Executive Summary
3C-INT (Cybercrime Characterization for Intelligence) is designed to turn operational data and open sources into structured intelligence on threat actors and criminal ecosystems. Unlike an IOC repository or a generic OSINT tool, it organizes attribution, evidence, TTPs (MITRE ATT&CK®), relationships, and operational context into a living dossier.
The outcome is twofold: a stronger ability to explain “who is who” (defensible attribution) and a stronger ability to act (hunting playbooks and operational guides grounded in strategic intelligence).
Who is 3C-INT for?
3C-INT is built for teams that need to produce and sustain intelligence as an organizational asset, not as isolated documents.
- CTI / Threat Research teams: consistent profiles with evidence and reusable timelines across incidents.
- SOC / Detection Engineering / Threat Hunting: hunting hypotheses and actionable guidance aligned to ATT&CK and real prioritization.
- Incident Response / Crisis Management: attribution and context for internal investigations, third-party coordination, and executive communications.
- Security leadership (CISO / Head of Security): concise executive briefs with implications, risk, priorities, and recommended decisions, without losing traceability.
- Operationally sensitive environments (need-to-know): compartmentalization, restricted access, and role/team-based visibility control.
The problem: signals everywhere, intelligence nowhere
Most organizations already have solid tools to collect indicators and telemetry: EDR, sandboxes, SIEM, commercial feeds, and automation. Yet a structural problem remains: turning that mass of signals into actor, campaign, and ecosystem intelligence that is defensible, reusable, and consumable by different audiences (SOC, CTI, and leadership).
