In the Latin American threat landscape, not every actor is defined by high-end technical sophistication. Some operate according to a much more direct logic: compromise exposed targets, obtain sensitive information, and amplify the outcome publicly in order to generate reputational, political, and media impact. Within that category, Chronus Team deserves attention.
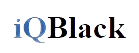
Chronus Team operational profile. Visual overview of the actor including classification, threat types, assessed country of origin, observed areas of operation, and editorial maturity level within the characterization module.
The information collected on this group reveals a consistent pattern. Its known activity is overwhelmingly concentrated on Mexican institutions, many of them tied to government, judicial, healthcare, education, or political environments. This does not appear to be random target selection. The victimology suggests a preference for state-linked or quasi-state targets with high symbolic value and strong potential to expose sensitive records relating to citizens, public employees, taxpayers, students, political affiliates, or beneficiaries of official programs.
That pattern matters because it supports a reasonable analytical conclusion: Chronus Team is, with a high degree of probability, a Mexico-linked or Mexico-based actor, even though this has not been formally claimed by the group itself. The density of cases in Mexico, the temporal continuity of the operations, and the type of targets observed all reinforce that assessment.
So far, activity attributed to Chronus Team and operators associated with its ecosystem includes intrusions with data leaks, website defacements, and, to a lesser extent, doxing. Affected sectors include judicial bodies, health authorities, educational institutions, municipalities, transparency systems, taxpayer-related databases, political affiliation records, and administrative government services. In other words, the group appears to prioritize targets where the public damage and propaganda value of a leak are more important than stealthy persistence or long-term espionage.
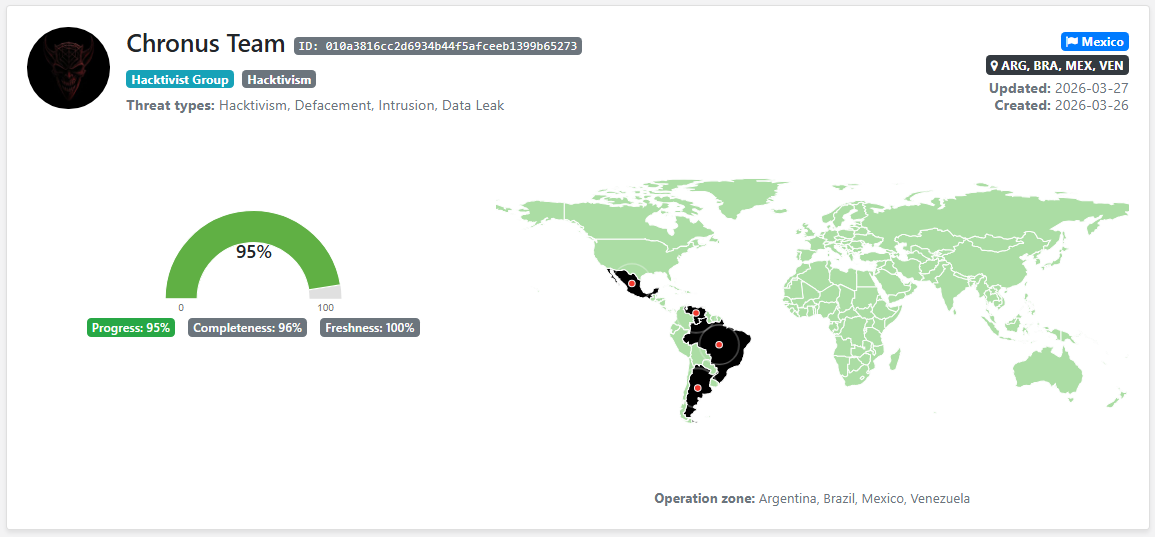
Another relevant characteristic is that Chronus Team does not appear to behave like a rigid, centralized organization, but rather as an operational brand under which multiple aliases conduct actions with varying degrees of visibility. Names such as adrxx, L0stex, SoftVoid, Z1k3n, Sh3llhunter, Wrench, Lizard, and others have been associated with specific incidents. This dynamic suggests a collaborative or semi-decentralized cluster, closer to a shared identity than to a traditional hierarchical structure.
