Threat Actor Characterization
Anshar Caliphate Army
ID: dfee5cf1582046b79985a664878851c7| ACA | Ansar Khilafah Army | An***************** | Cy************* |
| Cy****************** | ان************* | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
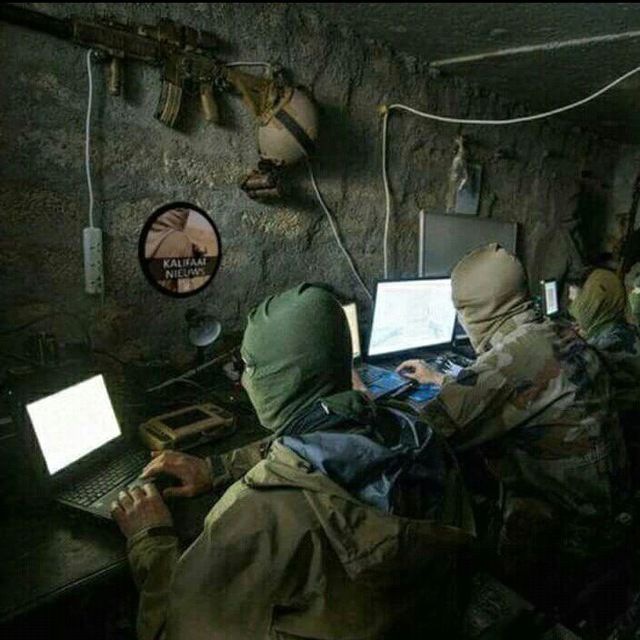
Anshar Caliphate Army (ACA) — Southeast Asia pro-ISIS hacktivist label documented in 2018 as part of the UCC collective. Activity set: symbolic defacements, DDoS claims and account takeovers during #OpTheWorld, plus threat videos/posters aimed at Indonesian GOV targets. Language/use patterns indicate Indonesian linkage.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1491.002 | External Defacement | TA0040 | |
| T1498 | Network Denial of Service | TA0040 |
|
| T1585 | Establish Accounts | TA0042 | |
| T1589 | Gather Victim Identity Information | TA0043 |
|
CLASSIFICATION: Unclassified / Open Source
Executive Summary
The Anshar Caliphate Army (ACA) is a Southeast Asia pro-ISIS hacktivist label that surfaced publicly in mid-2018 as part of the United Cyber Caliphate (UCC) ecosystem. Open sources document ACA’s role in symbolic defacements, account takeovers and DDoS claims during #OpTheWorld, coupled with a steady stream of threat posters/videos on social media. Technical proficiency appears low, consistent with UCC-style OSINT-heavy doxing and opportunistic web hits; influence is achieved via propaganda amplification rather than sophisticated intrusions. Overall confidence: medium (credible think-tank documentation; actor artifacts mainly evidentiary for chronology/propaganda).
Pro-ISIS alignment; ACA is explicitly listed among the UCC component groups in 2018 analytical reporting. Language indicators and target selection point to Indonesian origins within a broader transnational umbrella.
