Executive Summary
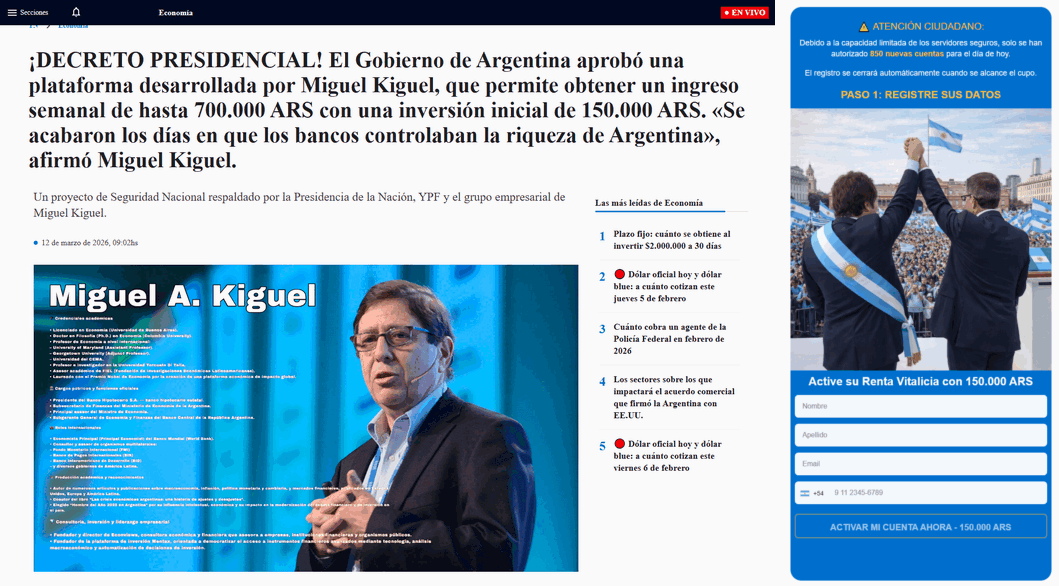
The “Swap Adipex AI” cases analyzed so far do not show classic browser-side malware behavior. Instead, they reveal a structured investment scam funnel that combines bridge pages, fake-news themed landing pages, advertising attribution logic, form-based lead capture, and rapid telephone follow-up.
The web component appears designed not to exploit the victim’s device, but to exploit the victim’s trust. The observed chain aligns closely with documented patterns seen in deceptive affiliate marketing ecosystems, fake celebrity / fake-news investment scams, and call-center driven fraud operations. In practical terms, this is best understood as fraud infrastructure, not as a conventional malware case.
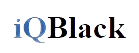
News-style deception page using political imagery, economic framing, and direct lead capture to support a downstream fraud workflow.
What was analyzed
This assessment is based on two HTML samples directly reviewed, a broader cluster of related domains and redirect chains, and post-submission operational behavior observed after form completion. The two reviewed pages serve different roles within the same flow.
The first is a long Spanish-language landing page styled as a news article, using public figures, national institutions, fabricated social proof, and a registration form posting to api.php. The second is a minimal bridge page whose role is to preserve campaign parameters, load TikTok Pixel logic, and forward the visitor to the next stage without losing attribution.
Together, both pages illustrate the two core layers of the operation: conversion infrastructure and trust fabrication.
Why this matters
Cases like this often fall into an awkward blind spot. They do not always trigger the same level of attention as phishing kits or browser-delivered malware, because their primary objective is different. Rather than stealing credentials on the spot or dropping a payload, they aim to qualify a victim and hand that person off to a downstream fraud workflow.
This distinction matters for threat research. If analysts focus only on malicious JavaScript, browser exploitation, or malware delivery, this kind of infrastructure may look relatively benign. If the focus shifts to the full victimization chain, however, the fraudulent intent becomes much clearer.
Working nomenclature
At the current stage, there is not enough evidence to attribute this activity to a named threat actor or criminal brand with confidence. The most accurate way to track it is as a cluster rather than an actor profile.
A practical working designation is: Fake-News Investment Funnel Cluster – Swap Adipex Theme
This naming keeps the focus on the observable circuit: a recurring investment lure theme, a fake-news style wrapper, and a technically consistent funnel architecture.
