Threat Actor Characterization

Chronus Team
ID: 010a3816cc2d6934b44f5afceeb1399b65273| Chronus | Chronus Group | Ch************* | Ch*********** |
| Ch*********** | Ch****************** | Ch********* | Kr********** |
| Te********** | Te********* | Te********** | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
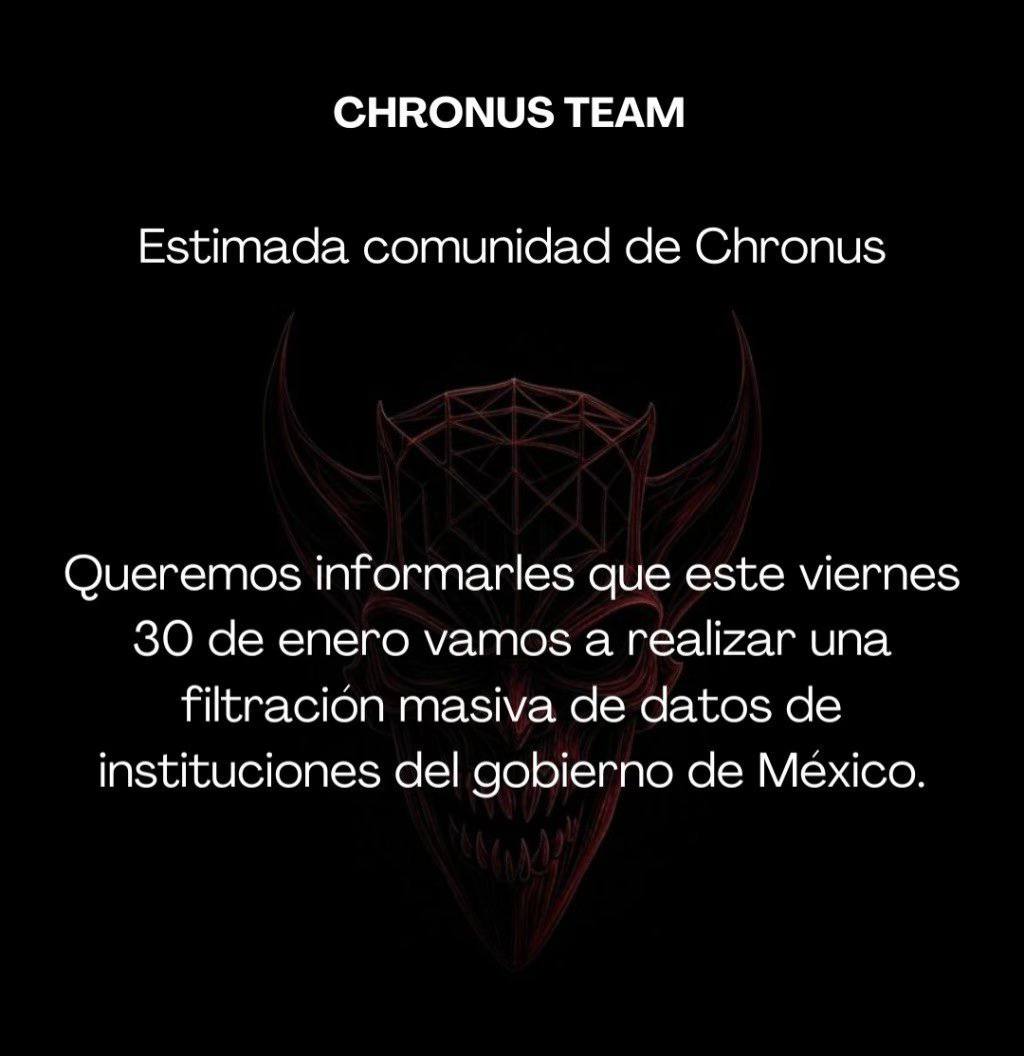
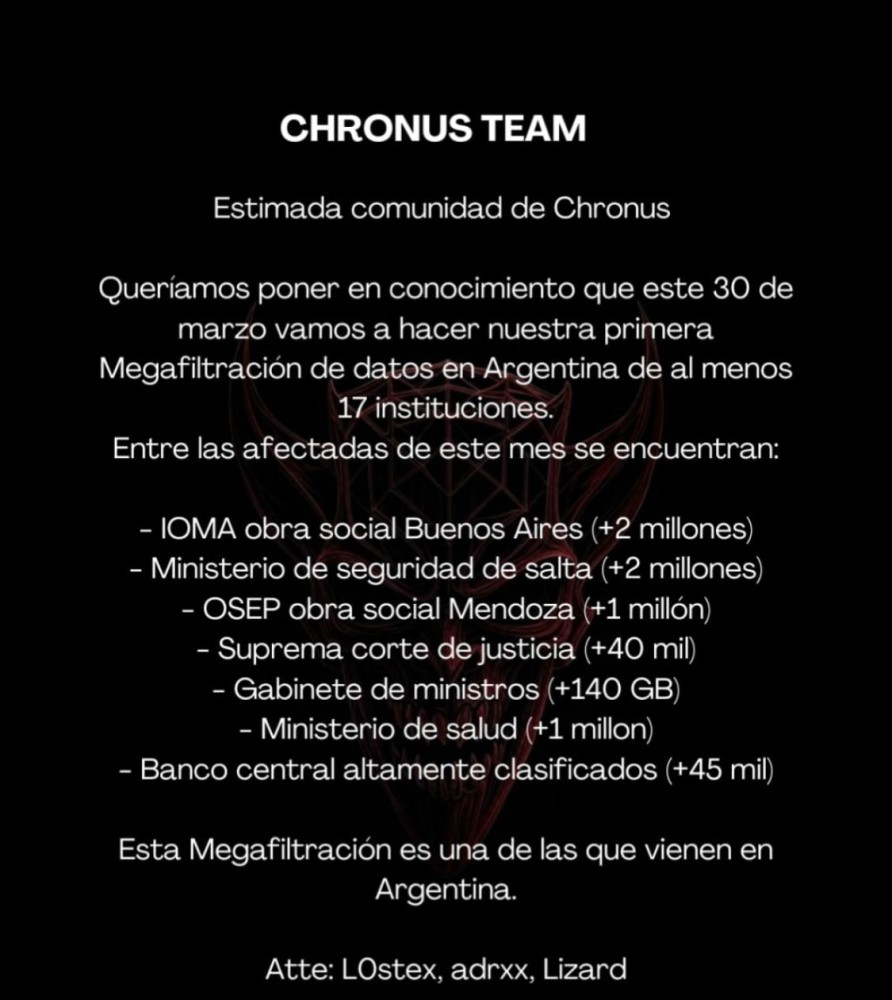
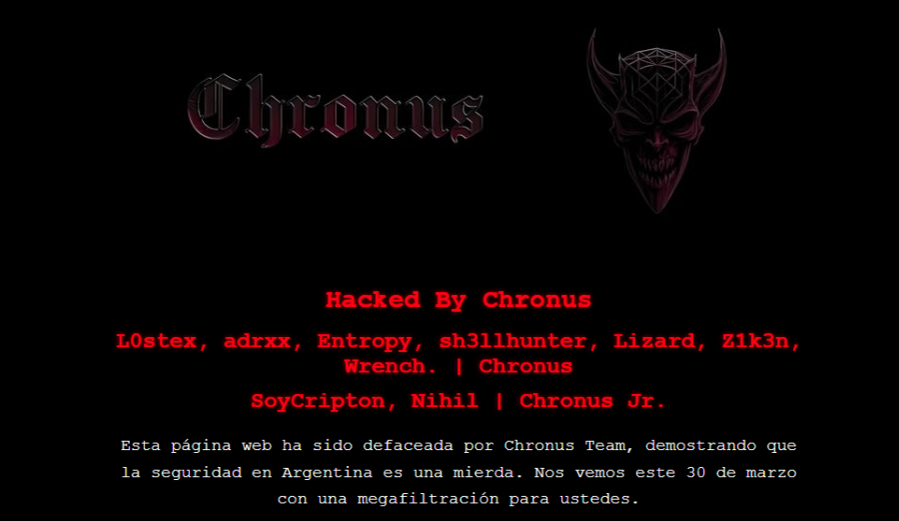
Chronus Team is a Spanish-speaking hacktivist / doxing-oriented cluster linked in public reporting to Mexican public-sector data exposure, public leak threats, and at least