Threat Actor Characterization

Belarusian Cyber Partisans
ID: 83b6ff72b362eeb77758e1c57bc897fd83163| BCP | Belarusian Cyber-Partisans | Cy************* | Cy************ |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Belarusian Cyber Partisans (BCP) — Belarusian hacktivist collective that emerged amid the 2020 protests against Alyaksandr Lukashenko. The group conducts high-visibility intrusions, leaks, and disruptive operations against Belarusian/Russian state entities, and claims selective support to Ukraine. Public artifacts include 2021 multi-database breaches ("Operation Heat"), a 2022 ransomware-for-impact incident on Belarusian Railways, and a 2025 joint operation with Silent Crow disrupting Aeroflot.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1486 | Data Encrypted for Impact | TA0040 | |
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 | |
| T1041 | Exfiltration Over C2 Channel | TA0010 | |
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1498 | Network Denial of Service | TA0040 |
|
| T1598 | Phishing for Information | TA0043 |
|
| T1587 | Develop Capabilities | TA0042 |
|
| T1589 | Gather Victim Identity Information | TA0043 |
|
| T1585 | Establish Accounts | TA0042 |
|
CLASSIFICATION: Unclassified / Open Source
Executive Summary
Belarusian Cyber Partisans (BCP) is a hacktivist collective that emerged in 2020 during the mass protests against Alyaksandr Lukashenko. The group presents itself as a volunteer network of IT specialists and non-IT contributors pursuing regime change, rule of law, and democratic rights, with operations spanning intrusion, data exfiltration, leaks, and disruptive actions against Belarusian and, increasingly, Russian state targets. Publicly attributed milestones include “Operation Heat” (mid-2021) with multi-database access (passport, police, MIA systems), the January 2022 Belarusian Railways ransomware-for-impact action to hinder Russian troop movements, and the July 2025 Aeroflot disruption claimed jointly with Silent Crow that led to widespread flight cancellations in Russia. BCP couples technical operations with information operations, including a Telegram presence focused on leaks/cyber-investigations and the development of Partisan Telegram (P-Telegram) for activist security. Recruitment runs through an open volunteer intake model and donation rails (crypto, cards, Patreon/Partizan Wave). Overall confidence in the group’s capability and authorship of the listed operations is medium-high, with parts independently corroborated by reputable outlets; some claims remain difficult to verify under wartime censorship and counter-propaganda.
- 2020-09. Emergence of the Cyber Partisans amid Belarus protests; public mission frames anti-dictatorship, pro-rule-of-law objectives. — CyberPartisans
- 2021-07-26…30. Operation Heat begins: access to multiple Belarus state databases (traffic police, AIS Passport, MIA systems, video services). — CyberPartisans
- 2021–2022. Leaks and investigations referencing KGB personnel/operatives, police and security services data. — AP News
- 2022-01-25. Belarusian Railways: ransomware-for-impact to impede Russian troop movements; claims of control/disruption. — WIRED
- 2022-03–06. Wiretaps & audio releases (Russian embassy/consulate in Belarus) via BCP Telegram and YouTube. — CyberScoop
- 2022-12-28. P-Telegram (Partisan Telegram) profiled: secure fork/workflow for at-risk activists (auto-wipe/SOS). — The Record from Recorded Future
- 2024-03–04. Analytical reporting recaps BCP’s operations (MIA classified servers breach; railway hack; COVID mortality exposure). — The Record from Recorded Future
- 2025-05-08. Assessments highlight ongoing secrecy and deniable access; emphasis on “not disclosing most impactful hacks.” — New Eastern Europe
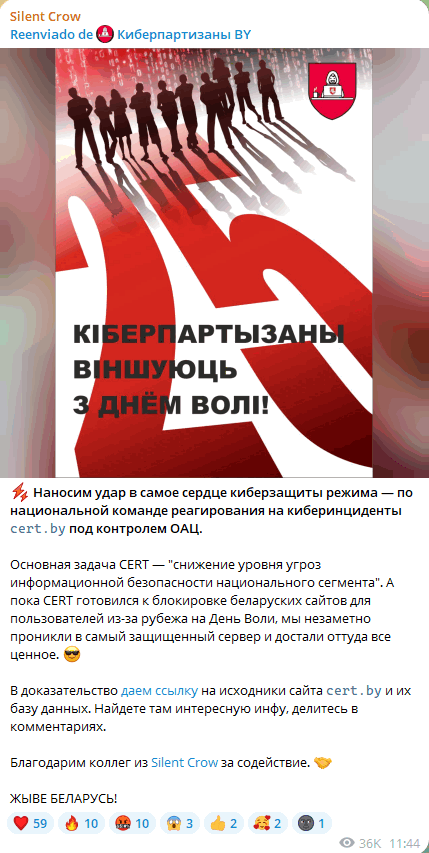
- 2025-07-28…30. Aeroflot disruption: BCP + Silent Crow claim large-scale disruption causing dozens to 100+ flight cancellations; Russia confirms incident and recovery steps. — Reuters
- 2025-08-01. BBC Monitoring synthesis: “dozens of attacks” on Belarusian/Russian government targets; messaging via defacement/leak channels. — monitoring.bbc.co.uk
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