When that bridge doesn’t exist, familiar symptoms show up: inconsistent attributions, fragmented knowledge, reports that age fast, and “resets” every time an actor returns under a new alias or with a slightly different tactic.
What 3C-INT is (and what it is not)
3C-INT is an actor-centric intelligence production platform. Its purpose is to build structured dossiers with traceable evidence, relationships, TTPs, and operational context.
It is not an “infinite IOC dumpster” nor a generic OSINT dashboard. IOCs exist when they add value, but the core of the system is intelligence: defensible attribution, explicit hypotheses, operational narrative, and outputs ready to plug into hunting workflows and decision-making.
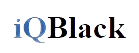
Clear attribution, ready for reporting
Attribution shouldn’t be a paragraph lost in the middle of a report, it should be a consistent, updatable, and traceable block. 3C-INT structures the assessed origin of the actor, geographic coverage, operational categorization, and known aliases in a reusable format for internal or public reporting.
This approach reduces friction on two fronts: it enforces consistency across analysts/teams and simplifies communication to non-technical audiences without sacrificing evidence.
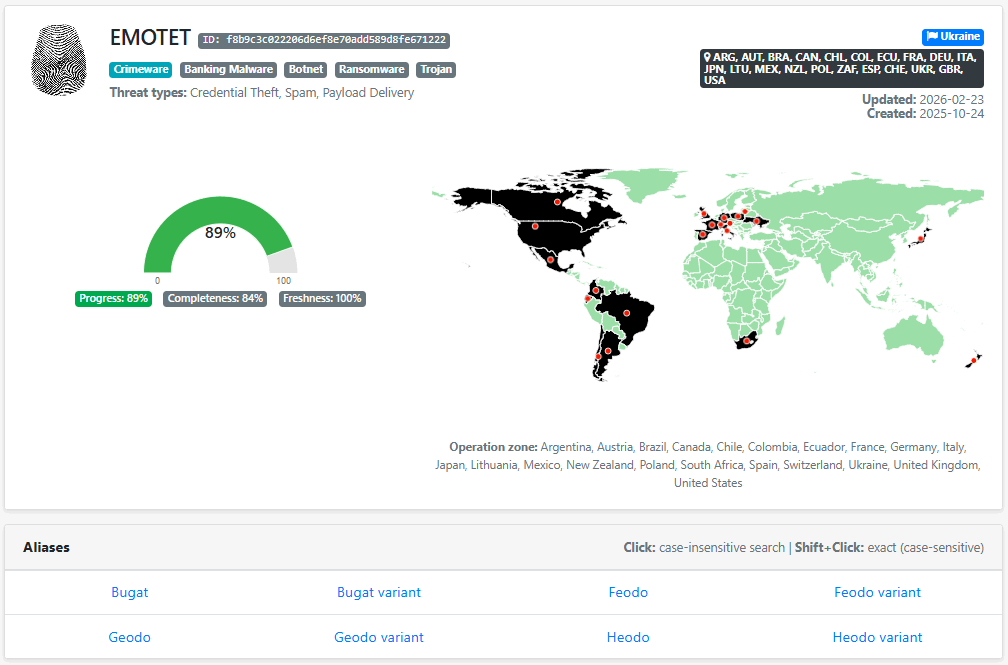
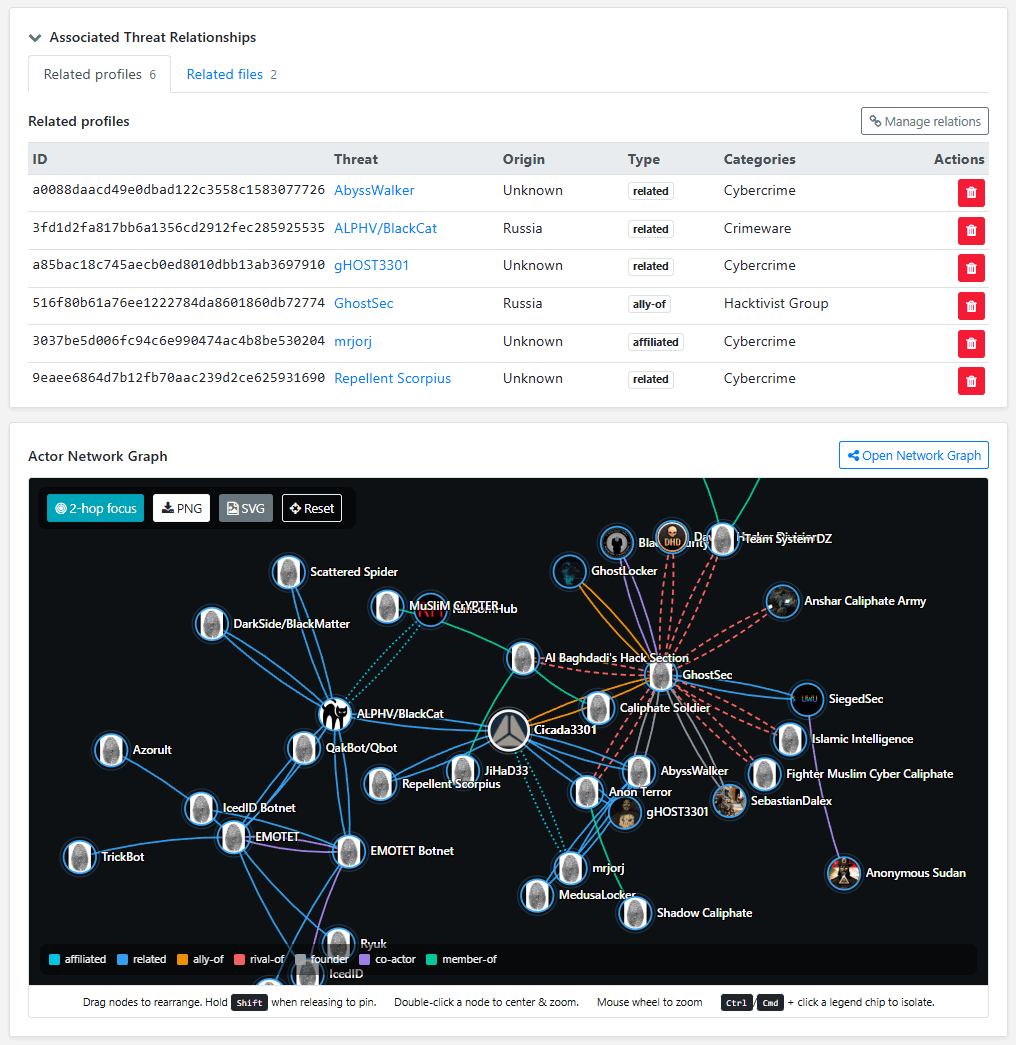
Relationships and pivoting: understanding networks, not just “a name”
Actors don’t operate in a vacuum. A central section lets you pivot across relevant relationships: direct and indirect links to other actors, shared infrastructure, operational ties, or associations that matter for investigation.
