Threat Actor Characterization

RedHack
ID: fc2c9179c9cd5d4a3311c5f07ae94c3494640| Kizilhack | Kızıl Hackerlar | Kı********************* | r3***** |
| r3***** | Re****** | Re********************* | Re**************** |
| RE********** | R** | th******** | Th******** |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
RedHack — Turkish Marxist–Leninist hacktivist group founded in 1997 with a reported core of ~12 members. Open sources attribute to RedHack intrusions and data-leak operations against police and ministries (2012), exploitation of public-facing apps and mass disclosures tied to parliament and agencies (2013–2014), breaches of major telecoms (TTNet, Turkcell, Vodafone) with PII leaks (2014), DDoS/availability actions, and the 2016 compromise and leak of Energy Minister Berat Albayrak’s emails.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1491.002 | External Defacement | TA0040 | |
| T1498 | Network Denial of Service | TA0040 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 | |
| T1041 | Exfiltration Over C2 Channel | TA0010 |
|
| T1190 | Exploit Public-Facing Application | TA0001 | |
| T1565.001 | Stored Data Manipulation | TA0040 | |
| T1110.001 | Password Guessing | TA0006 |
|
| T1566 | Phishing | TA0001 |
|
| T1589 | Gather Victim Identity Information | TA0043 |
|
| T1590 | Gather Victim Network Information | TA0043 |
|
RedHack Hacktivist Group
CLASSIFICATION: Unclassified / Open Source
Executive Summary
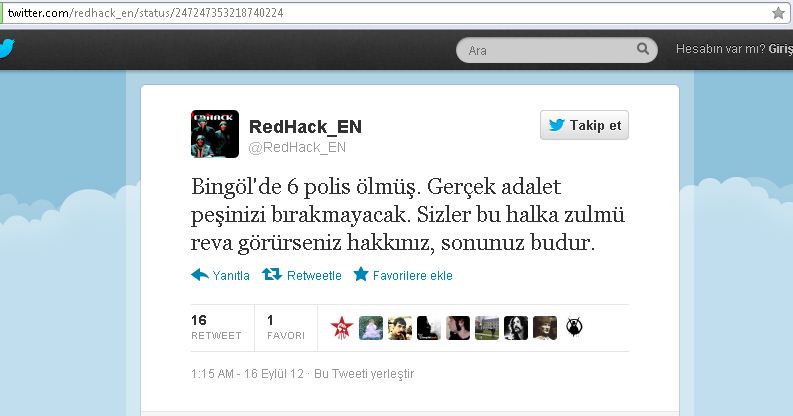
RedHack (Kızıl Hackerlar) is a Marxist–Leninist hacktivist collective founded in 1997, commonly described as having a core of ~12 members supported by a wider circle of sympathizers (we have identified 15 verified members). Open sources attribute to RedHack a long-running pattern of politically framed cyber operations: intrusions and data-leak campaigns against police and ministries (2012), exploitation of public-facing applications and high-visibility actions touching Parliament and administrative portals with data disclosures (2013–2014), breaches involving Turkish telcos (TTNet, Turkcell, Vodafone) and publication of PII (2014), DDoS/availability impacts, and—most prominently—the 2016 compromise and mass release of Energy Minister Berat Albayrak’s emails.
Socio-legal scholarship frames 2012–2017 as the group’s peak period of visibility and emphasizes the state’s criminalization of RedHack (terrorism/cyber-terror labels, emergency measures, and pressure on journalists around sensitive leaks). The evidence supports a pattern of politicized hacktivism with strong disclosure/amplification strategy; however, primary technical artifacts are uneven and some attributions rest on revendications and secondary reporting. Overall confidence: medium.
Executive Analyst Brief for CISO — RedHackClassification: Unclassified / OSINT1) Who / whatRedHack is a Turkish, Marxist-aligned hacktivist collective active since the late 1990s that has repeatedly targeted Turkish state and commercial infrastructure with website defacements, data exfiltration and public leaks. Its operations historically include leaks of government/official emails and credentials and disruption of public web assets. Core profile and timeline summaries are documented in open re
Hunting Playbook — RedHack Category A — Defacement & Webroot Tamper (HIGH priority) Hunt 1 — Webroot file creation / modification: known RedHack defacement file names ATT&CK® techniques: [T1190][T1491.002] Rationale: RedHack historically drops defacement pages. Monitor for creation/serving of those filenames. Splunk (SPL) index=osquery OR index=filebeat OR index=sysmon (file_path=*webroot* OR file_path=*www* OR file_path=*htdocs* OR file_path=*public_html*) AND (file_name="Hakkimizda.as
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