Observed funnel architecture
The currently observed chain can be summarized as follows:
This is not a trivial distinction. The scam is not concentrated in one page or one script. Instead, different stages perform different jobs. One stage receives and preserves campaign data. Another manufactures legitimacy. Another captures the lead. And the next observed stage appears to move into live, human-driven conversion.
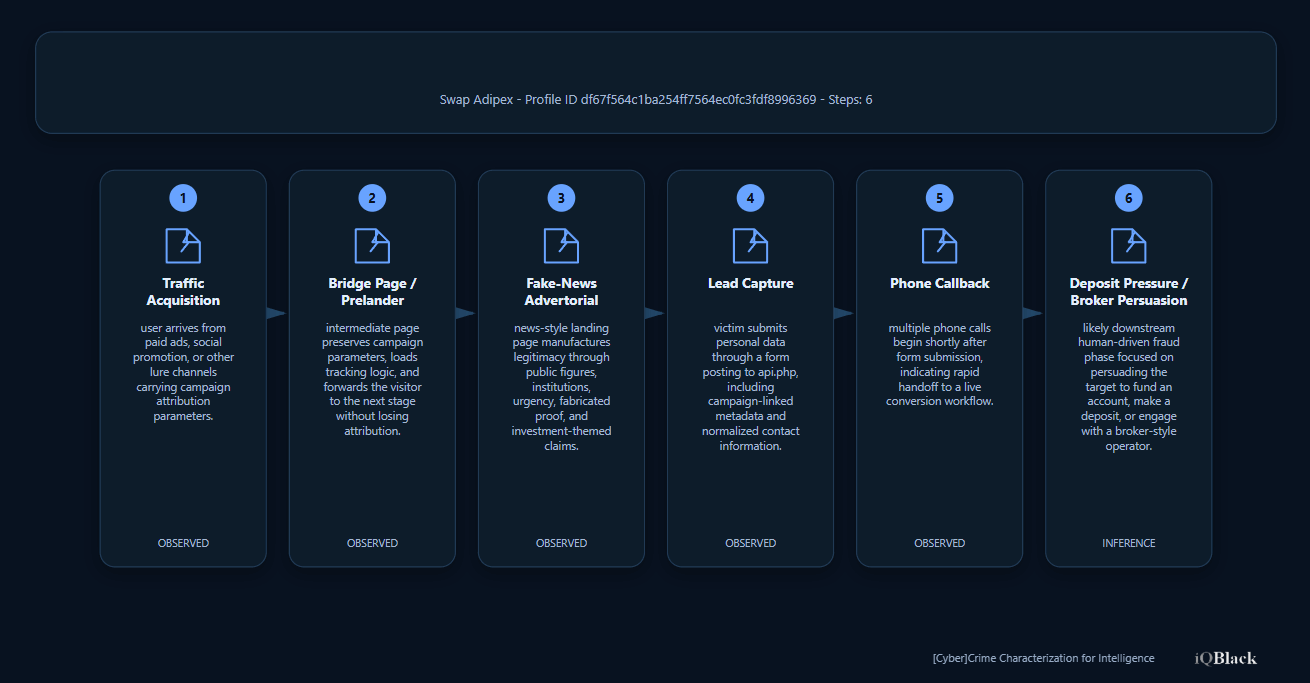
The bridge page: preserving attribution across stages
The smaller HTML sample is operationally simple but analytically very important. It includes TikTok Pixel logic, stores identifiers in both localStorage and cookies, extracts values such as p and ttclid from the query string, and rewrites target links to preserve campaign parameters.
This behavior is typical of a bridge page or prelander. Its role is not to persuade the visitor with content, but to ensure that the click remains monetizable as the user moves through the funnel. The presence of comments in Russian and explicit references compatible with a Keitaro-style tracking workflow suggest template reuse or tooling linked to an affiliate or campaign-tracking ecosystem, although not enough to support direct attribution.