This accelerates controlled knowledge expansion: instead of investigating “islands,” you build an ecosystem view.
Network visualization: from implicit context to an exportable graph
The Actor Network Graph materializes relationships into a navigable graph that helps organize nodes and export visuals for reporting. Practically, this prevents network understanding from living only “in the analyst’s head” or in a one-off slide, it becomes part of the dossier.
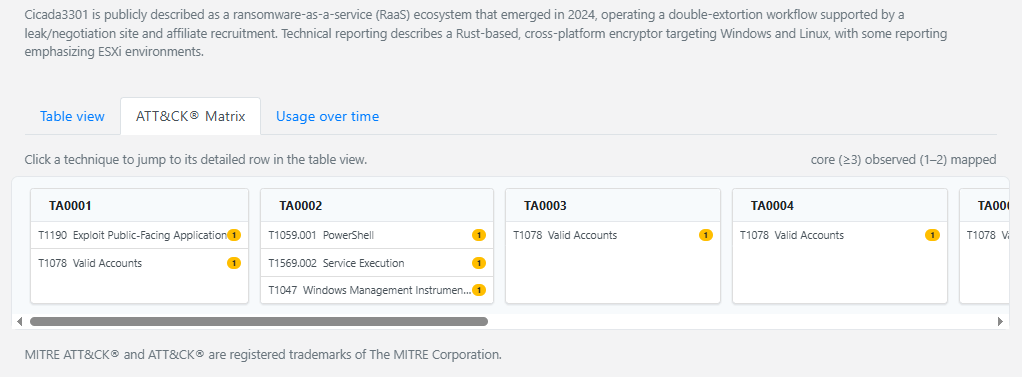
MITRE ATT&CK® with evidence and temporal evolution
MITRE ATT&CK® is useful when it is backed by evidence. 3C-INT links TTP mappings to supporting evidence per technique/tactic. In addition, the “usage over time” view helps track behavioral evolution over time, supporting defense prioritization and distinguishing real changes from “something they once did.”
Preliminary intelligence: explicit hypotheses with confidence levels
Useful strategic intelligence isn’t just listing facts, it’s proposing hypotheses, separating evidence from inference, and assigning confidence.
The Preliminary Intelligence section organizes inferences with confidence and delivers tables/matrices that are ready to integrate into recurring reporting, reducing repetitive work and improving consistency.
From strategic to actionable: executive brief and hunting playbook
Intelligence only creates value when it changes decisions and improves outcomes. In practice, that means producing outputs that serve two very different audiences: leaders who need clarity and prioritization, and operators who need precise, testable actions. 3C-INT operationalizes strategic intelligence through two complementary formats.
- Executive Analyst Brief: A leadership-oriented summary built to support timely decisions. It distills what matters now: likely impact, affected business processes, current threat posture, and recommended prioritization across prevention, detection, and response. The goal is not to “inform,” but to drive action—aligning security priorities with business risk, resource allocation, and continuity requirements.