Chronus Team relational ecosystem. Graph view of links between the group’s core, members, former members, associated operators, substructures such as Chronus Jr., and peripheral connections relevant to attribution and internal dynamics analysis.
Within that same context, an interesting derivative has emerged: “Chronus Jr” or “Chronus Juniors.” For now, the most prudent analytical approach is to treat it as a related but distinct unit rather than automatically merging it into the core Chronus Team roster. It shares branding, narrative space, and apparent proximity with active Chronus-linked operators, but there is not yet enough basis to assert a formally unified structure. Blurring both layers without nuance would only weaken attribution quality.
The group’s internal evolution also deserves attention. Recent information indicates that at least three aliases previously linked to the actor may no longer be part of Chronus Team. According to statements attributed to L0stex, the split appears to be rooted in ideological or strategic differences. This matters because, in groups where branding carries as much weight as individuals, membership changes can alter alliances, operational tempo, and target selection.
Beyond Mexico, there are already signals of regional expansion. One member linked to the group, Z1k3n, has been associated with operations in Brazil and Venezuela. An additional website defacement in Argentina has also been observed, placing the country within the group’s operational or at least narrative scope. But the most significant point is this: Chronus Team publicly announced that on March 30 it would carry out a “megaleak” targeting Argentine government institutions, naming organizations such as IOMA, the Ministry of Security of Salta, OSEP Mendoza, the Supreme Court, the Cabinet of Ministers, the Ministry of Health, and the Central Bank among the alleged victims.