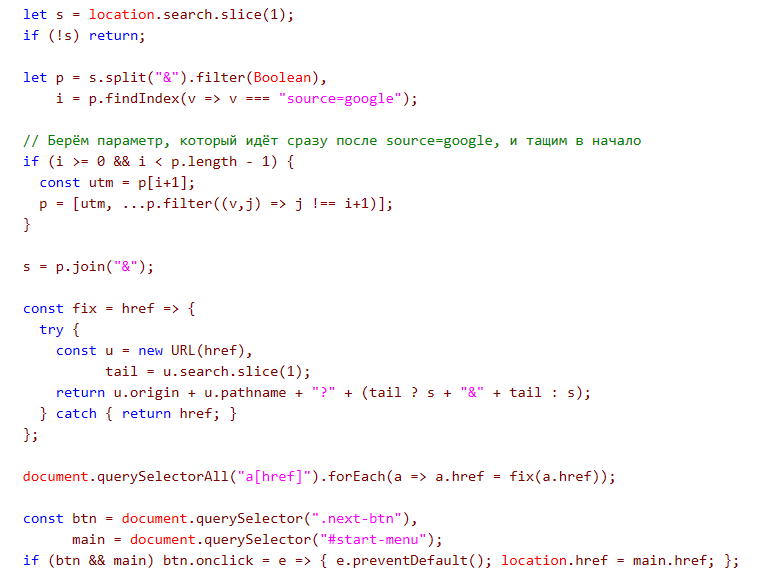
Observed tracking and campaign parameters
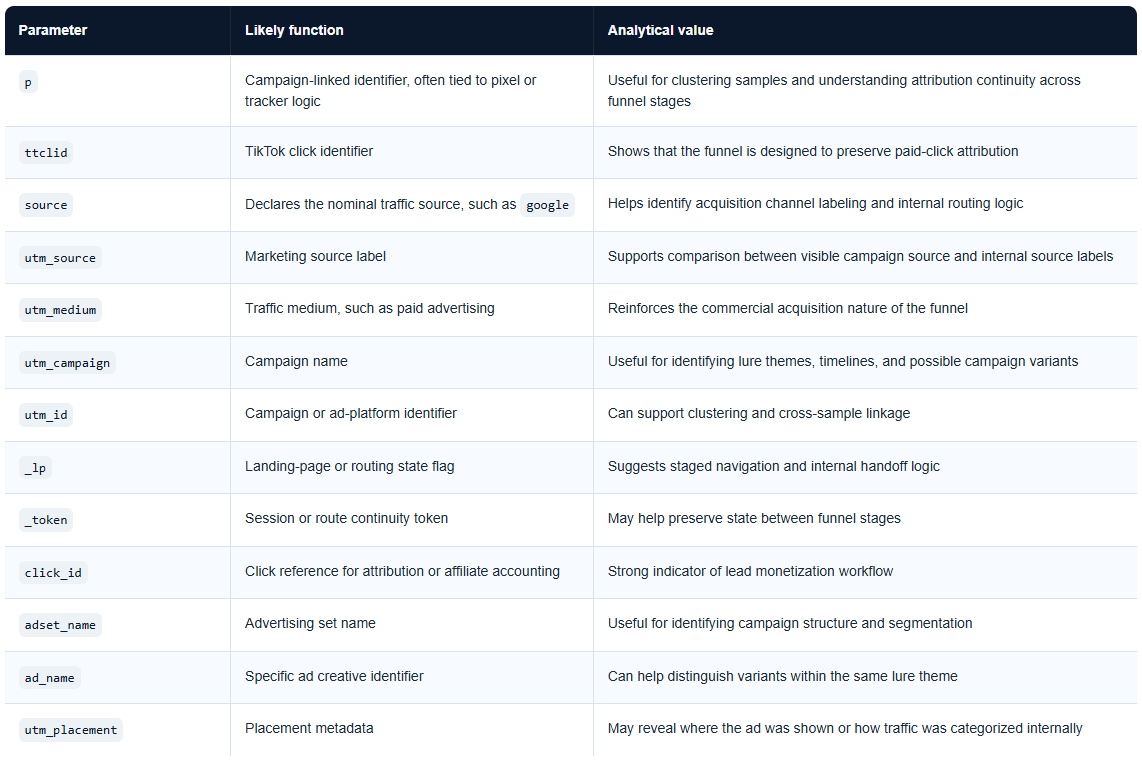
The reviewed samples use multiple tracking and attribution parameters that are typical of ad-tech, affiliate routing, and conversion measurement workflows.