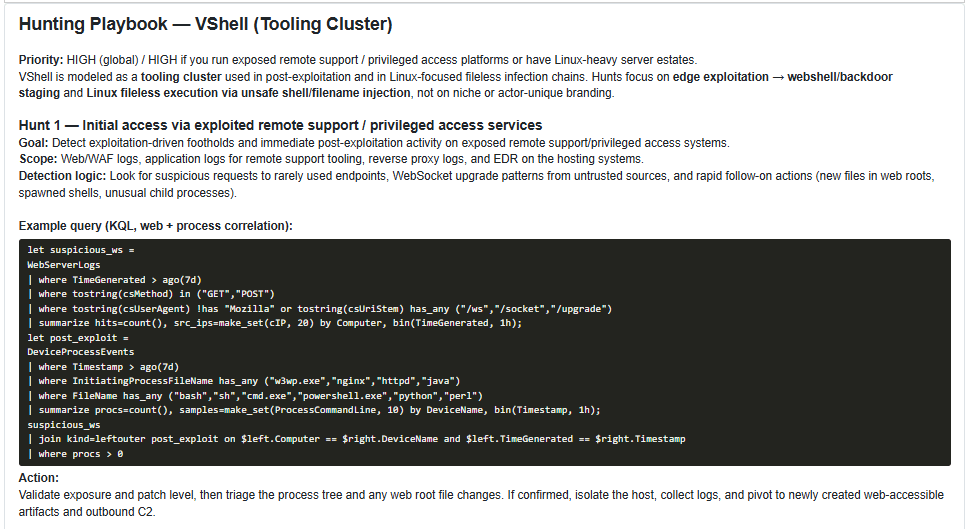
- Hunting Playbook: The Hunting Playbook is where strategic intelligence becomes operational advantage. It translates actor- and campaign-level understanding—TTPs, patterns, and observed evolution—into structured hunting guidance and detection-ready content aligned to MITRE ATT&CK®. This includes actionable hypotheses, investigative steps, and rules or query templates (KQL for Microsoft Sentinel/Defender, Splunk SPL, Elastic/Kibana, and other common stacks), designed to plug into existing threat hunting and detection engineering workflows.
Most organizations already have telemetry. The differentiator is how fast they can convert that telemetry into proactive detection and prevention. The Hunting Playbook extends the “window of proactivity” by allowing teams to hunt for early-stage behaviors and campaign patterns—often before an incident becomes a business interruption. Instead of reacting to an alert after impact, teams can prioritize high-signal behaviors tied to relevant adversaries, validate coverage gaps, and deploy detections that map to real-world tradecraft.
Operational value in concrete terms
- Faster transition from intel to action: reduce time from “new actor insight” to deployed hunts/detections.
- Better prioritization: focus on behaviors and techniques that matter for your environment, not generic checklists.
- Defendable detection strategy: detections and hunts are anchored to evidence and ATT&CK mapping, improving governance and auditability.
- Detection engineering alignment: playbooks help transform hunting discoveries into durable detections and continuous monitoring.
- Business continuity impact: by increasing early visibility and reducing dwell time, the playbook supports resilience and lowers the probability that threats escalate into disruptive events.
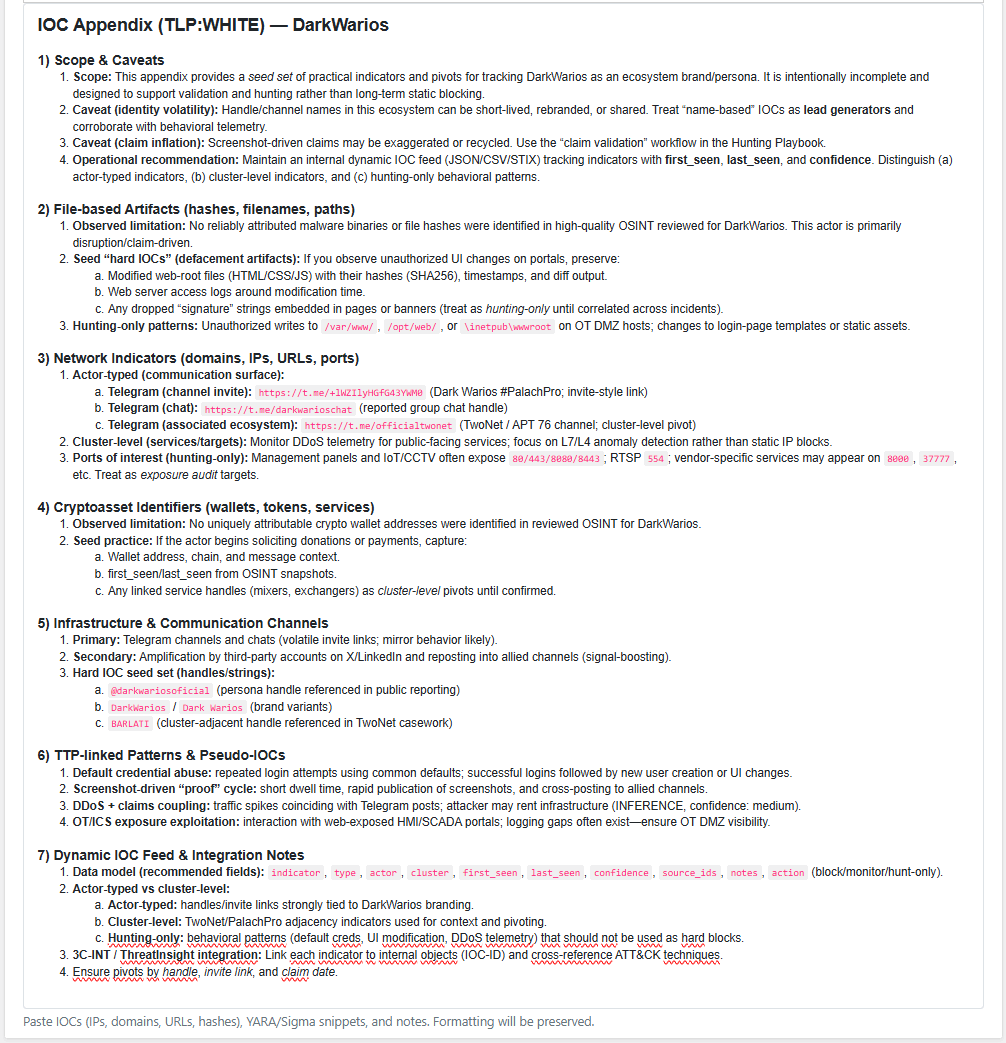
IOC Appendix: seed set + live feed (instead of eternal PDFs)
In 3C-INT, indicators are treated as an operational resource, not a static attachment. The IOC Appendix prioritizes a strategic-operational framework and, when appropriate, a small set of “hard” IOCs as a seed set.
