Threat Actor Characterization

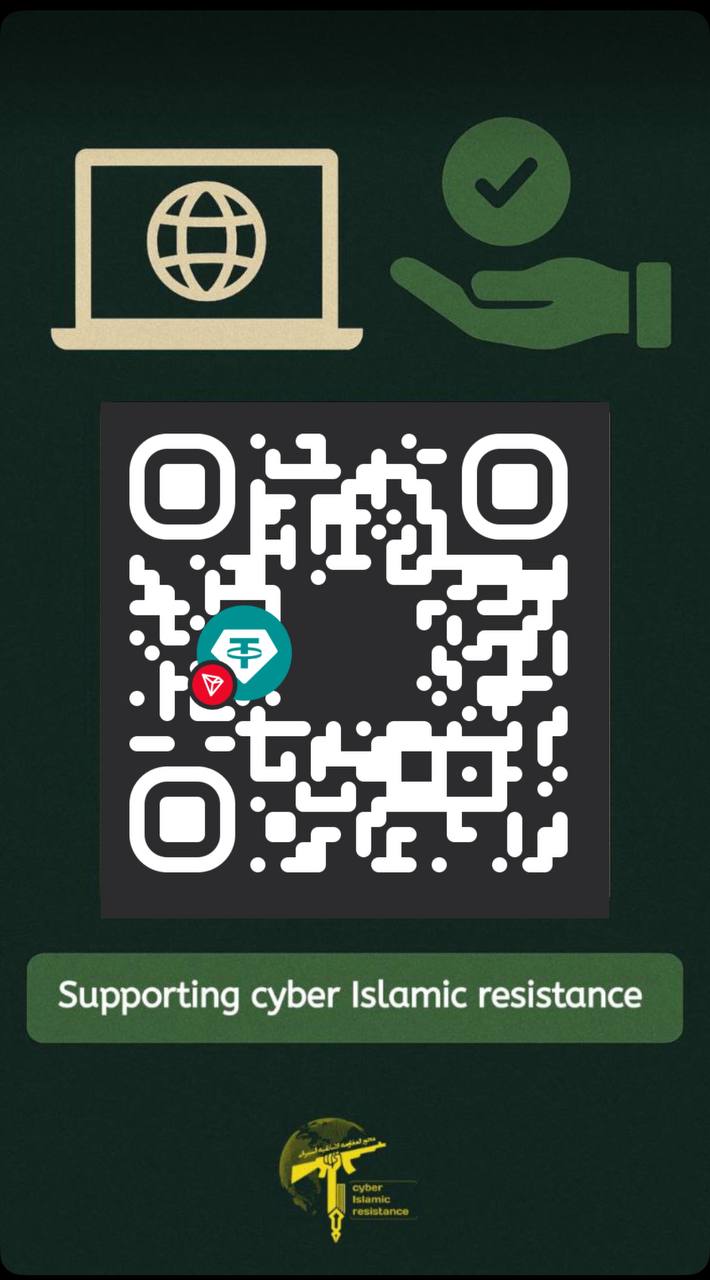
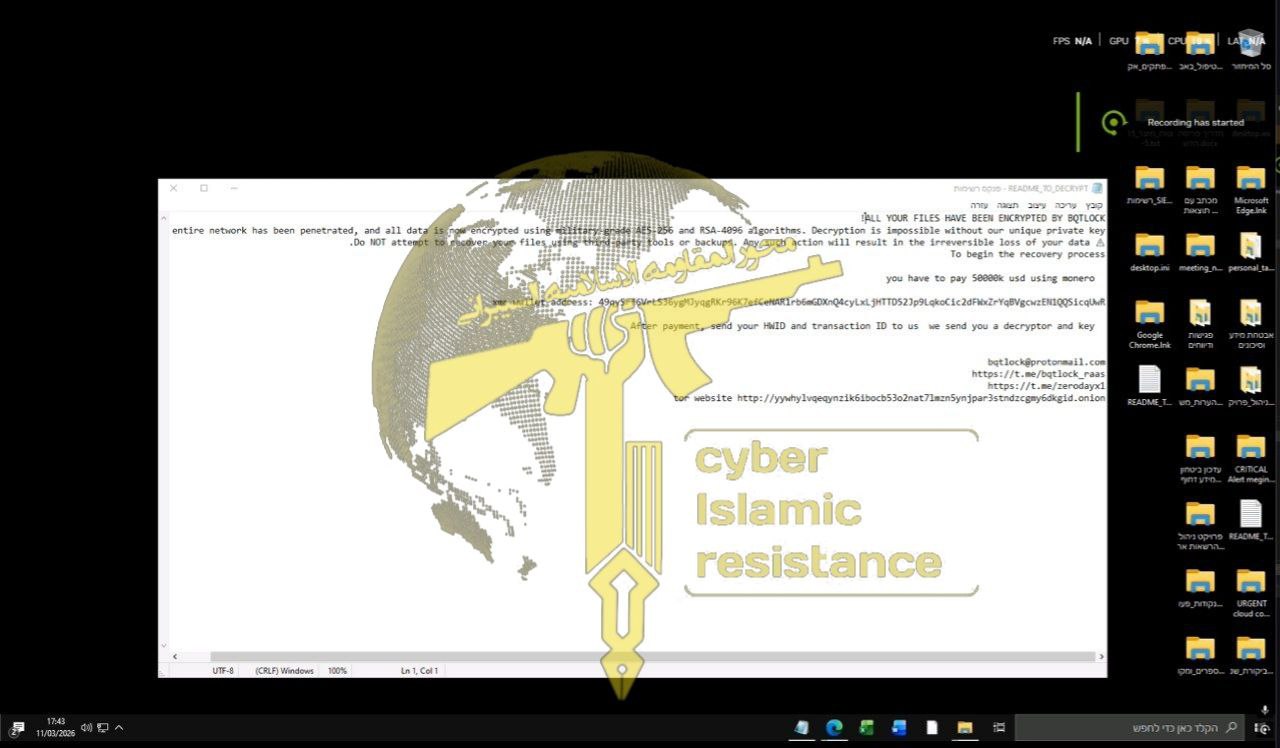
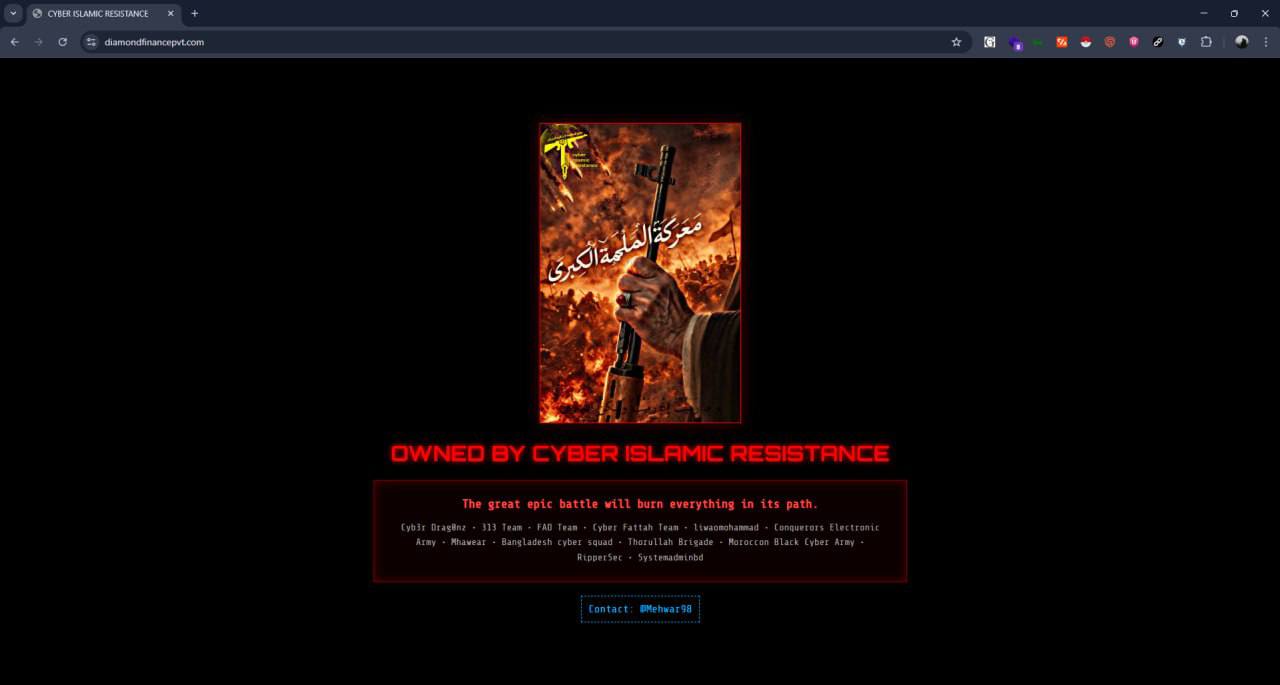
Cyber Islamic Resistance
ID: 8f27533a6eae91685fa0355542c0b3db| CIR | Cyber Axis of Resistance | Cy***************************** | Cy******************** |
| Ej****************************** | Is*************************** | Is********************* | Is*************************** |
| La******************************* | Th************************* | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Cyber Islamic Resistance is a pro-Iran-aligned cyber / hybrid extremist cluster that functions as a public-facing umbrella for coordinated DDoS, defacement, alleged data theft, and propaganda exploitation against Israeli and Western targets. Its activity is strongly Telegram-centric, coalition-driven, and often amplified by adjacent pro-Iranian and pro-Russian actors.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1595 | Active Scanning | TA0043 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1498 | Network Denial of Service | TA0040 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1565.001 | Stored Data Manipulation | TA0040 |
|
| T1485 | Data Destruction | TA0040 |
|
| T1213 | Data from Information Repositories | TA0009 |
|
| T1102.002 | Bidirectional Communication | TA0011 |
|
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Cyber / Hybrid Hacktivist-Extremist Cluster - Origin: Assessed transnational “Axis of Resistance” ecosystem with strong pro-Iran alignment and visible Iraq/Lebanon-linked coalition participation
Author: iQBlack CTI Team
Executive Summary
Cyber Islamic Resistance is best modeled as a clustered cyber-propaganda, claim, and coalition-signaling ecosystem rather than a neatly bounded single team. Public-facing branding, Telegram-based mobilization, coalition announcements, and recurring references to the “Islamic Resistance Axis” and “Holy League” indicate an umbrella identity used to coordinate or at minimum publicly synchronize multiple aligned hacktivist and nuisance cyber brands.
The actor’s messaging is consistently anti-Israel, pro-Palestine, pro-“axis of resistance,” and openly convergent with pro-Russian narratives. Public reporting in 2025–2026 described Cyber Islamic Resistance as a pro-Iranian umbrella collective coordinating multiple hacktivist teams for synchronized DDoS, defacement, and destructive or allegedly destructive operations against Israeli and Western infrastructure. Internal Telegram-derived analysis further indicates that the visible communications layer around multiple @Mhwea* identities recirculates materially similar content, which strengthens the cluster model over a “many independent teams” explanation.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
