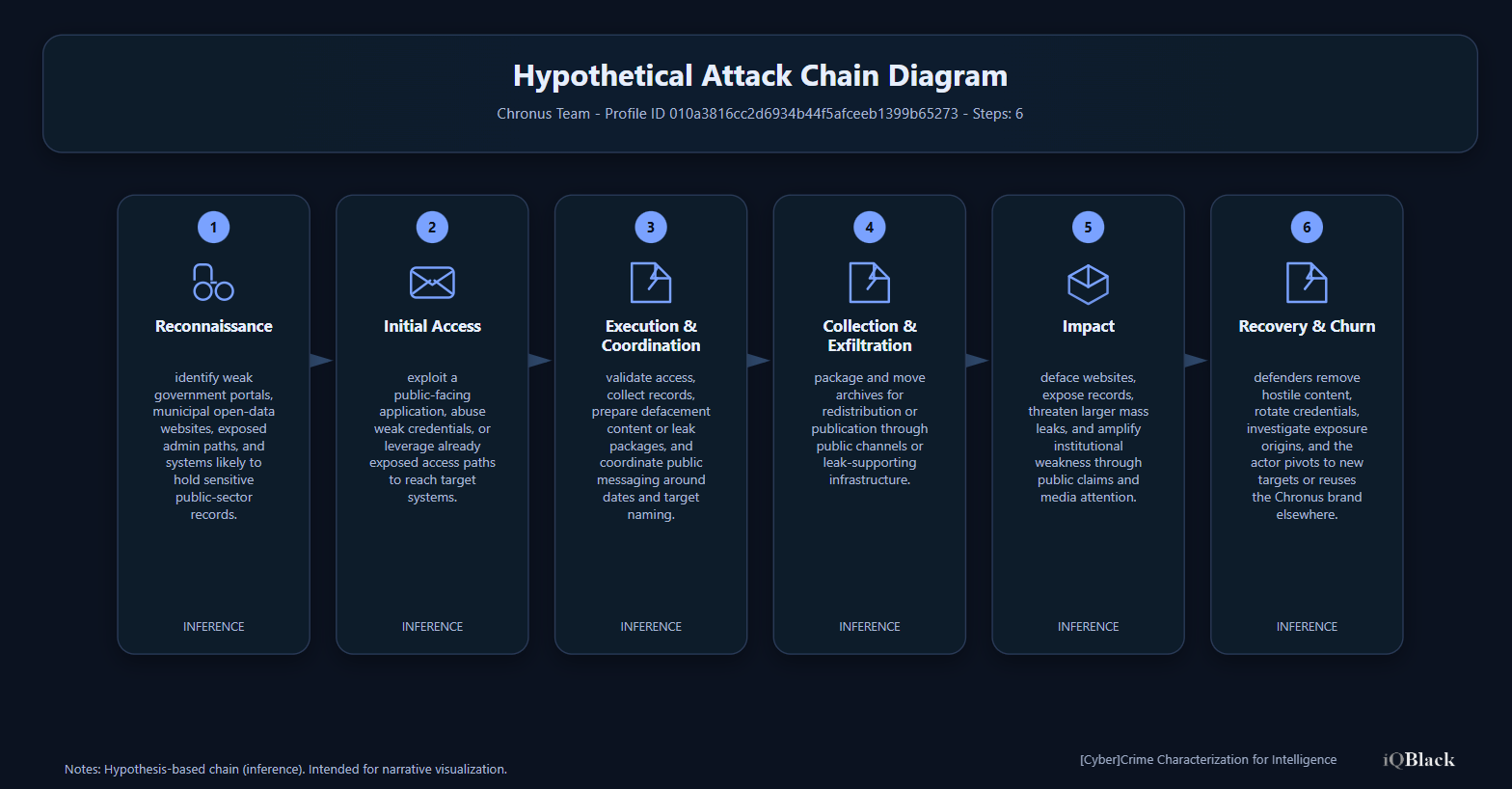
Analytical hypothesis of an attack chain attributable to the observed mode of operation of Chronus Team and its ecosystem. The sequence illustrates a reasonable operating model based on the available evidence, but does not represent a confirmed forensic reconstruction of all incidents.
In Argentina, this kind of operation also lands in a particularly sensitive environment. The combination of high digital adoption, persistent economic stress, strong dependence on fast communication channels, and a relationship that is often fragile between citizens and public institutions increases the impact of this type of publication. In that context, the exposure of data—or even the credible possibility of exposure—does not affect only the institutions directly involved. It also affects public trust, perceptions of state resilience, and the sense of control over systems handling socially sensitive information.
For that reason, what happened in this new phase of the Chronus case should not be read solely as a cybersecurity episode. It should also be read as an event of institutional pressure and strategic signaling.
Chronus Team does not need to demonstrate extraordinary sophistication to generate meaningful harm. It only needs something far more accessible and, for many public institutions, far more uncomfortable: the ability to turn opportunistic access, real leaks, repackaged databases, or mixed-provenance material into an effective public narrative of state vulnerability. That is, at present, its main strength.
What it still has not demonstrated—and should not be overstated—is a uniform capability for advanced intrusion across every target it invokes. Nor has it demonstrated a stable, closed, and fully coordinated structure. But that does not reduce the importance of the case. On the contrary, it shows why actors of uneven technical depth can still be highly disruptive when they understand how to exploit the asymmetry between public exposure, institutional slowness, and the social sensitivity of leaked information.
Analytically, the case is now entering a more demanding phase. The question is no longer whether Chronus Team sought to establish itself in the Argentine conversation. That has already happened. The question is how the official responses already issued by named or affected institutions will hold, evolve, or be refined, what level of independent validation will ultimately be achieved regarding the released material, and whether this phase represents a high-impact one-off operation or the beginning of a more sustained campaign of public exposure against Argentine targets.
Whatever the answer, one fact has already changed: Argentina is no longer merely a promise within the Chronus narrative. It has become an active part of its pressure theater.
References:
- 2026-03-27: Chronus Team: an emerging intrusion-and-leak actor focused on Mexico, with signs of expansion toward Argentina
- 3C-INT: Internal "Preliminary Intelligence".
- 3C-INT: Argentina and Mexico internal "Country Context".
- 3C-INT "Chronus Team" ID: 010a3816cc2d6934b44f5afceeb1399b65273
Explore 3C-INT
Expand actor, campaign and operational-link tracking through a structured intelligence layer.
Get new publications
Subscribe to receive new articles and public updates from iQBlack without unnecessary noise.