Threat Actor Characterization

ALTOUFAN TEAM
ID: 93659cff231652cdbbe776794b143742| Al Toufan | Al-Toufan | al****** | AL********** |
| Ba******************* | Fl******** | Th************ | فر********** |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
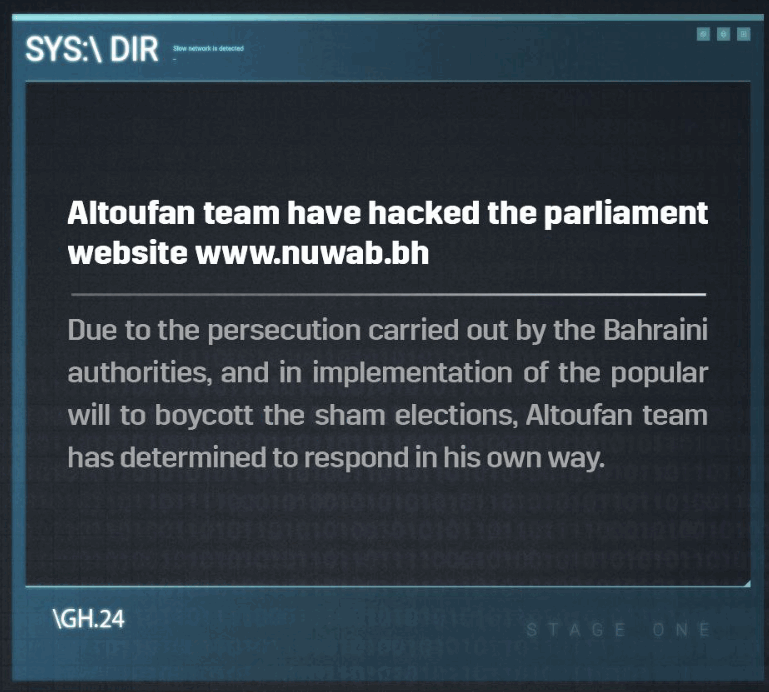
ALTOUFAN TEAM (Al-Toufan, "The Flood") is a politically motivated hacktivist group with anti-Zionist, anti-monarchy, and pro-14-February movement sentiments. The group has conducted defacements, DDoS attacks, credential-enabled intrusions, and data manipulation campaigns against Bahraini and Israeli targets, and more recently claims a data breach against the US Navy’s Fifth Fleet in Bahrain. Public reporting highlights use of stolen credentials (likely from info-stealer logs) to access Bahrain’s Social Insurance Organization (SIO) portal and modify pension records, widespread defacement/DDoS activity against government and financial sites, and hack-and-leak style operations promoted via X and Telegram. Ref: Malpedia, Cyble, Al Mayadeen, Cyber Shafarat, Associated Press/SecurityWeek.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1565.001 | Stored Data Manipulation | TA0040 |
|
| T1491.002 | External Defacement | TA0040 |
|
| T1498.001 | Direct Network Flood | TA0040 |
|
| T1567.002 | Exfiltration to Cloud Storage | TA0010 |
|
| T1555.003 | Credentials from Web Browsers | TA0006 |
|
| T1585.001 | Social Media Accounts | TA0042 |
|
Hunt 1 — Stealer-log credential abuse against business/benefits portals
Goal: Detect use of compromised credentials (from info-stealer logs) against production portals (pensions, HR, benefits, citizen/self-service).