Pro-Iranian and pro-Russian ecosystems are often read as if they inhabited separate compartments. On one side stands the digital galaxy of the “axis of resistance,” shaped by ideological weight, an anti-Israel focus, and the language of militancy. On the other is the more fluid universe of pro-Russian hacktivism, with campaigns against Ukraine, NATO countries, and other Western targets, operating in a space where propaganda, symbolic coercion, and geopolitical utility coexist. That division still helps organize the map. What it no longer does particularly well is describe the terrain. ENISA noted that Holy League, created in July 2024, brought together pro-Russian and pro-Palestinian groups, including NoName057(16), to target Ukraine, Israel, and countries perceived as allies of both fronts.
Cyber Islamic Resistance becomes especially interesting when viewed from that angle because it shows how two different environments can derive mutual benefit without fully integrating. The issue is not proving an organic fusion between Cyber Islamic Resistance and pro-Russian actors. It is observing that when enemies, timing, and narrative opportunities converge, that proximity begins to generate political and propagandistic effects that are increasingly difficult to dismiss as mere coincidence. Reuters reported this week that a Ukrainian intelligence assessment linked Russian groups such as Z-Pentest Alliance and DDoSia Project with Iranian actors such as Handala Hack in cyber coordination via Telegram, in the context of the recent conflict involving the United States, Israel, and Iran.
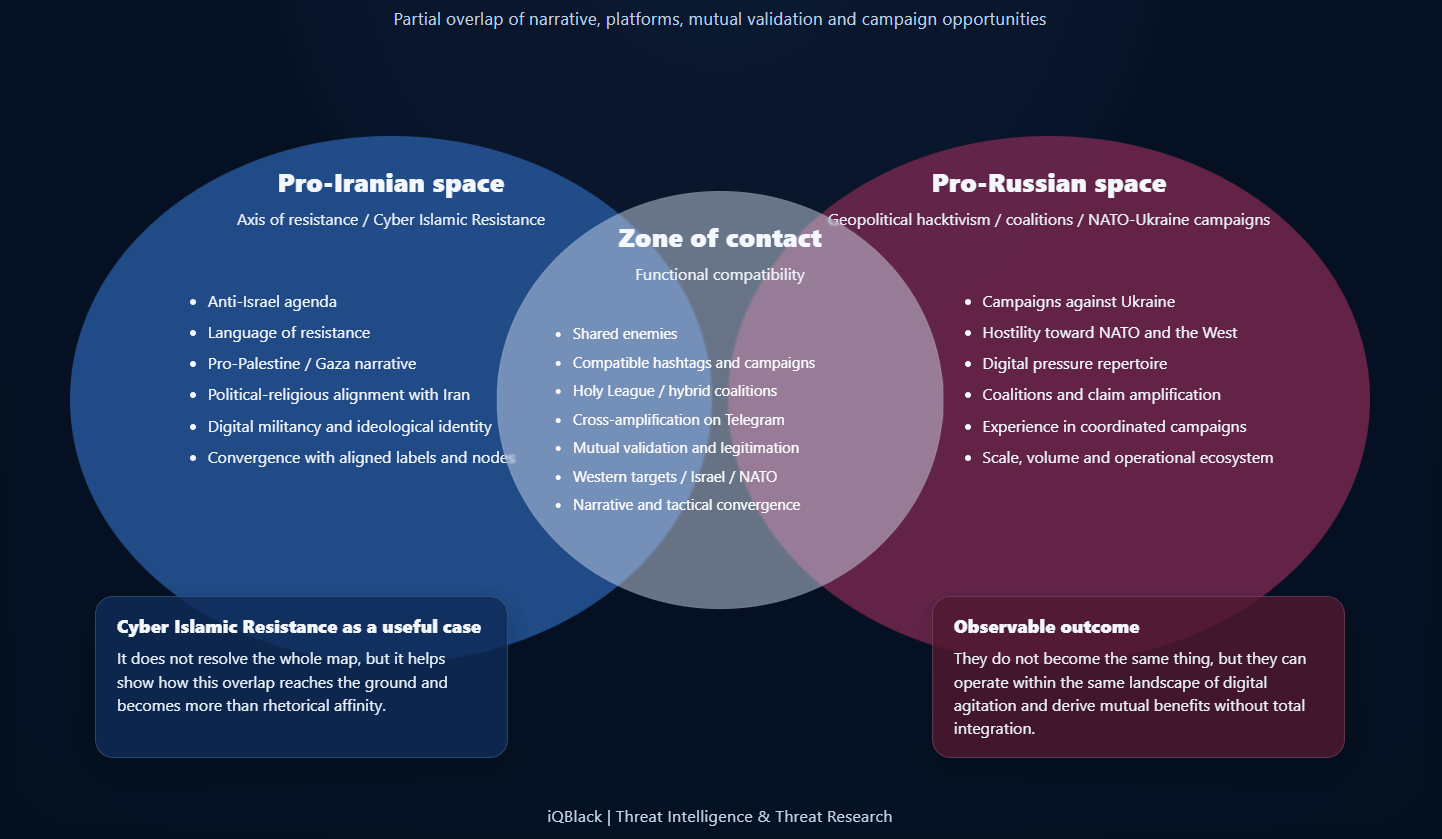
Functional overlap between pro-Iranian and pro-Russian spaces within the landscape of digital agitation. The visualization does not suggest a unified structure, but rather a zone of narrative, tactical, and propagandistic convergence between distinct clusters.