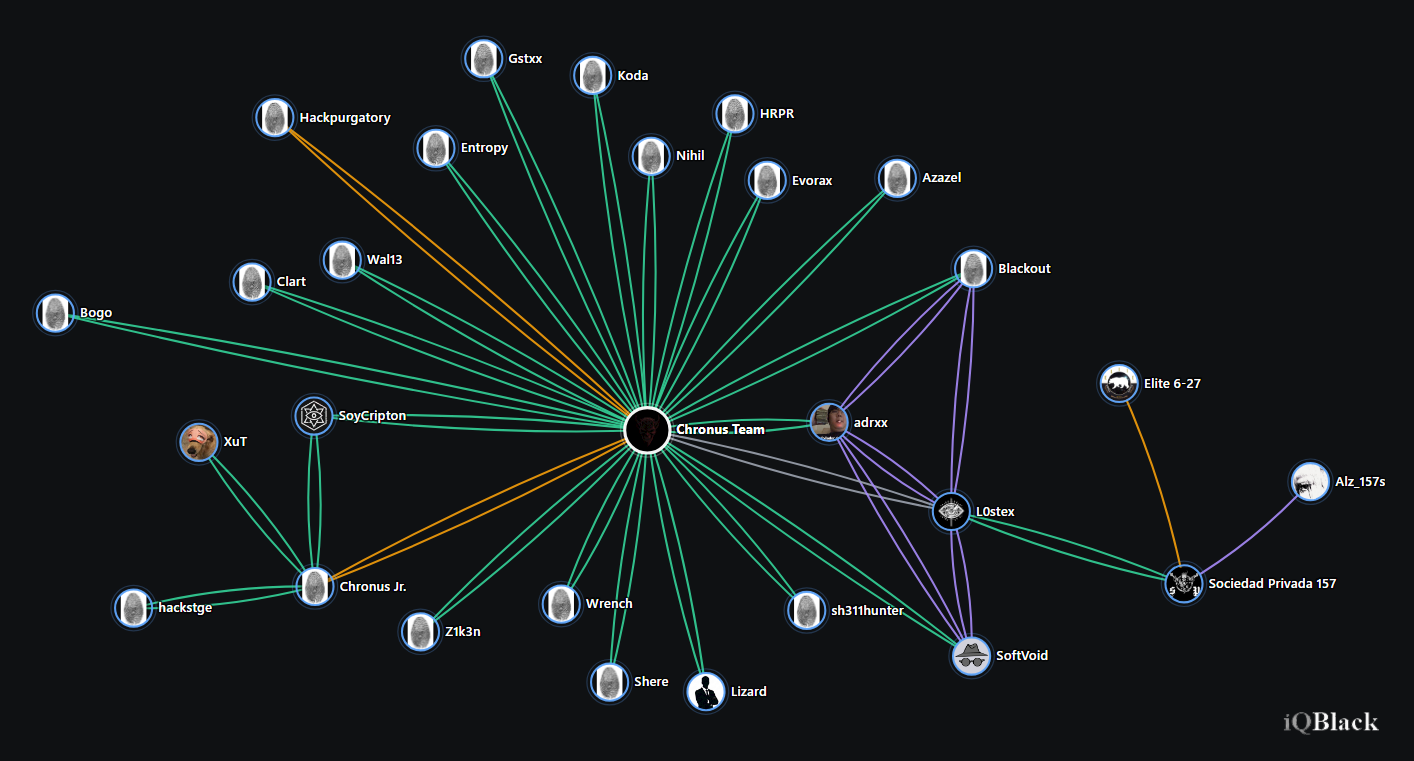
Chronus Team technical mapping. Correlation between observed or inferred techniques and preserved OSINT evidence, including exploitation of public-facing applications, defacement, local data collection, plausible valid-account abuse, and exfiltration for public release.
Resource: Download the Chronus Team Hunting Playbook for practical detection guidance, monitoring considerations, and defensive leads relevant to public-sector and LATAM-focused intrusion-and-leak activity.
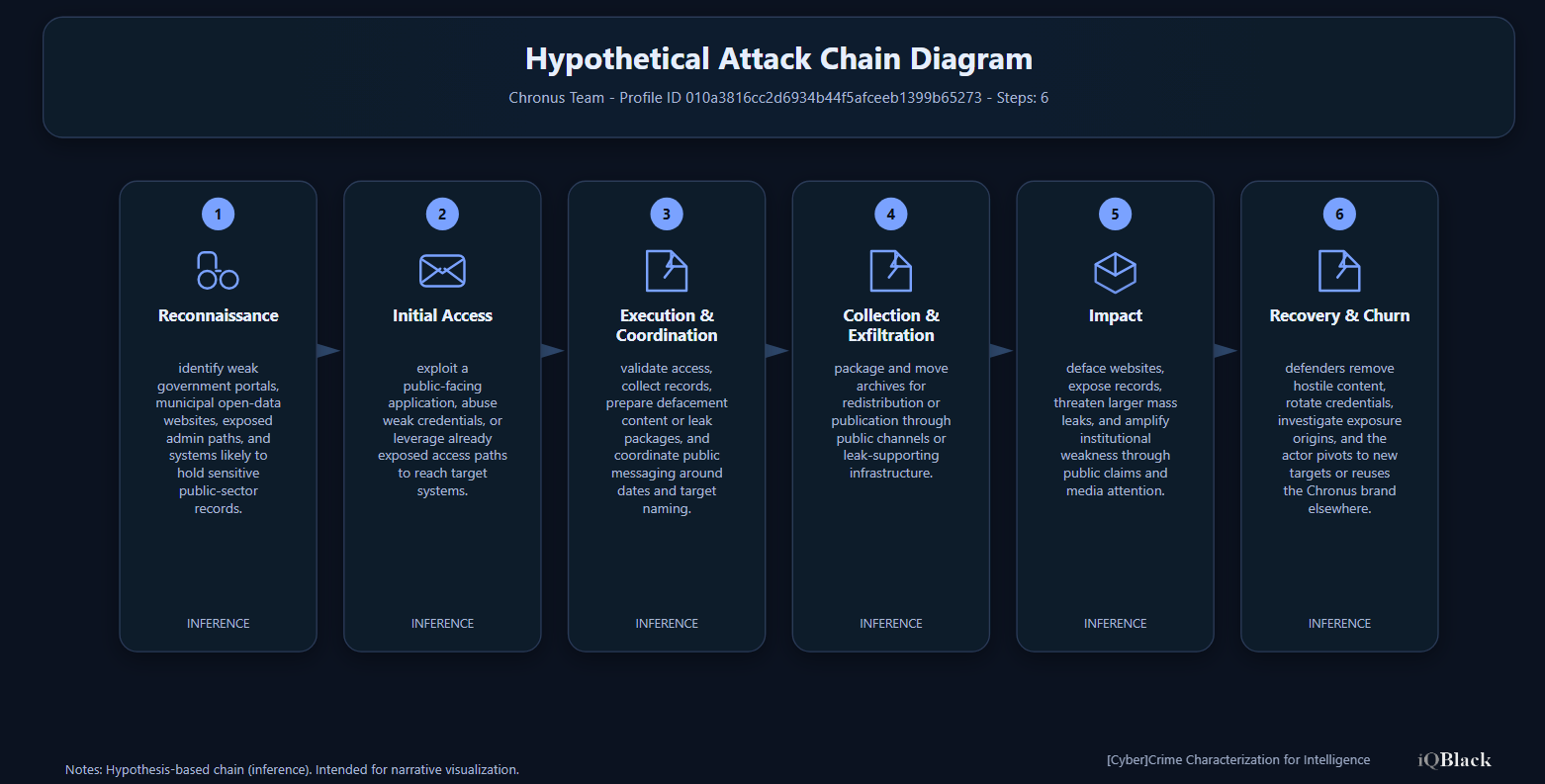
Chronus Team hypothetical attack chain. Inference-based visualization of the actor’s most likely operational flow, from reconnaissance of vulnerable public-facing portals to data leakage, defacement, and pivoting toward new targets under the same brand
That announcement must be treated carefully. It does not amount to a confirmed compromise. In the hacktivist space, public threats also serve a propaganda function. They may precede a real leak, exaggerate capabilities, or simply seek attention before an operation. However, from an intelligence perspective, the value of the announcement does not depend solely on whether it is ultimately fulfilled. Its existence alone already provides useful insight: it reveals intent, thematic prioritization, geographic orientation, and willingness to escalate publicly.