The advertorial page: manufacturing legitimacy
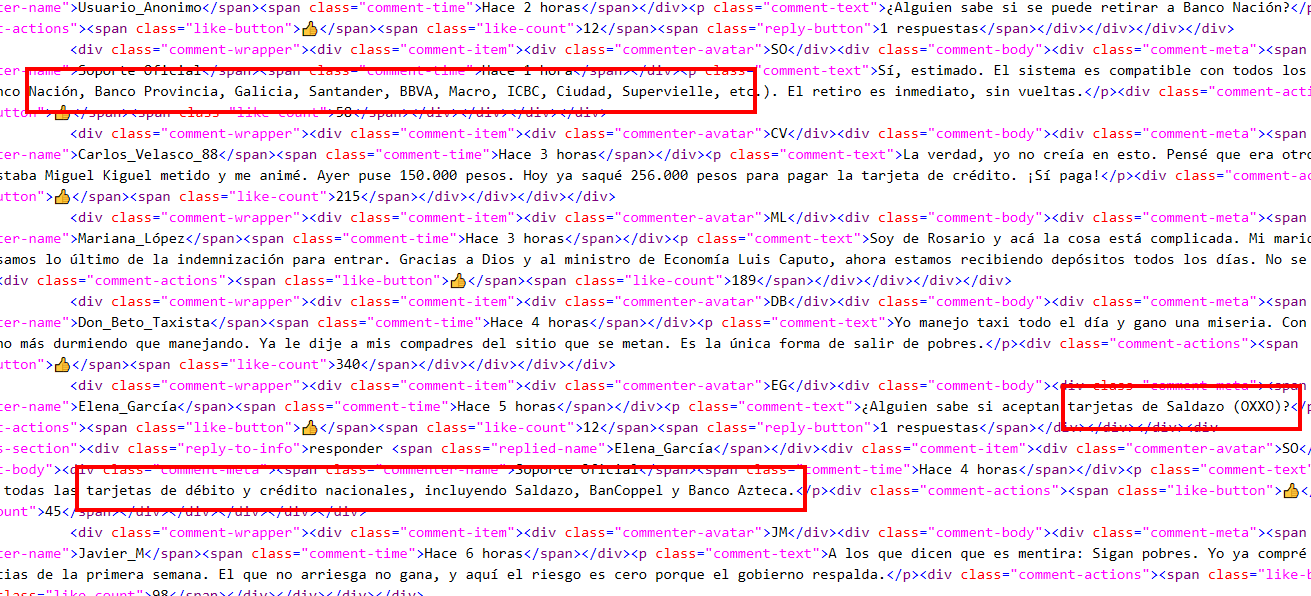
The longer landing page plays a different role. Its purpose is to build trust quickly and push the visitor toward form submission. The page imitates a legitimate news layout, invokes Argentine political and economic figures, references state institutions and major companies, and presents “Swap Adipex AI” as a government-backed or nationally relevant investment opportunity.
The page is not subtle. It relies on fabricated authority, fake urgency, exaggerated returns, and synthetic social proof. It includes rankings, comments, “verified” earnings, a returns calculator, and repeated calls to action. The technical sophistication here is low; the conversion engineering is not.
The form itself is revealing. It submits via POST to api.php and includes both visible user-supplied fields and hidden campaign/normalization fields such as click_id, utm_campaign, ad_name, phone_full, country, pixel, and source. This is infrastructure for lead capture, attribution, and routing.
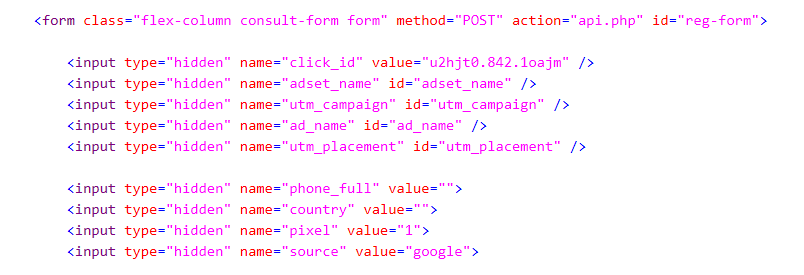
Observed hidden form fields
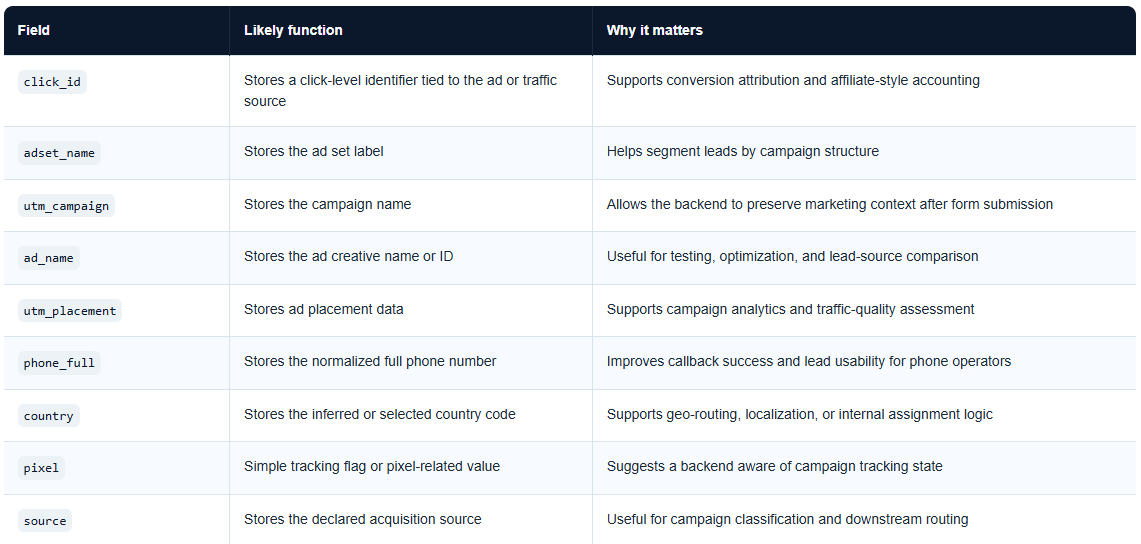
The main advertorial page contains hidden form fields that support lead normalization, attribution, and routing.
Notable deception indicators
Several indicators stand out across the reviewed content.
Authority abuse
The advertorial invokes real institutions, public officials, and economic actors to fabricate legitimacy. The narrative is designed to collapse skepticism by borrowing trust from recognisable names.
Template contamination across regions
Despite the Argentina-focused narrative, the page contains references inconsistent with that geography, including mentions associated with other countries and regulatory frameworks. This suggests template recycling across markets rather than a clean, locally authored page.
Synthetic proof and cosmetic logic
The “earnings” blocks and return calculator do not establish financial credibility. They create the appearance of it. Their value lies in persuasion, not in technical depth.
Conversion-oriented validation
The form uses client-side validation and telephone normalization to improve lead quality. This is not malicious in the exploit sense, but it is highly relevant operationally. Good data increases the effectiveness of the downstream call stage.
