Threat Actor Characterization

Anti-Armenia Team
ID: 30519ff175f41f5045b85143863861a335745| AAT | ANTİ ERMENİA TEAM | An************* | Az******************* |
| Az*********************** | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
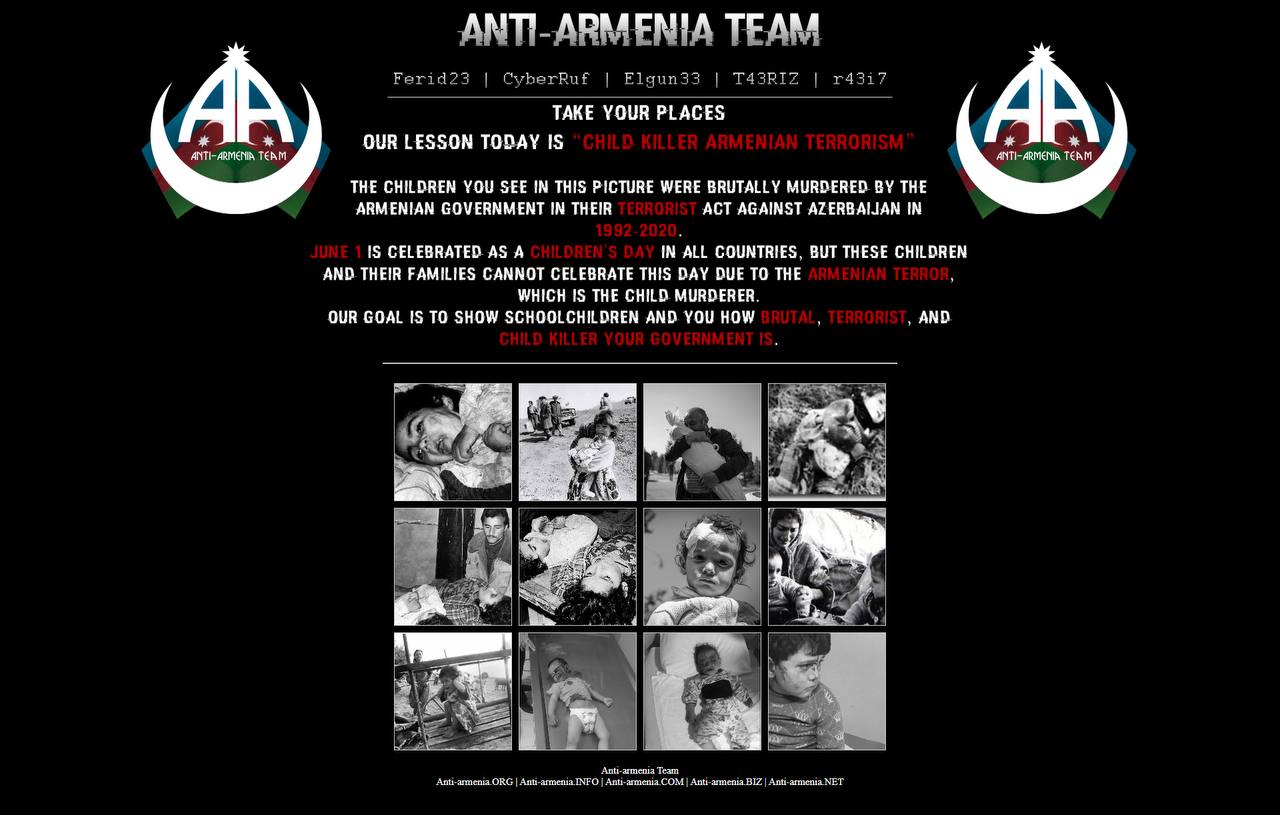
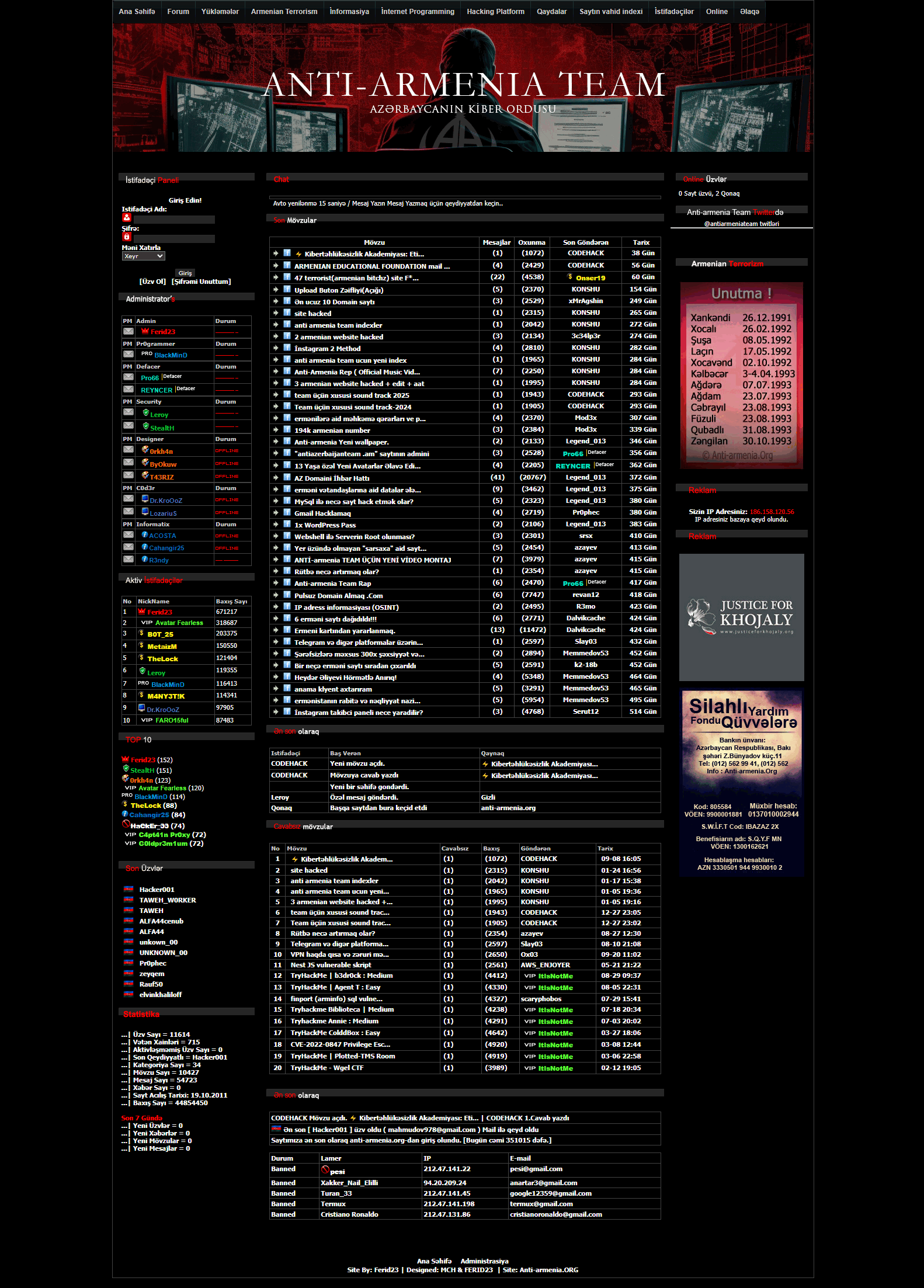
Anti-Armenia Team is a long-running Azerbaijani nationalist hacktivist brand publicly aligned with the Azerbaijan Cyber Army label. Public reporting most consistently associates it with Armenia-focused website compromise, defacement, selective data leaks, and propaganda amplification against politically symbolic targets.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1005 | Data from Local System | TA0009 |
|
| T1567 | Exfiltration Over Web Service | TA0010 |
|
Anti-Armenia Team (Azerbaijan Cyber Army) - Nationalist / conflict-linked hacktivist collective
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Assessed country of origin / home base: Azerbaijan
Executive Summary
Anti-Armenia Team is a long-running Azerbaijani nationalist hacktivist brand that publicly presents itself as part of the “Azerbaijan Cyber Army” ecosystem. Public reporting and the group’s own long-lived online presence indicate an operational focus on Armenia-linked targets, especially government, diplomatic, military-adjacent, and public-facing information resources. The actor’s most consistently observed effects are website defacements, politically framed account compromise, public leak claims, and messaging activity designed to shape perception during moments of interstate tension.
The group should not be modeled as a stealth-heavy espionage actor or a mature crimeware enterprise. Its public footprint is better explained by conflict-driven hacktivism with selective data exposure, symbolic targeting, and propaganda-oriented amplification. Even so, repeated public reporting ties the brand to compromises of Armenian government-linked resources and to conflict-era leak claims, which means the actor remains relevant to regional exposure mapping, influence-aware incident attribution, and public-sector defensive planning.
Anti-Armenia Team is best assessed as an Azerbaijani nationalist hacktivist collective whose identity is explicitly anti-Armenian and whose public branding is closely aligned with wartime or crisis-era messaging. The actor openly frames activity as cyber support to Azerbaijani national interests and publicly links itself to the “Azerbaijan Cyber Army” concept. Its messaging, branding, and victim selection strongly suggest that symbolic political effect is a primary operational objective.
IOC Appendix — Anti-Armenia Team (TLP:WHITE)
Scope & Caveats. This appendix reflects a hacktivist brand with stronger public attribution and social presence than deep technical reporting. As a result, the most reliable indicators are organizational and communications-linked rather than malware-rich. These items are best used for monitoring, enrichment, watchlisting, and correlation; they are not all suitable for blocking.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
