Threat Actor Characterization

RMRF Group
ID: aec70f53e5c42b4234c59d6e9c90ed6f92527| ReMove -RussianFederation | ReMove RussianFederation | Re********************** | R**** |
| RM********* | R*** | RM******* | su******** |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
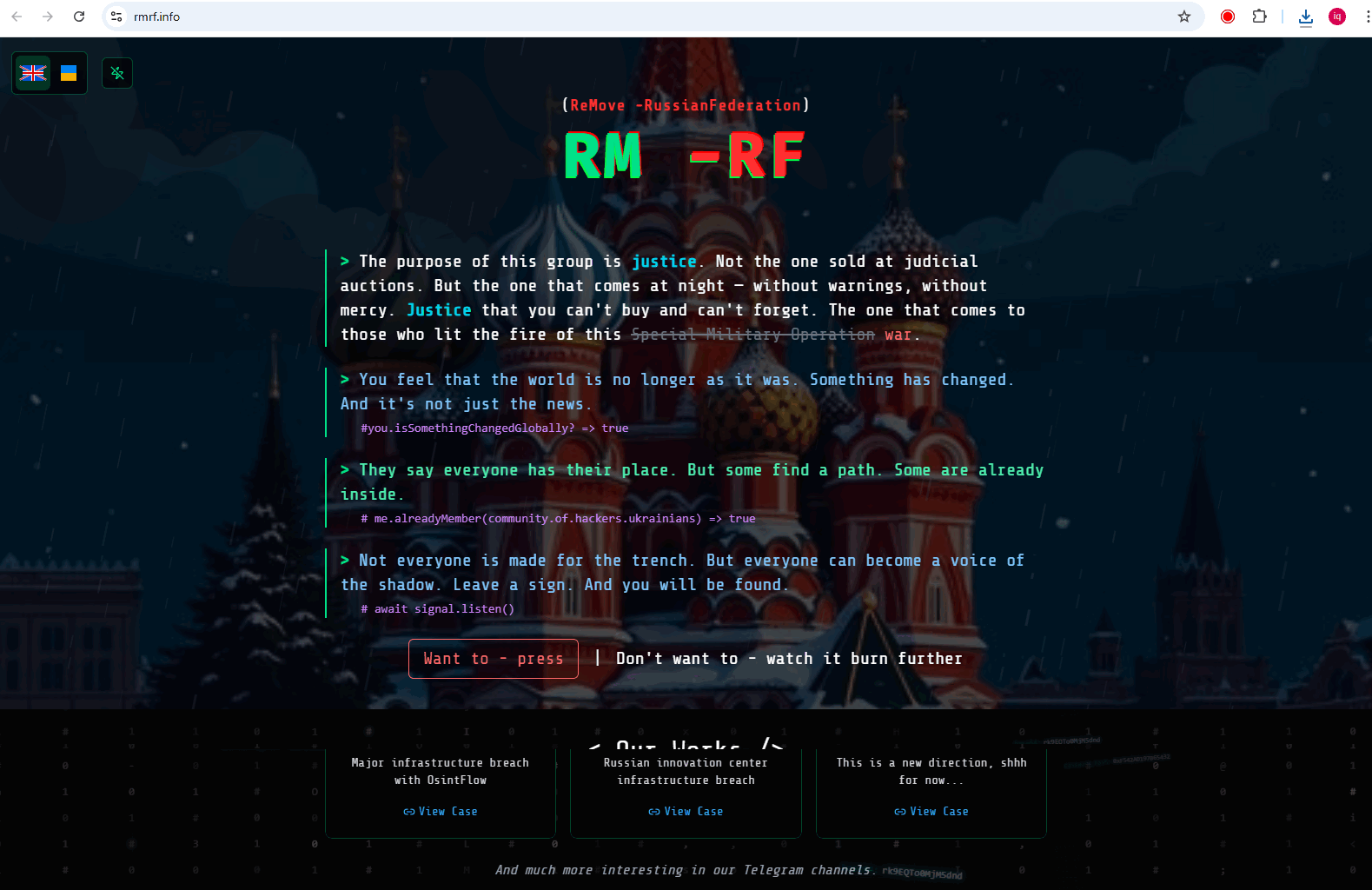
RMRF Group (a.k.a. sudo rm -RF, “ReMove-RussianFederation”) is a pro-Ukraine hacktivist collective linked by public claims to high-impact disruptions and alleged data/backups destruction against Russian entities, including the 2024-10 attack on state broadcaster VGTRK and a 2023-08 breach claim against MosgorBTI.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1485 | Data Destruction | TA0040 | |
| T1491.002 | External Defacement | TA0040 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1565.001 | Stored Data Manipulation | TA0040 |
|
CLASSIFICATION: Unclassified / Open Source Intelligence (OSINT)
Category: Cyber / Hacktivism — Origin: Ukraine-aligned (public claims since 2023)
Executive Summary
RMRF Group —frequently stylized as sudo rm -RF— is a pro-Ukraine hacktivist collective that conducts high-impact operations against Russian entities, prioritizing disruption and data destruction and publicly showcasing results. On 2023-08-07, the group claimed to have compromised MosgorBTI (the Moscow real-estate registry) and transferred information on officials and security forces to Ukrainian authorities.
On 2024-10-07, multiple outlets reported an “unprecedented” intrusion against the state corporation VGTRK (Russian television and radio) coinciding with Putin’s birthday; sources attributed the operation to sudo rm -RF, with allegations of backup deletion and outages on dozens of channels.
The operational pattern emphasizes large-scale attacks and rapid disclosure via Telegram/media to maximize reputational effects. Assessed capability: moderate-to-high for disruption and wiping; low public evidence of custom malware. Analytic confidence: high for publicly reported incidents/attribution to sudo rm -RF; medium for internal tactical details.