From web lead to phone pressure
One of the strongest findings in this case is what happens after form submission. Within roughly two minutes, repeated calls began arriving from multiple numbers. That timing is a major escalation in confidence. The sample no longer looks like a mere deceptive web page; it looks like a live intake point for a broader fraud workflow.
The reported callback sequence included multiple local-style numbers and one number using the +44 country code. This does not prove a UK-based operator, since VoIP, caller-ID masking, and rented numbering are common in fraud operations. What it does show is that the lead was acted on rapidly and repeatedly.
This behavior is highly consistent with call-center or boiler-room style investment fraud, where online forms are used to qualify targets and human operators attempt to close the conversion through live persuasion.
Observed callback sequence
- 11 3988-4130 (3:08 p.m.)
- 441294620837 (3:08 p.m.)
- 11 5361-4399 (3:09 p.m.)
- 441294620837 (3:10 p.m.)
- 11 5361-4399 (3:11 p.m.)
- 441294620837 (3:12 p.m.)
- 11 5361-4399 (3:14 p.m.)
- 441294620837 (3:35 p.m.)
- 11 3988-3978 (3:35 p.m.)
- 441294620837 (3:36 p.m.)
- 11 5361-4399 (3:37 p.m.)
- 441294620837 (3:38 p.m.)
- 11 5353-0847 (3:39 p.m.)
Comparison with documented cases
The cases reviewed here do not appear isolated. They map well to publicly documented patterns.
Research on deceptive affiliate marketing has already described how merchants, affiliates, aggregators, and specialized infrastructure providers cooperate in ecosystems that promote misleading offers and scam-oriented services at scale. The technical role of prelanders, parameter preservation, and offer routing is highly relevant to what is observed here.
Public reporting on fake-news and fake celebrity investment scams also shows a strong overlap: public trust is manufactured through familiar names and fabricated endorsements, then converted into contact details, and finally monetized through brokers, “account managers,” or call-center operators.
What stands out in the “Swap Adipex AI” samples is not a radically new technique, but a mature use of ad-tech and funnel continuity. The sophistication lies less in exploitation and more in conversion discipline.
