Threat Actor Characterization

Cyber.Anarchy.Squad
ID: 7c89c4599ea886e33424cc7581978ebd| C.A.S | C.A.S Group | C.******** | C** |
| CA******* | CA****** | Cy***************** | Cy***************** |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1105 | Ingress Tool Transfer | TA0011 |
|
| T1003 | OS Credential Dumping | TA0006 |
|
| T1059 | Command and Scripting Interpreter | TA0002 |
|
| T1485 | Data Destruction | TA0040 |
|
| T1486 | Data Encrypted for Impact | TA0040 |
|
| T1071 | Application Layer Protocol | TA0011 |
|
Classification: Unclassified / Open Source Intelligence (OSINT)
Category: Cybercrime / Hacktivism — Origin: Ukraine-aligned (pro-Ukraine ecosystem)
Author: iQBlack CTI Team
Executive Summary
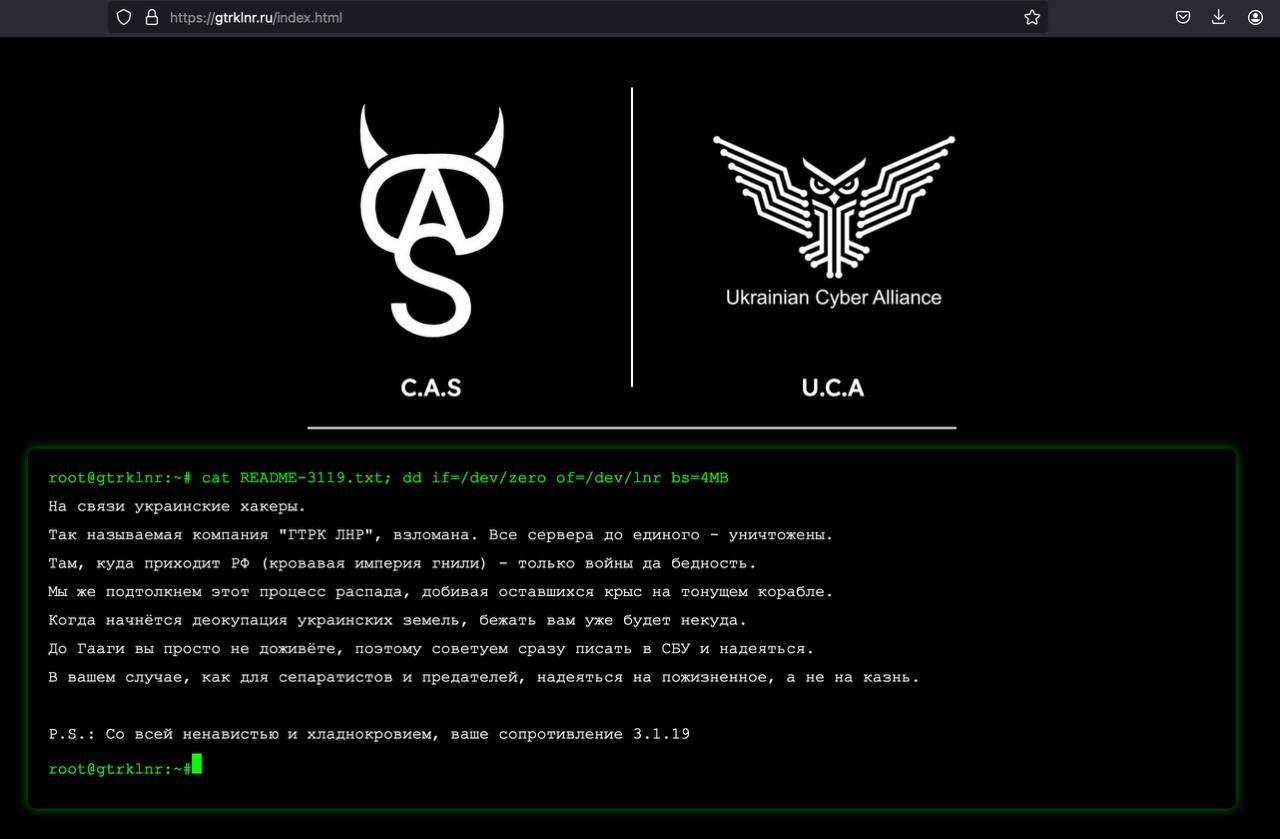
Cyber.Anarchy.Squad (C.A.S) is a pro-Ukraine hacktivist collective active since 2022, conducting destructive and data-leak operations primarily against Russia and Belarus. Public technical reporting (Kaspersky Securelist, 2024-12-18) documents C.A.S campaigns abusing public-facing application vulnerabilities (e.g., Jira, Confluence, MS-SQL) and deploying uncommon RATs (Revenge RAT, Spark RAT) and Meterpreter for post-exploitation. Victimology spans government, telecom, tech, and industrial firms in Russia/Belarus. C.A.S activity includes high-impact disruptions and data destruction, such as the Avanpost (Avanpost/Avapost) breach (2024-07) and Infotel JSC service disruption (2023-06), both publicly acknowledged by victims/media. C.A.S communicates on Telegram, posts claims/evidence, and has links to other pro-Ukraine groups (Ukrainian Cyber Alliance—UCA, RUH8, RM-RF), with cross-group operational collaboration noted. Overall, C.A.S’s capability to rapidly weaponize Internet-exposed services, leverage commodity+rare tools, and coordinate claims places it among the more operationally consequential hacktivist actors in the RU/UA conflict space. Confidence: high for targeting, tooling, and campaign facts; medium for internal membership structure.
- Industries / Sectors: Government ministries and agencies; telecommunications; financial/banking infrastructure enablers; technology/entertainment; industrial enterprises.
- Geography (Region): Primarily Russia and Belarus; opportunistic RU-linked providers.
- Timeframe: 2022–present; notable peaks in 2023–2025.
Executive Analyst Brief for CISO
Why care now: C.A.S has executed confirmed high-impact ops (Avanpost 2024-07; Infotel 2023-06), proving capacity for destruction & encryption beyond DDoS.
OSINT Library — Cyber.Anarchy.Squad (C.A.S)
2025-08-21 — SecurityWeek (brief via The Record) — “Pro-Ukraine hackers compromise Investment Projects in Russia”
https://www.scworld.com/brief/pro-ukraine-hackers-compromise-investment-projects
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
