Threat Actor Characterization
You’re viewing the read-only version.
Sign in for analyst tools (editors, promote draft, file/relations management, etc.)

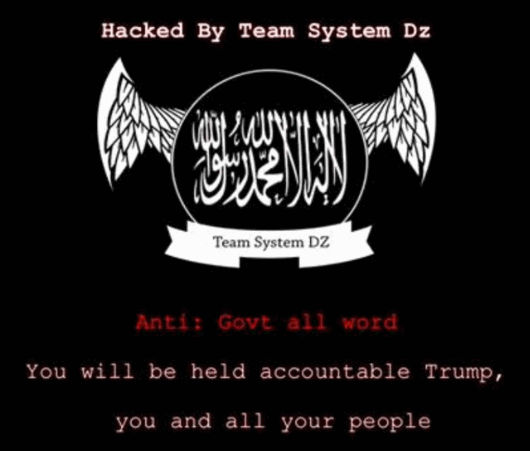
Team System DZ
ID: fb621df16aebfebcc1c84d62bfa875e7
Hacktivist Group
Collective
CyberTerrorism
Defacement Crew
Hacktivism
Threat types: Pro-ISIS, Cyberterrorism, DDoS, Defacement, Propaganda
Progress: 85%
Completeness: 92%
Freshness: 70%
Operation zone: Belize, Dominican Republic, France, Germany, Iran, Israel, Italy, Netherlands, Nigeria, Peru, Romania, United Arab Emirates, United States
Aliases
Limited alias preview
| Team System DZ | TeamSystemDZ | T**** | ٹی********* |
Showing 2 of 4 aliases in free preview.
Actor Network Graph
Open Network GraphMITRE ATT&CK®
confidence: medium-high
Team System DZ is described in OSINT as a low-sophistication defacement actor aligned in reporting with pro-ISIS/Daesh propaganda messaging. Activity is primarily opportunistic compromise of public-facing websites (often weak/outdated CMS or credentials) followed by homepage defacement and claim amplification.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1595 | Active Scanning | TA0043 |
|
| T1110 | Brute Force | TA0006 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1491.002 | External Defacement | TA0040 |
|
| T1585 | Establish Accounts | TA0042 |
|
Executive brief
now
Saved successfully.
Hunting Playbook — Team System DZ (Defacement-focused)
Purpose: Detect and disrupt opportunistic web compromise leading to propaganda defacement, with emphasis on WordPress/CMS brute force, exploit probing, unauthorized content changes, and post-defacement persistence (webshells). This actor class is “low sophistication, high optics,” so the decisive advantage is hygiene + fast integrity detection + rapid rollback.
Tip: Hover the section title to learn what’s included in Analyst / Premium plans.
Hunting Playbook
now
Saved successfully.
IOC Appendix
now
Saved successfully.
OSINT Library
now
Saved successfully.