Threat Actor Characterization

Armenian Code
ID: f2b22cd5501a6ec54f0e5999723d136231259| Armenian Code Group | Armenian Code Team | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Armenian Code is an emerging pro-Armenian hacktivist cluster publicly observed in March 2026. Current reporting ties it to claimed DDoS-style disruption against Turkish defense-sector companies and to screenshot-based claims of access to symbolic control-system interfaces in Turkey and Azerbaijan. Confidence is highest for public branding and ideological targeting, and lower for sustained OT/ICS intrusion capability.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1595 | Active Scanning | TA0043 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
Armenian Code — Armenian nationalist hacktivist cluster with anti-Turkish / anti-Azerbaijani targeting claims
Classification: TLP:WHITE - Open Source Intelligence (OSINT)
Category: Hacktivism / Nationalist cyber activism - Origin: Assessed Armenian / pro-Armenian online milieu
Author: iQBlack CTI Team
Executive Summary
Armenian Code is best assessed as a small, publicly branded, pro-Armenian hacktivist cluster that emerged in open reporting during March 2026. The group’s observable activity is centered on public claims, social-media amplification, and ideologically framed targeting of Turkish and Azerbaijani entities, especially symbolic or politically resonant targets.
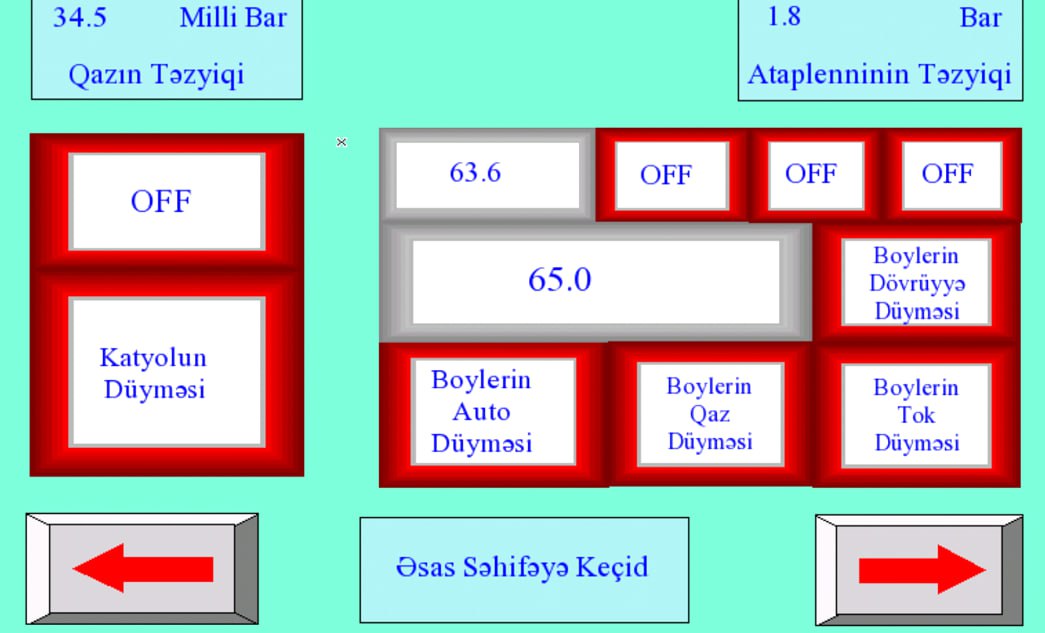
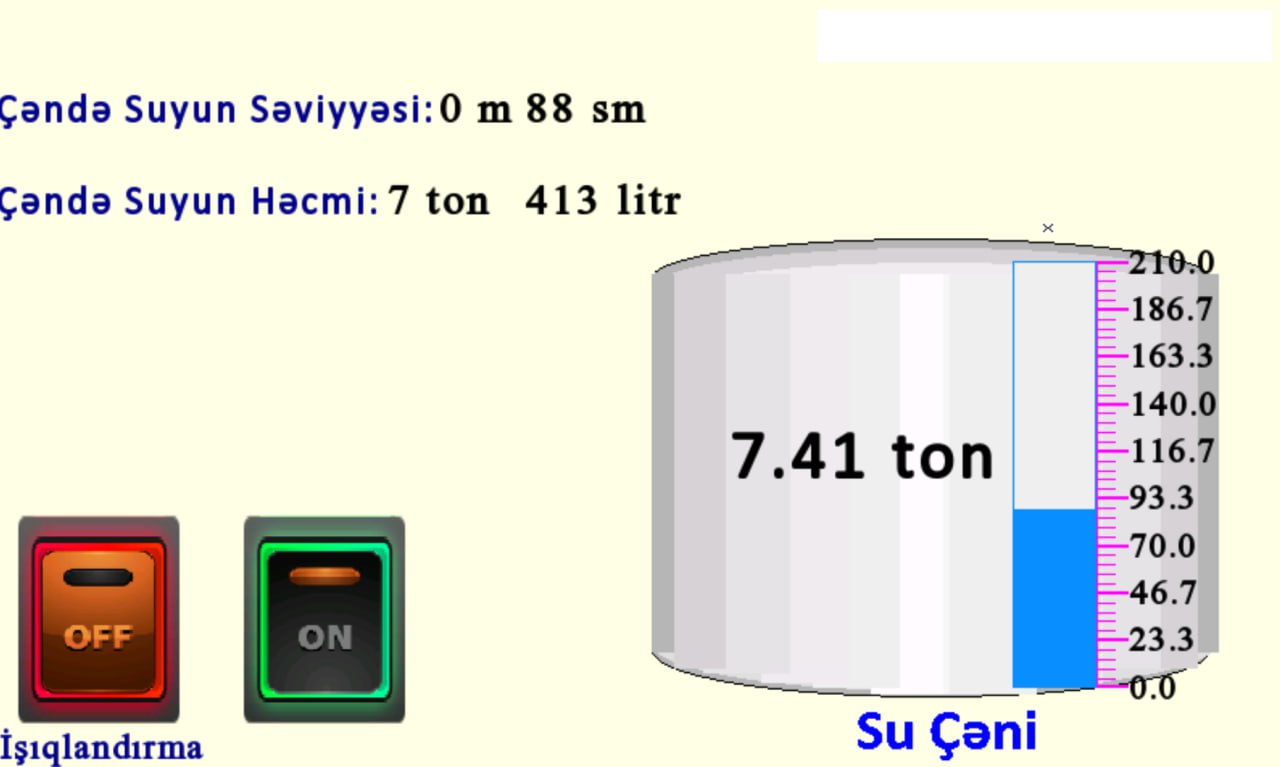
Public reporting and social-media traces indicate two main lines of activity. First, the group publicly claimed disruptive operations against Turkish defense-related companies and Turkish websites. Second, posts attributed to the group showcased screenshots allegedly showing access to irrigation, climate-control, and heating-control interfaces in Turkey and Azerbaijan. These intrusion-style claims materially increase concern, but the evidentiary base remains limited because the current record relies heavily on screenshots, reposts, and secondary reporting rather than independent forensic validation.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
