Threat Actor Characterization
adrxx
ID: 409f0a8f7265fac0caeec8fea0a61f2046997| Addrx | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
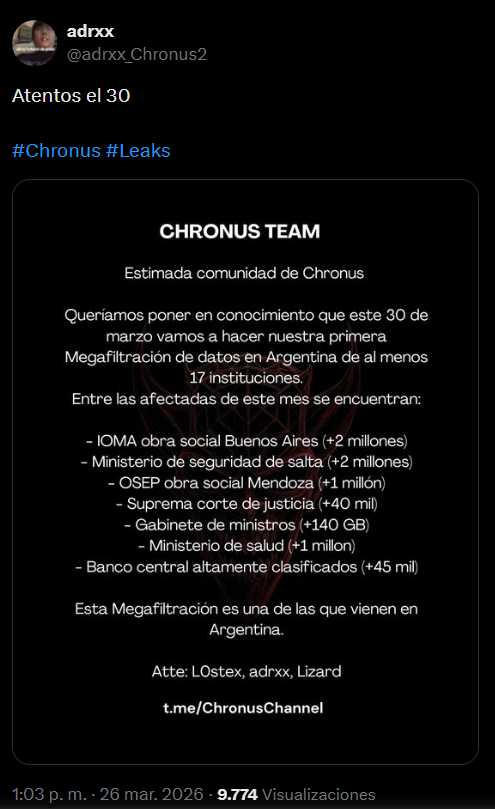
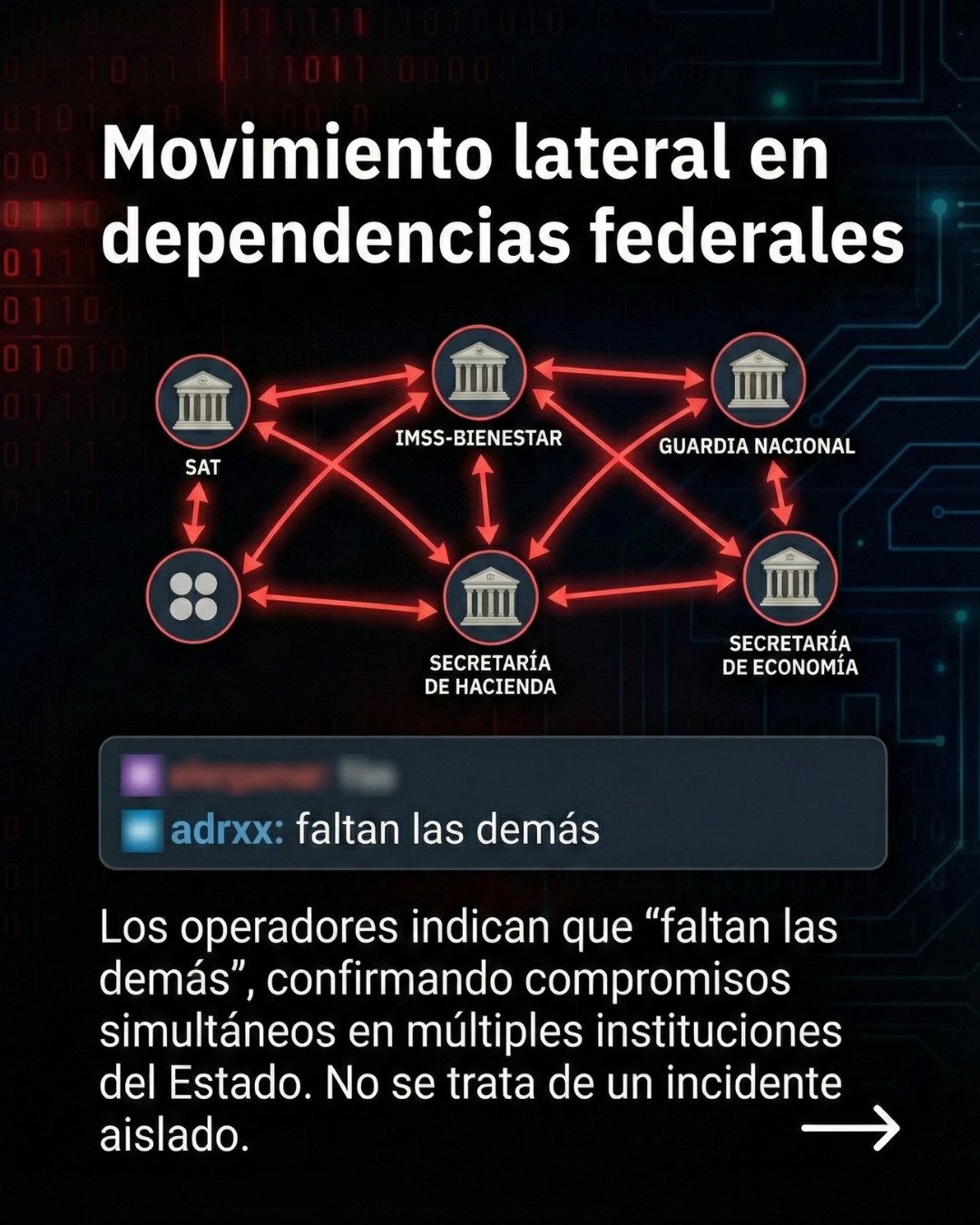
adrxx is a visible actor-persona associated with the Chronus Team ecosystem and repeatedly linked to website defacement, intrusion and data-leak activity affecting public-sector targets in Mexico and, more recently, Argentina. The available evidence supports treating adrxx as a cluster member rather than a standalone threat group.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1505.003 | Web Shell | TA0003 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1041 | Exfiltration Over C2 Channel | TA0010 |
|
| T1589 | Gather Victim Identity Information | TA0043 |
|
adrxx - Highly active persona operating within the Chronus Team ecosystem
Classification: TLP:WHITE - Open Source Intelligence (OSINT) and selected HUMINT / internal reporting
Category: Cybercrime / Intrusion, data exposure and website defacement persona - Origin: Mexico (assessed, not confirmed)
Author: iQBlack CTI Team
Executive Summary
adrxx is assessed as a highly active persona operating within the Chronus Team ecosystem, a loose and publicity-aware cluster associated with defacements, opportunistic intrusions, data-leak claims and reputational pressure against public-sector and quasi-public targets in Mexico and, more recently, Argentina. Public reporting and operational signatures consistently place adrxx among the more visible names used to sign or promote incidents linked to the cluster.
Available information does not support treating adrxx as a standalone group. The stronger assessment is that adrxx functions as an exposed operator-facing alias inside a broader collective brand, alongside personas such as L0stex, SoftVoid, Blackout, Sh3llhunter, Entropy, Nihil and others. INFERENCE (confidence: high): this structure gives the cluster resilience, plausible deniability and flexible branding while allowing individuals such as adrxx to accumulate visibility and credibility.