Threat Actor Characterization

Mexican Mafia Hackers Team
ID: fb9fd8bad1eb99b5ffd606d3081a039142875| Mexican Mafia | Mexican Mafia ALV | Me**************** | Me********** |
| Me************** | M*** | M** | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Mexican Mafia Hackers Team / Mexican Mafia is a Mexico-focused breach-and-leak cluster linked in public reporting to compromises of government, judicial, police, academic, and selected private-sector targets. Its public operating pattern centers on exploitation of exposed services, bulk data extraction, sample publication, and forum-based sale or release of stolen data.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1213 | Data from Information Repositories | TA0009 |
|
| T1005 | Data from Local System | TA0009 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1595 | Active Scanning | TA0043 |
|
| T1041 | Exfiltration Over C2 Channel | TA0010 |
|
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Cybercrime / Breach-and-Leak / Opportunistic Intrusion Cluster — Origin: Mexico (assessed)
Author: iQBlack CTI Team
Executive Summary
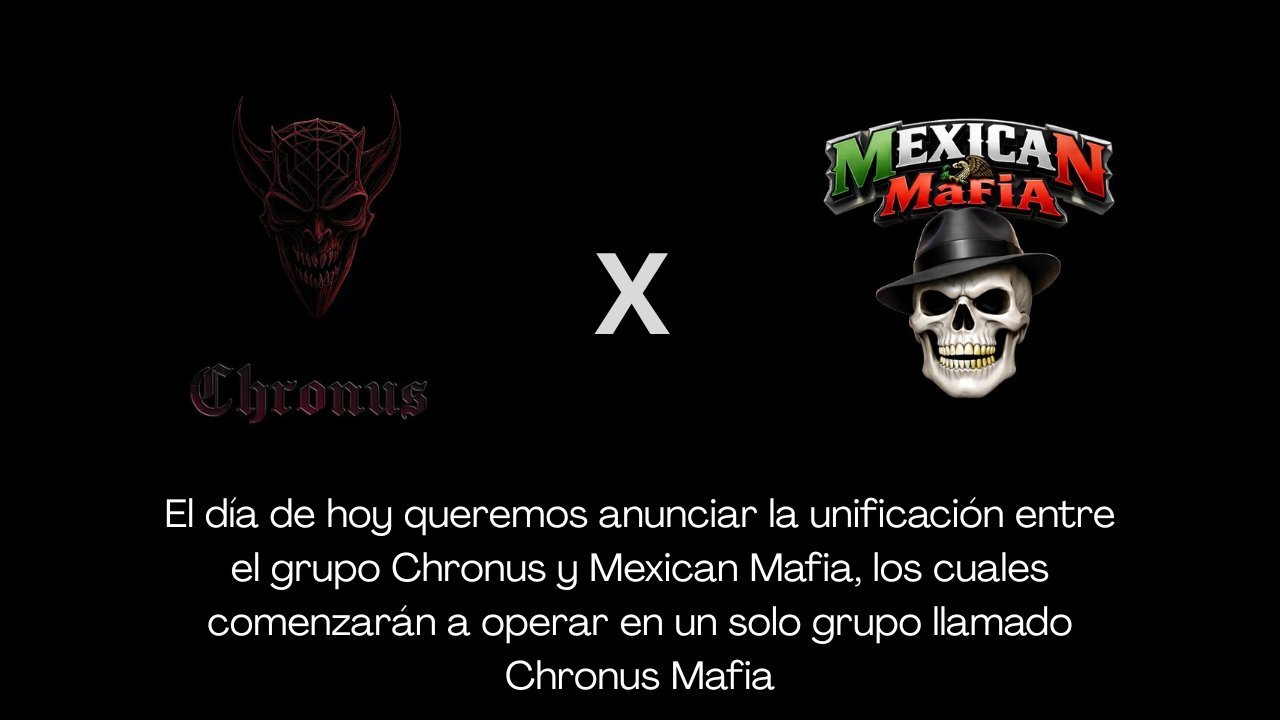
Mexican Mafia Hackers Team, also referred to publicly as Mexican Mafia, is best assessed as a Mexico-focused cyber intrusion and data-leak cluster that gained visibility during 2024 through a rapid sequence of breaches, leak sales, and public humiliation operations affecting Mexican government entities, academic institutions, and selected private-sector organizations. Public reporting repeatedly associates the cluster with the handles Pancho Villa, Lord Peña, Dyce, and a smaller set of recurring aliases. Confidence is medium: the victim pattern and recurring actor labels are consistent, but many specific claims still come from actor-controlled or actor-amplified channels.
The cluster’s operational profile is not that of a mature ransomware program or a high-end espionage unit. Instead, it appears to revolve around opportunistic compromise of exposed services, extraction of large volumes of e-mails or database content, selective free release of samples to prove access, and subsequent sale or threatened release through criminal forums. In several reported cases, the group appears to have exploited weak public-facing infrastructure and outdated web or mail platforms rather than advanced custom tooling.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