one preserved defacement event in Argentina. The actor appears focused on government-facing targets and narrative amplification rather than on a clearly documented advanced malware-led intrusion platform.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1005 | Data from Local System | TA0009 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1567 | Exfiltration Over Web Service | TA0010 |
|
| T1589.001 | Credentials | TA0043 |
|
CHRONUS TEAM — LATAM hacktivist / doxing-oriented cluster
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Hacktivism / Data-leak and defacement cluster — Origin: Assessed Mexico-linked / wider LATAM nexus (INFERENCE, confidence: medium)
Author: iQBlack CTI Team
Executive Summary
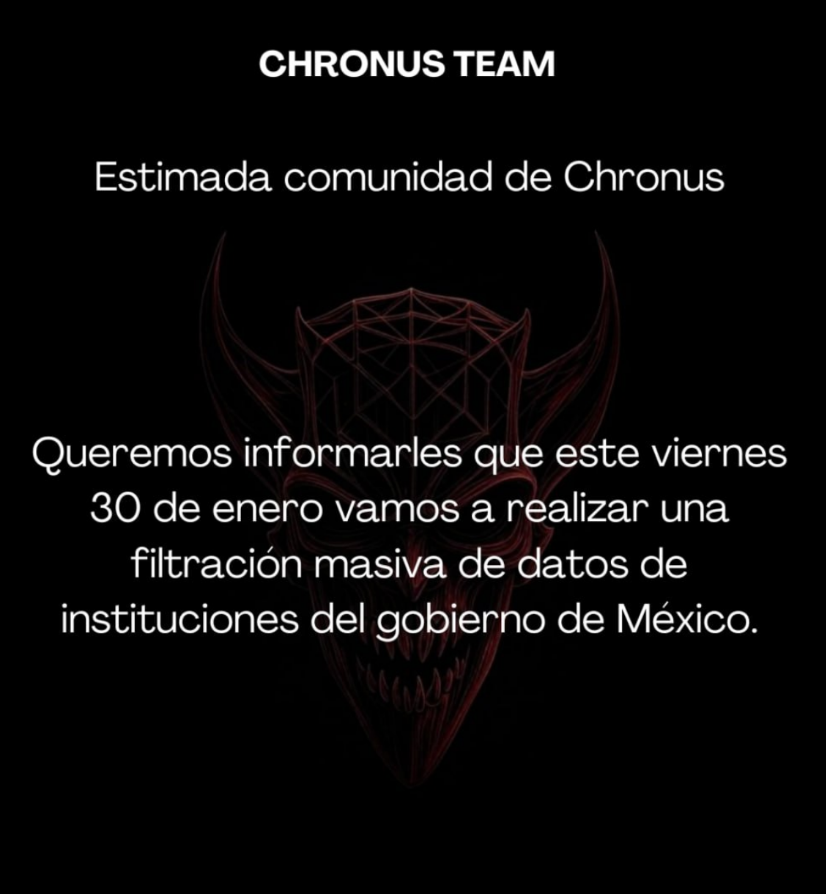
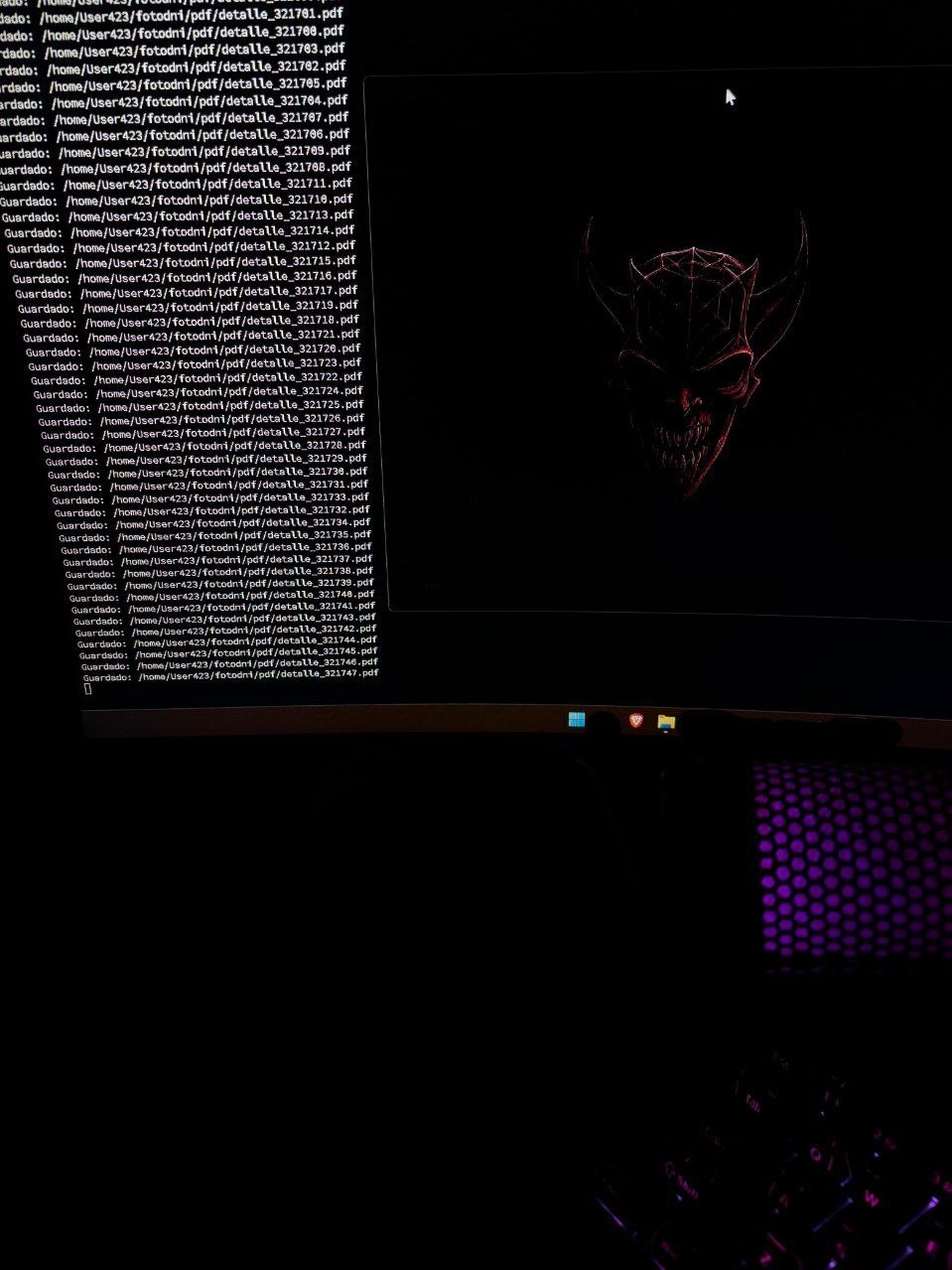
Chronus Team is an emerging Spanish-speaking hacktivist and data-exposure cluster publicly associated with threats, leaks, and defacement activity affecting public-sector entities in Mexico and, more recently, Argentina. Open reporting from late 2025 through March 2026 consistently links the name “Chronus Team” to public leak threats, publication of government-related datasets, and at least one preserved defacement page claiming responsibility for hostile activity against an Argentine municipal open-data portal.
The group’s operational pattern appears centered on publicity, humiliation, and doxing leverage rather than on stealthy long-term access. Public messaging and media coverage indicate a preference for announcing deadlines, threatening “mass leaks,” and amplifying the perceived weakness of government security controls. This is consistent with a hacktivist or notoriety-driven model in which the media effect is part of the operation, not a by-product.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