For volatile elements (temporary infrastructure, per-victim wallets, rotating domains), the recommended model is a dynamic internal feed with first_seen, last_seen, and confidence. This provides immediate value to SOC/IR without creating dependency on stale appendices.
Compartmentalization and access control: intelligence on a need-to-know basis
Many organizations need to produce intelligence privately and selectively. Threat intelligence is often sensitive by default. Even when the underlying sources are public, the analysis, hypotheses, investigative direction, and internal linkages can expose capabilities, priorities, relationships, and ongoing cases. For many organizations, the limiting factor isn’t collecting data—it’s controlling who can see what, when, and why.
3C-INT is built to support compartmentalized intelligence workflows through role- and team-based access control, allowing organizations to run need-to-know operations without slowing down production or forcing analysts into “shadow documentation” (private notes, local files, side channels).
What this enables in practice
- Private profiles and restricted workspaces: Organizations can maintain profiles that are not discoverable or visible outside designated roles or teams. This is especially relevant for: active investigations, sensitive attribution work, pre-disclosure tracking, and cases involving legal counsel or external partners.
- Separation of duties and controlled collaboration: Different groups can collaborate on the same actor or campaign while controlling exposure of sensitive fields (for example, internal hypotheses, investigative leads, or partner-provided material). This supports “minimum necessary disclosure”: teams can contribute intelligence without broadcasting the most sensitive parts of the record.
- Clean handling of sensitive context (beyond IOCs): Compartmentalization is not just about hiding indicators. The highest-risk content often includes: investigative reasoning, link analysis, internal victimology context, executive assessments, and details about response posture. 3C-INT keeps this context inside governed access boundaries rather than spreading it across emails, spreadsheets, or chat threads.