From that perspective, Cyber Islamic Resistance stops being only a case tied to the anti-Israel front. Its public identity grows out of politically and religiously framed resistance language aligned with Iran, and from a narrative sustained around Palestine, Gaza, and confrontation with the West. Yet that same environment has also incorporated visible signs of support for Russia, favorable references to NoName057(16), shared frames against NATO, and an increasingly less marginal coexistence with labels and coalitions in which the pro-Iranian and pro-Russian spheres no longer appear as incompatible spaces. Instead, they begin to behave like fronts that can overlap within the same digital theater. ENISA recorded precisely that mixture in campaigns such as #op_france, #op_italia, #opbelgium, and other coordinated operations carried out under the Holy League umbrella.
What is most revealing is that this convergence does not require formal integration to produce real effects or something denser than simple parallelism. In many cases, shared enemies and a shared agenda are enough. One side contributes legitimacy within the anti-Israel resistance narrative; the other brings ecosystem, scale, repertoire, and experience in digital pressure campaigns against Western targets. Neither side needs to dissolve into the other for that overlap to become useful. ENISA captured this by describing Holy League as an alliance bringing together pro-Russian and pro-Palestinian groups. Reuters went further by placing Russian-Iranian coordination within the same messaging space and within the same expanded conflict environment.
It is still worth avoiding the temptation to throw every layer into the same bag. Not all convergence works in the same way. In some cases it is symbolic: shared enemies or shared geopolitical punishment. In others it takes on a more propagandistic form: narrative recycling and mutual validation across alliances. It can also take on a more tactical tone, with campaigns unfolding in the same period, aligned targets, or informal divisions of labor depending on the moment.
Higher up, though still surrounded by gray areas, there is the possibility of service or support convergence, where tools, infrastructure, or coordination channels begin to overlap. The point is not to claim that Cyber Islamic Resistance currently operates across all of those levels. The point is that the ecosystem around it shows signs that these layers are no longer fully separated. Reuters describes precisely that kind of cyber collaboration between Russian and Iranian groups, while recent private-sector analysis argues that cyber conflict linked to the Iran-Israel confrontation has already spilled beyond the initial theater into third countries and broader networks of geopolitical hacktivism.
The rebellious dimension of hacktivism and the geopolitical implications of this overlap are more serious than they may appear at first glance. When two ecosystems that are usually studied separately begin to share operational frames, the conflict expands. It stops being contained within Gaza, Israel, Ukraine, or NATO as isolated theaters and begins to move within a broader logic, one in which supporting Ukraine can become grounds for punishing a European country, attacking Israel can become compatible with signaling solidarity with Russia, and digital campaigns cease to reflect a single war and instead begin to orbit several at once. ENISA already showed that Holy League articulated attacks against Israel, Ukraine, and countries aligned with NATO. Reuters, for its part, placed that dynamic on an even more sensitive level by linking Russian-Iranian cyber collaboration to the open escalation of 2026.
Cyber Islamic Resistance is especially useful as a case of analysis because it does not claim to solve the alliance map on its own, yet it does reveal how that overlap works once it reaches the ground. It can be seen in the combination of alliances and in the ease with which an anti-Israel agenda can coexist with pro-Russian frames without apparent friction. It can also be seen in something more subtle: the naturalness with which certain actors stop treating one another as outsiders once they realize they share enemies.
That, in the end, is the value of the analysis. Not because it definitively settles the question of a merger between pro-Iranian and pro-Russian environments, but because it makes it possible to see how two worlds that analysis usually keeps apart begin to become functionally compatible when war and shared enemies push them toward each other.
Methodological note: This analysis is based on internal profiling inputs developed at 3C-INT on the hacktivist ecosystem associated with Cyber Islamic Resistance and pro-Russian groups.
Explore 2C-INT
Go deeper into criminal, extremist and hybrid structures through an intelligence environment built around context.
Get new publications
Subscribe to receive new articles and public updates from iQBlack without unnecessary noise.