For that reason, the Chronus Team case is relevant even before any new publication materializes. The group represents a particularly uncomfortable threat model for Latin American public-sector institutions: it does not need exceptional sophistication to cause real damage. Reused credentials, exposed services, weak segmentation, poorly administered portals, or weak operational security are often enough to turn opportunistic access into a high-impact public leak.
In state environments, where the exposure surface is often broad and uneven, that model is especially effective. A leak involving health, judicial, educational, or administrative data does not only affect systems; it affects trust, governance, privacy, and institutional credibility.
In that sense, Chronus Team should not be read as an isolated anomaly. It is a symptom. It reflects how regional clusters, with strong digital identity and relatively low-cost operations, can pressure public institutions through intrusion, exposure, and propaganda. Mexico has been its main stage so far. The open question is whether Argentina will be next.
Conclusion
Chronus Team deserves close monitoring. Not because of some extraordinary
sophistication, but because it combines three elements that are often enough to
generate serious impact in the region: symbolic target selection, opportunistic
compromise, and public amplification. In Latin America, that is more than
enough to turn an emerging actor into a serious problem.
Resource: Download the Chronus Team Hunting Playbook for practical detection guidance, monitoring considerations, and defensive leads relevant to public-sector and LATAM-focused intrusion-and-leak activity.
3C-INT "Chronus Team" ID: 010a3816cc2d6934b44f5afceeb1399b65273
Explore 3C-INT
Expand actor, campaign and operational-link tracking through a structured intelligence layer.
Get new publications
Subscribe to receive new articles and public updates from iQBlack without unnecessary noise.