Threat Actor Characterization
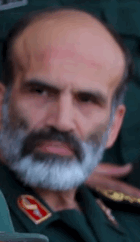
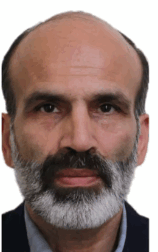
Hamid Reza Lashgarian
ID: dc8eceafd88a3bf25d2d43d57b6c4d3499330| Hamidreza Lashgarian | حمیدرضا لشگریان | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Hamid Reza Lashgarian is the publicly identified head of the IRGC Cyber-Electronic Command (IRGC-CEC) and a commander in the IRGC-Qods Force. He is best assessed as a state cyber leadership figure linked to the command structure behind CyberAv3ngers and related critical-infrastructure cyber activity.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1110 | Brute Force | TA0006 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1565.001 | Stored Data Manipulation | TA0040 |
|
| T1595 | Active Scanning | TA0043 |
|
| T1059.004 | Unix Shell | TA0002 |
|
| T1059.006 | Python | TA0002 |
|
| T1105 | Ingress Tool Transfer | TA0011 |
|
| T1583.001 | Domains | TA0042 |
|
Hamid Reza Lashgarian
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Author: iQBlack CTI Team
Executive Summary
Hamid Reza Lashgarian is publicly identified by the U.S. Department of the Treasury and Rewards for Justice as the head of the Islamic Revolutionary Guard Corps Cyber-Electronic Command (IRGC-CEC) and, simultaneously, as a commander in the IRGC-Qods Force. In open sources, this makes him one of the clearest named senior officials tied to the state-linked command structure behind the CyberAv3ngers ecosystem and related malicious cyber activity affecting critical infrastructure.
Public reporting does not present Lashgarian as a noisy online “handle” or a visible operator persona. Instead, he appears as a senior command-and-control figure whose significance derives from organizational leadership, state authority, and linkage to a broader portfolio of Iranian cyber and intelligence operations. His relevance to defenders therefore lies less in direct attribution of hands-on keyboard activity to him personally, and more in understanding the leadership node that appears to sit above operational brands, front companies, and supporting personnel.
Hunting Playbook — Hamid Reza Lashgarian
Priority: High for OT/ICS-heavy organizations, critical infrastructure operators, water/wastewater, fuel-management environments, and enterprises with internet-exposed industrial devices.