Threat Actor Characterization

OverFlame
ID: ee7c9196a35cc624774e641bf7962efcActor Network Graph
Open Network GraphMITRE ATT&CK®
OverFlame is a pro-Russia-aligned hacktivist brand frequently referenced in OSINT as an active participant in coalition-style DDoS campaigns (including co-activity with NoName057(16)) and as a member of coalition constructs such as the 'Holy League'. Multiple sources also associate OverFlame with alliances in the pro-Russian OT/critical-infrastructure hacktivist ecosystem (e.g., Sector16/Z-Pentest adjacency and infrastructure sharing narratives). Evidence strongly supports DDoS disruption and propaganda/cross-promotion; OT/ICS intrusion capability is treated as variable and marked INFERENCE where not independently validated.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 | |
| T1585.001 | Social Media Accounts | TA0042 | |
| T1583.006 | Web Services | TA0042 |
|
| T1595 | Active Scanning | TA0043 |
|
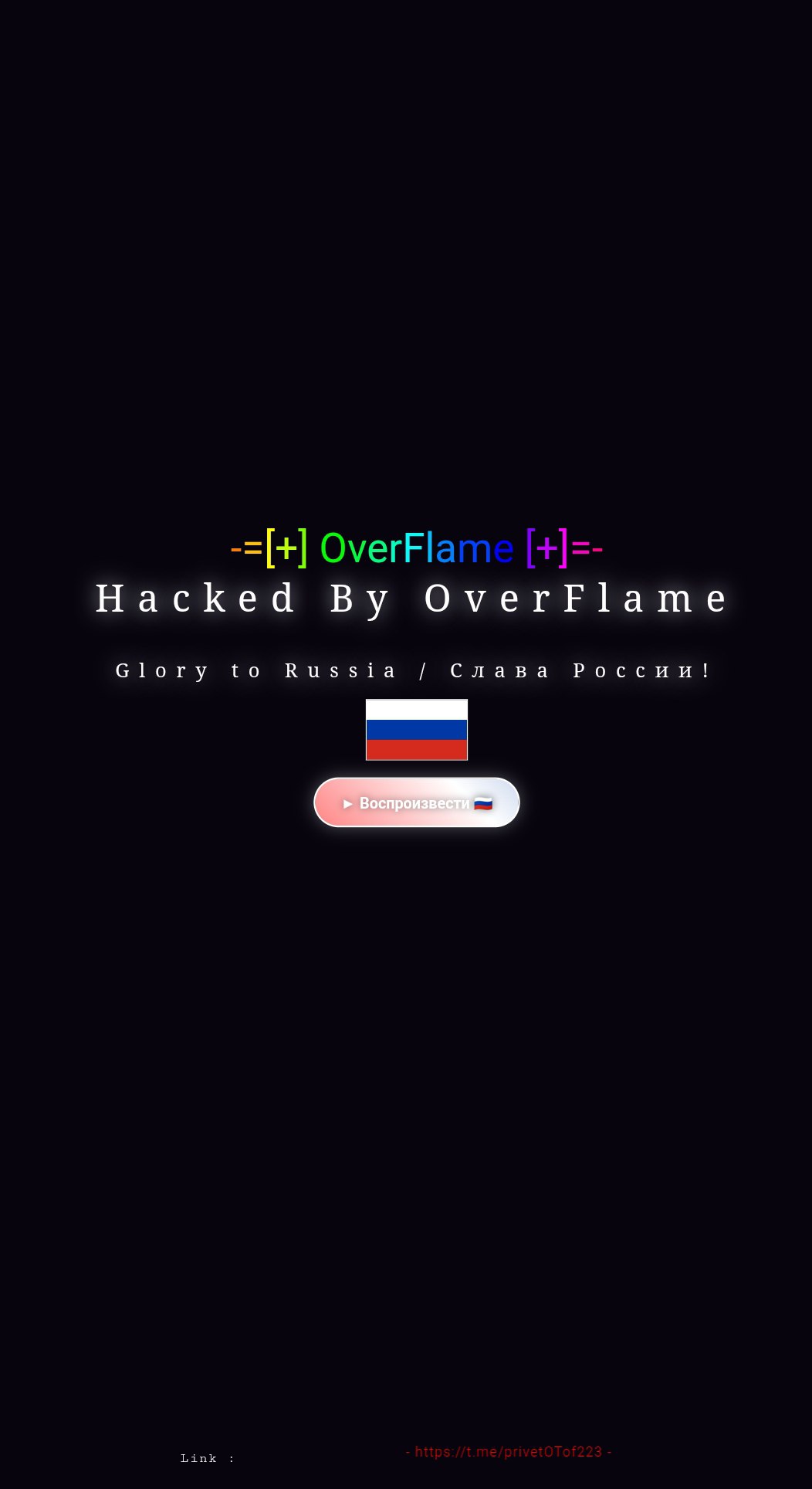
OverFlame — Pro-Russia-Aligned Hacktivist Brand (DDoS Coalition Member; OT/CI Narrative Adjacency)
Classification: TLP: WHITE — Open Source Intelligence (OSINT)
Category: Cyber / Hacktivism — DDoS disruption + coalition-driven propaganda; occasional critical-infrastructure narrative adjacency
Assessed home base: Unclear / transnational; consistently described as pro-Russia-aligned in OSINT
Executive Summary
OverFlame is a pro-Russia-aligned hacktivist brand repeatedly referenced in OSINT as an active participant in DDoS campaigns and coalition structures. In 2024, the actor is described as part of hacktivist “coalitions” and as operating alongside NoName057(16) in prominent DDoS waves (e.g., Austria-focused targeting ahead of elections). OSINT also places OverFlame within a broader ecosystem of pro-Russian hacktivist alliances that cross-promote and share operational capacity.
From 2025 onward, reporting increasingly links OverFlame to OT/critical-infrastructure narratives through collaboration/adjacency with Sector16 and Z-Pentest ecosystems, including claims of unauthorized access to industrial control interfaces. These OT-related claims are often framed as intimidation (“proof-of-access” screenshots/videos) and should be treated as variable-impact without victim-side validation.
Confidence is high that OverFlame is a real, active hacktivist brand participating in pro-Russia-aligned DDoS campaigns and coalition messaging. Confidence is medium regarding the actor’s direct OT/ICS intrusion capability, because much of the linkage appears via alliances, shared infrastructure narratives, and claim-driven reporting rather than consistent, independently validated technical artifacts.