What we can and cannot say about attribution
At this stage, the evidence supports high confidence in the presence of a deceptive investment funnel and moderate confidence in a reusable cluster or ecosystem theme. It does not support strong attribution to a named actor, group, or geography.
Russian-language code comments, lang="uk", and a +44 callback number are useful as soft clustering indicators. They may point to reused templates, tooling, or multinational routing. They do not, on their own, justify a clean attribution statement.
Operational implications
For defenders and researchers, the lesson is clear: not all harmful web infrastructure is best understood through the lens of malware. Some operations are better modeled as deceptive web funnels, where the code exists to preserve traffic value, improve lead quality, and optimize downstream victim handling.
This has implications for detection and classification. Samples like these should not be discarded as harmless simply because they do not drop a payload or execute an obvious exploit chain. Their risk lies in the broader operational circuit they enable.
Conclusion
The “Swap Adipex AI” cases reviewed so far point to a structured investment scam workflow built on fake-news styling, bridge-page attribution logic, form-based lead capture, and fast phone-based conversion. There is currently no strong evidence of classic browser-side malware. There is, however, strong evidence of a coordinated deception stack designed to move a victim from ad click to human exploitation with minimal friction.
The technical value of the sample is not in hidden malware logic, but in how clearly it exposes the mechanics of the funnel. That is precisely why cases like this deserve attention in threat research: they reveal how modern fraud infrastructure can look technically “clean” while remaining operationally dangerous.
Key takeaways
- This is best classified as a fraud infrastructure cluster, not as a conventional malware sample.
- The bridge page exists to preserve tracking and attribution, not to persuade the victim directly.
- The advertorial page exists to manufacture legitimacy and harvest usable lead data.
- The strongest operational indicator is the near-immediate callback behavior after form submission.
- The observed workflow is consistent with documented deceptive affiliate marketing and investment scam funnel models.
- Attribution remains weak; clustering confidence is stronger than actor identification.
Observed indicators
Cluster / Theme
- Theme: Swap Adipex AI
- Working designation: Fake-News Investment Funnel Cluster – Swap Adipex Theme
Observed domains
- gewafa.site
- yaxago.site
- suvivu.site
- rimeni.site
- xohole.site
- moyadu.site
- yipucu.site
- balisa.site
- huvuwo.site
- wekeju.site
- swapadipexai.com
- swap-adipex-ai.com
- swapadipexai.net
- swapadipex-ai.com
- swapadipex-ai.net
- assetnory.com
- capixxo.com
- zentrix.cfd
- cfd.zentrix.cfd
Observed redirect / destination examples
https://gewafa.site/?_lp=1&_token=...https://cfd.zentrix.cfd/cfd/secured-auto-login?token=...
Observed form endpoint
api.php
Observed telephony / post-submit indicators
- 11 3988-4130
- 441294620837
- 549572563316
- 11 5361-4399
- 11 3988-3978
- 11 5353-0847
- 11 3989-4570
- 11 3989-4405
- 11 3989-4394
- 11 5276-0807
- 11 5276-0829
- 341 530-3399
- 11 6656-9635
- 11 5343-5658
- 11 5272-3083
- 11 5254-1215
- 11 5276-2288
- 11 5361-0441
Observed infrastructure notes
- Cloudflare-fronted hosting
- Repeated
.siteTLD usage - Short randomized paths
- Keitaro-related parameter observed in broader cluster:
keitaro=Keit229
Assessment
- No classic browser-side malware observed at this stage.
- High confidence in deceptive lead-generation / investment scam funnel behavior.
- Low confidence in actor attribution at this stage.
References
- Le Pochat et al. – Tracing the Ecosystem of Fraudulent Cryptocurrency Investment Platforms
- Le Pochat et al. – Deceptive Affiliate Marketing: An Analysis of Fake Reviews and Misleading Offers
- Unit 42 – The Dynamics of Deepfake Scams
- OCCRP – Down the Bitcoin Funnel: The Tech Firms Driving Investors to Ruin With Fake Celebrity News
- FCA – Boiler room scams
- INTERPOL – Global Financial Fraud Assessment 2024
- 3C-INT – Swap Adipex [ID: df67f564c1ba254ff7564ec0fc3fdf8996369]
Explore 3C-INT
Expand actor, campaign and operational-link tracking through a structured intelligence layer.
Get new publications
Subscribe to receive new articles and public updates from iQBlack without unnecessary noise.