Threat Actor Characterization

Cyber Support Front
ID: bb459fd9ec3557e894d7ae2bc86a34ed| Al-Isnad al-Sibarania Front | al-Jabha al-Isnad al-Sayberaniyah | C**** | C** |
| C***** | Cy**************** | Fr*************************** | ال*********************** |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Cyber Support Front is a pro-Palestinian, anti-Israel hybrid hacktivist/proxy-style brand that emerged in June 2025 during Israel-Iran escalation. Public reporting most strongly supports Telegram-led threat signaling, DDoS/disruption narratives, selective leak publication, and claim-heavy operations against Israeli critical infrastructure, communications, and defense-adjacent targets.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 |
|
| T1567 | Exfiltration Over Web Service | TA0010 |
|
| T1087 | Account Discovery | TA0007 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1485 | Data Destruction | TA0040 |
|
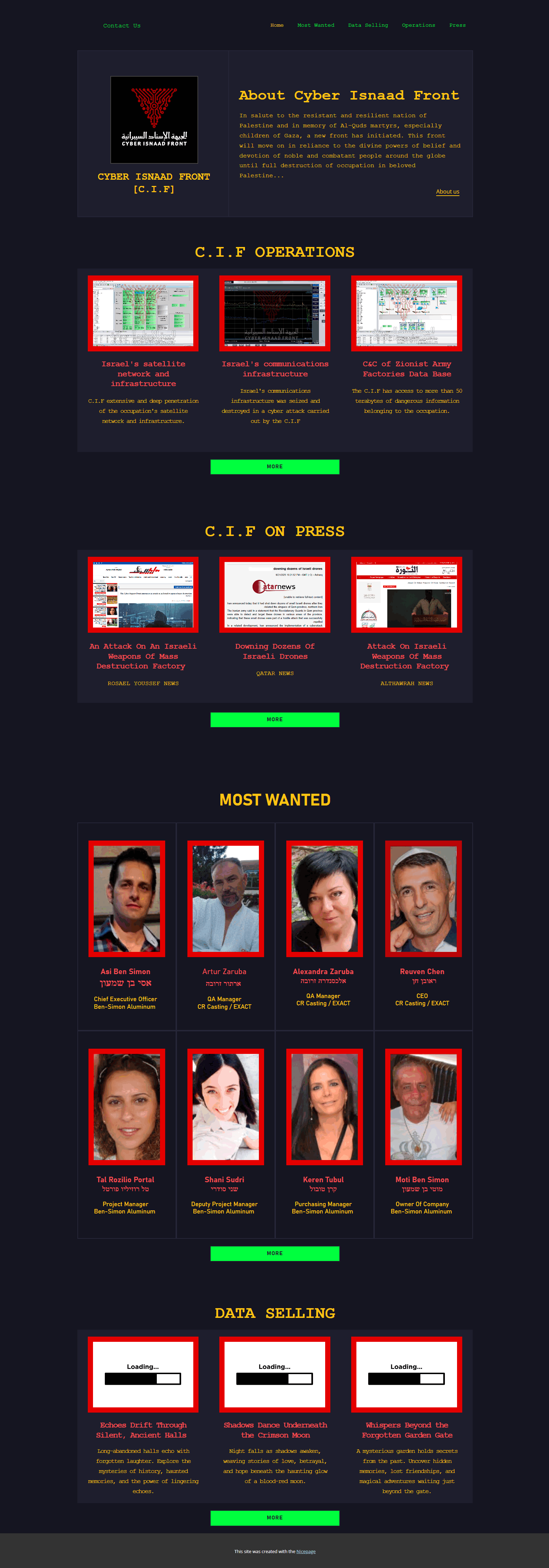
Cyber Support Front / al-Jabha al-Isnad al-Sayberaniyah / Cyber Isnaad Front
Classification: TLP:WHITE — (Cyber / Pro-Iran Hybrid Hacktivist Brand / Crisis-Era Influence-and-Disruption Persona)
Author: iQBlack Team
Executive Summary
Cyber Support Front is a pro-Palestinian, anti-Israel cyber actor brand that publicly emerged on 2025-06-19 amid the rapid escalation of direct and proxy confrontation between Israel and Iran. In its founding statement, the group described itself as a cyber front composed of experts from several Arabic countries and explicitly aligned its activity with the “resistance front” against Israel. Public reporting from 2025 through early 2026 places the actor inside the broader ecosystem of pro-Iran and “axis of resistance” hacktivist messaging that intensified around wartime events, especially against Israeli critical infrastructure, government communications, and defense-adjacent targets.
The strongest open-source evidence for Cyber Support Front concerns public declarations, Telegram-centered propaganda, threat signaling, leak publication, and crisis-time amplification. Its most notable publicized incident was the late-2025 claim that it had compromised Maya Defense Industries and obtained information connected to Israel’s Iron Beam and other advanced systems. In early March 2026, the group again claimed a large operation against Israeli military and government communications infrastructure. These claims received amplification through Iranian and pro-Iran media channels, but independent technical validation remains partial and uneven.
OSINT Library — Cyber Support Front
2025-06-19 — Tasnim News Agency — "Anti-Israeli Cyber Group Vows to Target Zionists’ Infrastructures"