Threat Actor Characterization

Monte Melkonian Cyber Army
ID: e6772ccc6d804c7dbe76489cd77df26376617| MMCA | MonteMelkonianCyberArmy | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
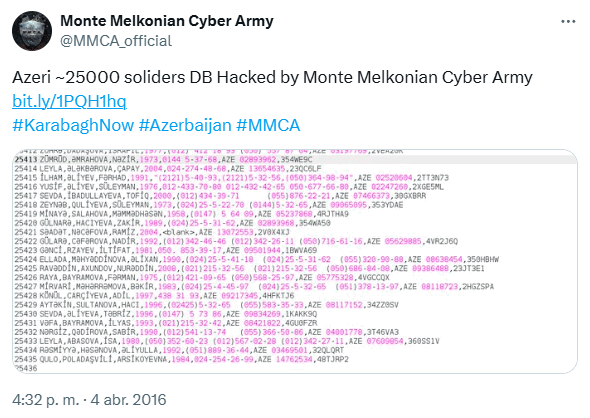
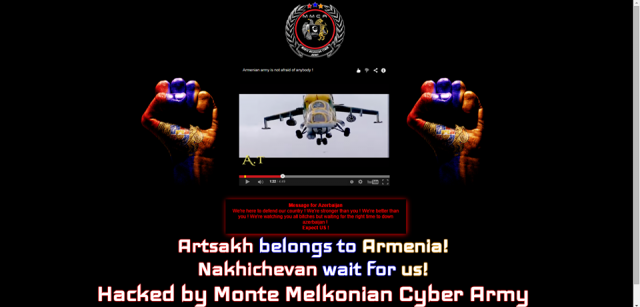
Monte Melkonian Cyber Army (MMCA) — Armenian hacktivist label active in at least 2015–2020. Open sources attribute to MMCA multi-site defacements (incl. state sites), forum compromise with database exposure, and a 2020 operation claiming access to Azerbaijani government email systems and large-scale document leakage; one report alleges destructive impact against an Azerbaijani agribusiness network.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1491.002 | External Defacement | TA0040 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1041 | Exfiltration Over C2 Channel | TA0010 |
|
| T1486 | Data Encrypted for Impact | TA0040 |
|
| T1490 | Inhibit System Recovery | TA0040 |
|
Monte Melkonian Cyber Army (MMCA) Hacktivist Group
CLASSIFICATION: Unclassified / Open Source
Executive Summary
Open sources place the Monte Melkonian Cyber Army (MMCA) as an Armenian hacktivist label with observed activity from 2015 to 2020. Credible media report multi-site defacements including state domains and exposure of personal data (2015) and a forum compromise with database leak claims (2017). During the 2020 Nagorno-Karabakh escalation, MMCA claimed access to Azerbaijani government email systems and released ~1GB of documents; a separate report alleges destructive impact against a major agribusiness network (encryption, backup deletion). While the branding invokes the legacy of Monte Melkonian, evidence linking MMCA to designated terrorist organizations is not established in open sources; any such link remains unproven. Overall confidence is medium, based on multiple independent outlets echoing MMCA claims and artifacts of release, balanced against limited primary technical detail and reliance on revendicative statements.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
