Threat Actor Characterization

IT Army of Russia
ID: 60d5067039f6032b8b4659b5ed60b8c776669| itarmy_ru | ITRUSSIA | Th******************* | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
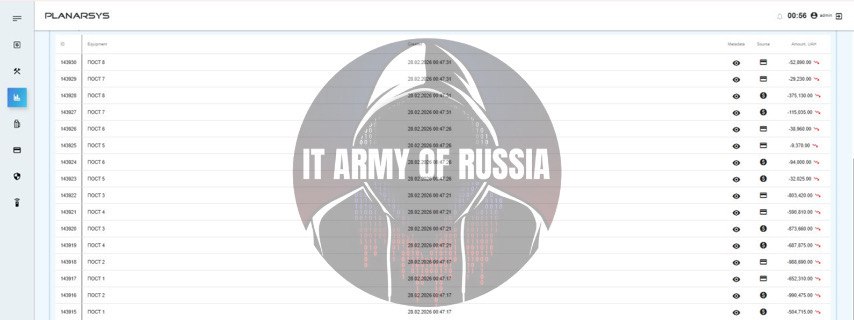
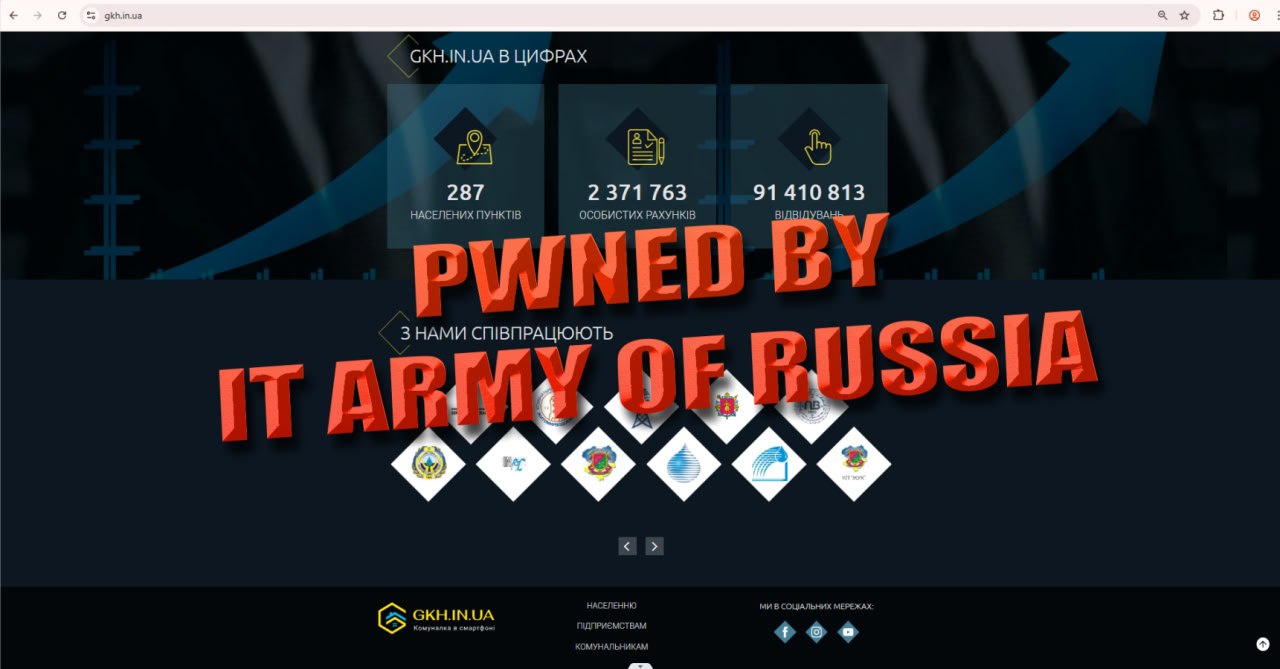
IT Army of Russia is a pro‑Russia-aligned hacktivist campaign brand reported in mid‑2025 OSINT as targeting Ukraine and supporters via Telegram-coordinated operations. Public reporting emphasizes disruption (DDoS) and claim amplification, with some mention of insider recruitment and information collection. Government and partner advisories in late 2025 highlight opportunistic pro‑Russia hacktivist disruption patterns that inform defensive priorities. ATT&CK mapping is conservative: DDoS and social-platform coordination are supported; insider solicitation and related preparatory behaviors are included as INFERENCE where not directly evidenced for this specific brand.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 | |
| T1585.001 | Social Media Accounts | TA0042 |
|
| T1595 | Active Scanning | TA0043 |
|
| T1589 | Gather Victim Identity Information | TA0043 |
|
IT Army of Russia — Pro‑Russia‑Aligned Hacktivist Brand (Telegram‑Coordinated Disruption + Insider Recruitment Claims)
Classification: TLP: WHITE — Open Source Intelligence (OSINT)
Category: Cyber / Hybrid — Hacktivism (DDoS + claims), potential data‑theft/insider solicitation (claim-driven)
Assessed home base: Unclear; pro‑Russia alignment reported; Telegram‑centric ecosystem
Executive Summary
IT Army of Russia is a pro‑Russia-aligned hacktivist label reported in OSINT as a newer entrant (mid‑2025 reporting) in the pro‑Russia hacktivist ecosystem targeting Ukraine and its supporters. Open reporting describes Telegram as the primary coordination surface, with campaign-style operations emphasizing disruption (DDoS) and information collection. Some reporting describes insider recruitment attempts and data‑theft operations, though detailed technical corroboration is often limited in publicly available material.
This actor should be treated as a campaign brand in a broader pro‑Russia hacktivist landscape characterized by coalition dynamics, brand churn, and opportunistic targeting. Government and partner advisories in late 2025 emphasize that pro‑Russia hacktivist ecosystems conduct opportunistic disruptive attacks (often DDoS) and—within critical infrastructure contexts—may abuse exposed remote access to OT devices; those advisories provide the best baseline for defensive control priorities, even when not naming every emerging brand.
Confidence is medium that IT Army of Russia is a real and operational hacktivist brand used in Telegram-coordinated campaigns. Confidence is low–medium regarding deeper intrusion capability and insider recruitment effectiveness due to claim-driven reporting and limited victim-side telemetry in the open record reviewed for this deliverable.
IOC Appendix (TLP:WHITE) — IT Army of Russia
Note: Reviewed OSINT provides limited stable infrastructure IOCs specifically attributable to IT Army of Russia. This appendix focuses on behavioral indicators and correlation cues typical of Telegram-coordinated hacktivist disruption and insider solicitation.