Threat Actor Characterization
CrX
ID: e34a66d4e43067ac1a5729fb9402bdb9Actor Network Graph
Open Network GraphMITRE ATT&CK®
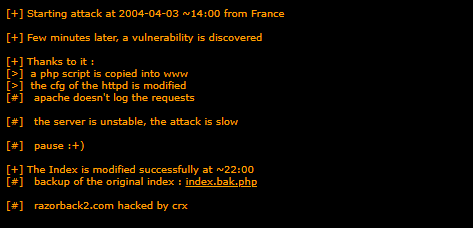
“crx” — individual web defacer active circa 1999–2004 with multiple page takeovers recorded in Zone-H mirrors. Trademark strings observed include “Hacked by crx”, “CRX OWNZU”, and Spanish-language insults; one detailed narrative (razorback2.com, 2004-04-03) describes discovery of a vulnerability, uploading a PHP script to the webroot, modifying the HTTPD configuration, disabling logging, and replacing index. Possible alternate handle mentioned in a conflict post: “Kastro” (unconfirmed).
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1491.002 | External Defacement | TA0040 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1562.002 | Disable Windows Event Logging | TA0005 |
|
CLASSIFICATION: Unclassified / Open Source
Executive Summary
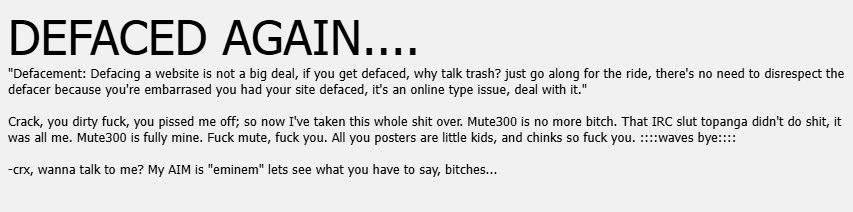
crx appears in multiple historical mirrors (Zone-H era) as an individual defacer active from at least 1999 to 2004, leaving minimalist strings such as “Hacked by crx”, “CRX OWNZU”, and, in one case, Spanish-language profanity accompanied by a Mexican flag image. A detailed write-up on razorback2.com (2004-04-03) describes discovering a vulnerability, uploading a PHP script to the webroot, modifying the HTTPD configuration, disabling Apache logging, and replacing index (with a backup saved as index.bak.php). A longer, combative message on mute300.net (1999) includes an AIM handle reference and taunts; within that text the name “Kastro” appears, but linkage as an alias remains unverified. Overall, the evidence supports a profile of a solo defacer executing opportunistic exploitation and page replacement across disparate targets. Confidence: medium.
- mute300.net — lengthy deface note signed -crx; claims full takeover and taunts administrators; mentions “Kastro” within the rant (possible alias, unconfirmed).
- 2004-04-03. razorback2.com — narrative states attack “starting … from France”, “vulnerability is discovered”, PHP script copied into www, HTTPD config modified, Apache logging disabled, index replaced; ends “razorback2.com hacked by crx”.
- Undated (early 2000s). accounts.usc.edu.tt — banner “Hacked by crx”, Mexican flag image, Spanish profanity.
- Undated (early 2000s). Multiple hosts show “CRX OWNZU” or “hacked by crx” strings (scripts-zone.com, portailduhack.freegaia.net, security-corporations.com, gueux.net, dark-sign.com, harnois.biz).
- Possible alternate handle: “Kastro” — appears only inside the mute300.net rant; no independent infrastructure or campaign continuity found. INFERENCE (confidence: low).
- Operational behaviors: Opportunistic web defacements across heterogeneous targets; in at least one case, post-exploitation hardening to reduce traces (turning off web logs).
- Geographic hints:
- Mexican flag + idiomatic Spanish insult suggest Mx-themed signaling on accounts.usc.edu.tt.
- “Starting … from France” on razorback2.com indicates either French vantage (proxy/host) or physical presence at the time; not dispositive of nationality.
- English in 1999 post is fluent colloquial US-slang with minor errors—consistent with a heavy-exposure non-native or a native speaker; MT quality in 1999 was poor, so fluency likely genuine. INFERENCE (confidence: low–medium).