- Reduced operational risk and internal leakage: Access control lowers the chance of accidental exposure inside the organization—particularly in environments with multiple subsidiaries, mixed contractor access, or rotating staff. Need-to-know controls reduce the blast radius of both mistakes and insider risk scenarios, while still enabling intelligence continuity.
- Auditability and accountability (who accessed what, and when): In mature environments, “who saw what” matters. Compartmentalized workflows become significantly more defensible when access is governed and reviewable—supporting compliance requirements and internal governance, and making post-incident review clearer.
Compartmentalization isn’t a “nice to have”—it’s what allows intelligence programs to scale. Without it, teams tend to fragment into informal silos to protect sensitive work, and the organization loses the benefits of a shared intelligence library. With proper access control, intelligence becomes both reusable and controlled: a structured asset that remains internal, supports decision-making, and can be shared selectively when collaboration is needed.
This capability is particularly valuable for organizations that operate across regions, have multiple teams consuming intelligence (SOC/IR/CTI/leadership), work with external counsel or partners, or maintain investigations that should not be broadly visible across the enterprise.
Where it fits in your current stack
3C-INT does not replace EDR, SIEM, SOAR, or sandboxing—and it doesn’t try to. Those systems are built to collect telemetry, generate alerts, and support response execution. 3C-INT sits above them as the intelligence layer: it turns signals into structured threat profiles and dossiers that can be used to investigate, attribute, prioritize, and communicate consistently across the organization.
In practical terms, this means 3C-INT helps teams move from “we saw something” to “we understand who is behind it, how they operate, what they are likely to do next, and what we should do about it.” It creates a repeatable workflow to ingest and maintain actor and campaign profiles—linking observed behaviors, infrastructure, relationships, and evidence—so investigations don’t restart from scratch each time an adversary reappears with a new alias, a new tool, or a slightly modified technique.
This positioning also improves coordination. Security operations can keep using existing tools for detection and response, while 3C-INT provides the shared context that aligns CTI, SOC, IR, and leadership. The output is not just a narrative report; it’s an intelligence dossier with traceability, timelines, hypotheses, ATT&CK mappings, and operational guidance—ready to support a crisis table, a security committee, partner coordination, or a legal process where defensibility matters.
Additionally, 3C-INT functions as a living intelligence library—not a static “report warehouse.” Profiles evolve over time, preserving investigative decisions and evidence. And because the library is exportable, the organization retains continuity even if external vendors change. In other words, the intelligence produced by the team becomes durable operational ownership: a structured asset that stays internal, accumulates value, and remains reusable regardless of shifting contracts, tooling refreshes, or provider churn.
Conclusion
If your organization already collects strong telemetry and indicators, the next natural step is turning that data into actor intelligence that is consistent, defensible, and actionable. 3C-INT is designed to make that transition systematic: a repeatable production model for ingesting, maintaining, and operationalizing threat profiles—so intelligence doesn’t depend on individual heroics or tribal knowledge.
The end state is straightforward: faster investigations, clearer attribution, better prioritization, and operational outputs that support proactive detection and business continuity. When threat intelligence becomes a maintained library rather than a one-off document, every new case strengthens the organization’s long-term advantage—not just its short-term response.
Key takeaways
- Turns signals (telemetry/IOC/OSINT) into structured actor dossiers with traceability.
- Improves defensible attribution and accelerates actionable outputs (executive briefs + hunting playbooks).
- Preserves intelligence as an organizational asset with role/team-based access control.
3C-INT actor Characterization
- Emotet - (ID f8b9c3c022206d6ef8e70add589d8fe671222)
- Cicada3301 - (ID 11196e28e27f5da7fabf6449326a641101089)
- NoName057(16) - (ID 78dd1c3c3dfc6fcbbda95d743ab0e2f732121)
- DarkWarios - (ID 125c675b998f01a97afbfc3a83d41d1f83490)
- VShell - (ID e2e1fcdd390249b8977a82bb5c948b8684635)
Explore 3C-INT
Expand actor, campaign and operational-link tracking through a structured intelligence layer.
Get new publications
Subscribe to receive new articles and public updates from iQBlack without unnecessary noise.