Threat Actor Characterization

Dark Storm Team
ID: 8c8b24698c3e7d70dc625634a34afbb668798| Dark Storm | Dark Storm Hackers Team | Da************* | Da*********** |
| Da******* | D** | T** | Te************* |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Dark Storm Team (DarkStrom/Dark Strom Team) is widely described in OSINT as a pro‑Palestinian‑aligned hacktivist group specializing in DDoS campaigns and claim amplification, including use of third‑party 'proof links' (check-host/check-report style) to substantiate claimed outages. OSINT also describes a monetization dimension (DDoS-for-hire and data-sale/leak narratives). ATT&CK mapping emphasizes DDoS disruption and social-platform coordination; broader capability assertions are treated conservatively unless corroborated by victim telemetry.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 | |
| T1585.001 | Social Media Accounts | TA0042 |
|
| T1583.006 | Web Services | TA0042 |
|
| T1595 | Active Scanning | TA0043 |
|
Dark Storm Team (DarkStrom / Dark Strom Team) — Pro‑Palestinian‑Aligned Hacktivist Group (DDoS + Monetized Services)
Classification: TLP: WHITE — Open Source Intelligence (OSINT)
Category: Cyber / Hacktivism — Disruption (DDoS) + influence/claims; monetization via “for‑hire” services
Assessed home base: Unclear / transnational (OSINT suggests possible Russia links while publicly framed as pro‑Palestinian)
Executive Summary
Dark Storm Team is widely described in OSINT as a pro‑Palestinian‑aligned hacktivist group specializing in distributed denial‑of‑service (DDoS) campaigns and high‑visibility claim amplification. Open reporting and research coverage consistently frame the group as politically motivated (support for Palestine, opposition to Israel and perceived supporters), while also describing a profit‑seeking dimension: DDoS‑for‑hire style services and monetization attempts.
A key observable behavior is the use of third‑party “proof links” (e.g., check‑host/check‑report style availability captures) to bolster credibility for claimed outages. This approach appears repeatedly in coverage of March 2025 X (Twitter) outages, where Dark Storm Team publicly claimed responsibility and provided proof artifacts.
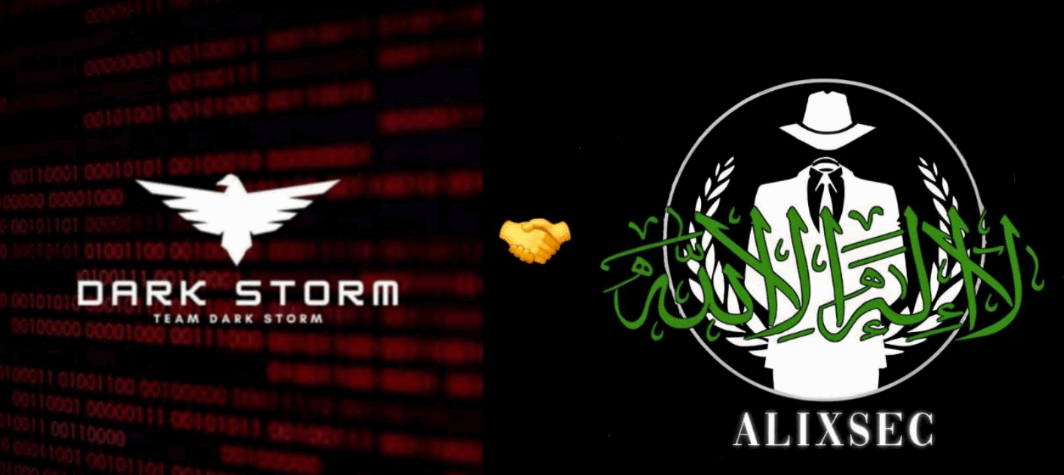
An Orange Cyberdefense investigation describes a decentralized/horizontal structure (unconfirmed), Telegram‑centric coordination, coalition relationships with other groups, and a blend of ideological and financial motivations. It also references broader service offerings (DDoS‑as‑a‑service, leaks, and ransom‑as‑a‑service narratives) and notes possible links with Russia, highlighting attribution complexity.
IOC Appendix (TLP:WHITE) — Dark Storm Team
Note: Public reporting on Dark Storm Team is DDoS- and claim-centric, with limited stable malware/C2 indicators suitable for static IOC blocking. This appendix prioritizes behavioral indicators and correlation cues.