Threat Actor Characterization

313 Team
ID: 08ee9086c28b81c9f13ac2295bec8475| 313 | AL MUJAHIDEEN FORCE 313 | AL********************* | Is******************************** |
| So******************** | Te****** | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
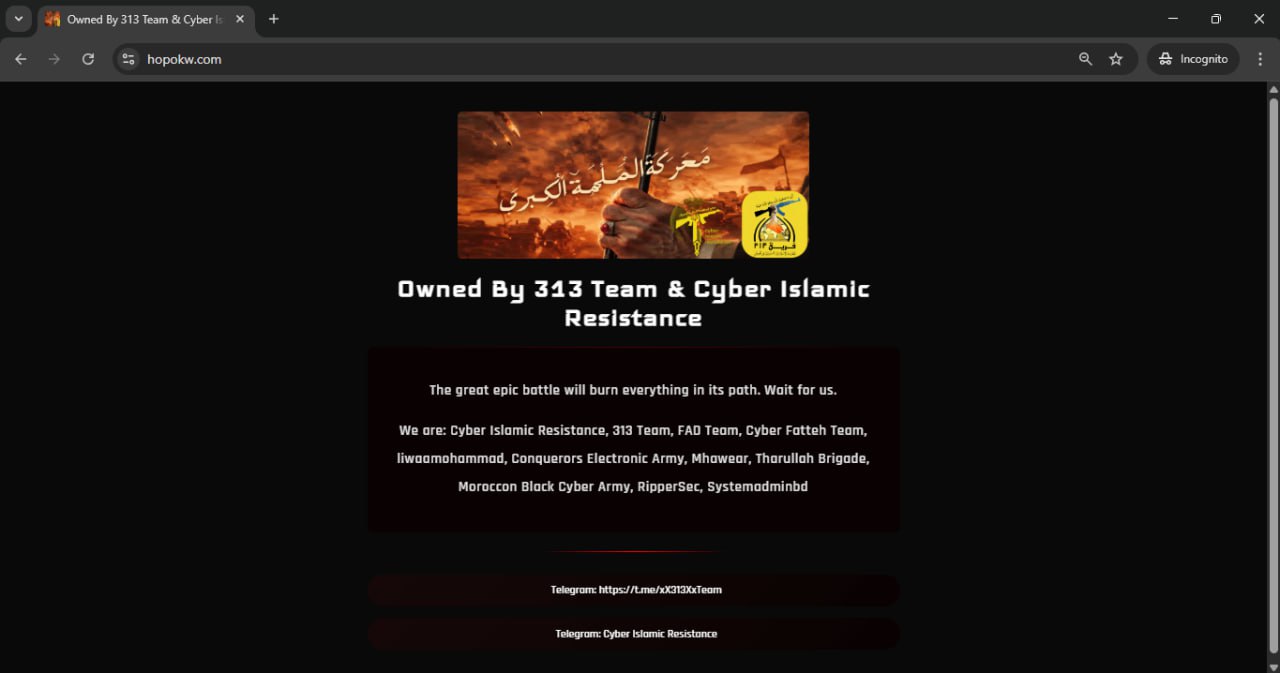
313 Team is a pro-Iran, Shia-aligned hacktivist collective that brands itself as an Islamic cyber resistance group based in Iraq. Public reporting links 313 Team to disruptive DDoS operations against politically symbolic targets such as Truth Social following U.S. strikes on Iranian nuclear facilities, and joint cyberattacks against Saudi government platforms like Qiwa and Absher alongside Yemen Cyber Army and Cyber Islamic Resistance-Axis. The group also promotes its own open-source destructive malware, 313 AlmuntaqimVirus, written in C#, which corrupts the Master Boot Record (MBR), deletes registry keys, and produces visual and audio disturbances for psychological impact. Overall, 313 Team sits in the mid-tier hacktivist band: technically capable of impactful disruption and defacement, tightly coupled to regional ideological narratives, and increasingly integrated into a broader Axis-of-Resistance cyber coalition.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498.001 | Direct Network Flood | TA0040 |
|
| T1498.001 | Direct Network Flood | TA0040 |
|
| T1498.001 | Direct Network Flood | TA0040 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1561.002 | Disk Structure Wipe | TA0040 |
|
| T1485 | Data Destruction | TA0040 |
|
| T1112 | Modify Registry | TA0003 TA0005 |
|
| T1059.003 | Windows Command Shell | TA0002 |
|
| T1565.003 | Runtime Data Manipulation | TA0040 |
|
| T1583.006 | Web Services | TA0042 |
|
| T1585.001 | Social Media Accounts | TA0042 |
|
| T1591 | Gather Victim Org Information | TA0043 |
|
313 Team (a.k.a. Team 313) — Pro-Iranian / “Islamic cyber resistance” hacktivist collective
Classification: TLP:WHITE
Author: iQBlack Team
Executive Summary
313 Team (often branded as “Team 313”) is a pro-Iranian, religiously framed hacktivist collective that positions itself as “Islamic cyber resistance in Iraq, soldiers of Imam Mahdi” on Telegram and related channels. Publicly observed activity is dominated by disruptive operations (primarily DDoS) and propaganda-oriented claims against geopolitical adversaries of Iran, especially the United States, Israel, and Gulf states aligned with them.
In June 2025, 313 Team publicly claimed responsibility for a Distributed Denial-of-Service (DDoS) attack that briefly disrupted Donald Trump’s Truth Social platform shortly after the U.S. announced strikes on Iranian nuclear facilities; this claim was echoed in mainstream media, DHS-linked commentary, and private-sector threat reporting that describe the group as Iran-aligned hacktivists. In September 2025, The Cyber Shafarat reported that 313 Team, together with Yemen Cyber Army and Cyber Islamic Resistance-Axis, conducted a coordinated cyberattack against the Saudi government’s “Qiwa” HR platform, reportedly impacting services for several hours.