Threat Actor Characterization
Millenium RAT
ID: ad253209ab14560e6435956c924425c062843| MilleniumRAT | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
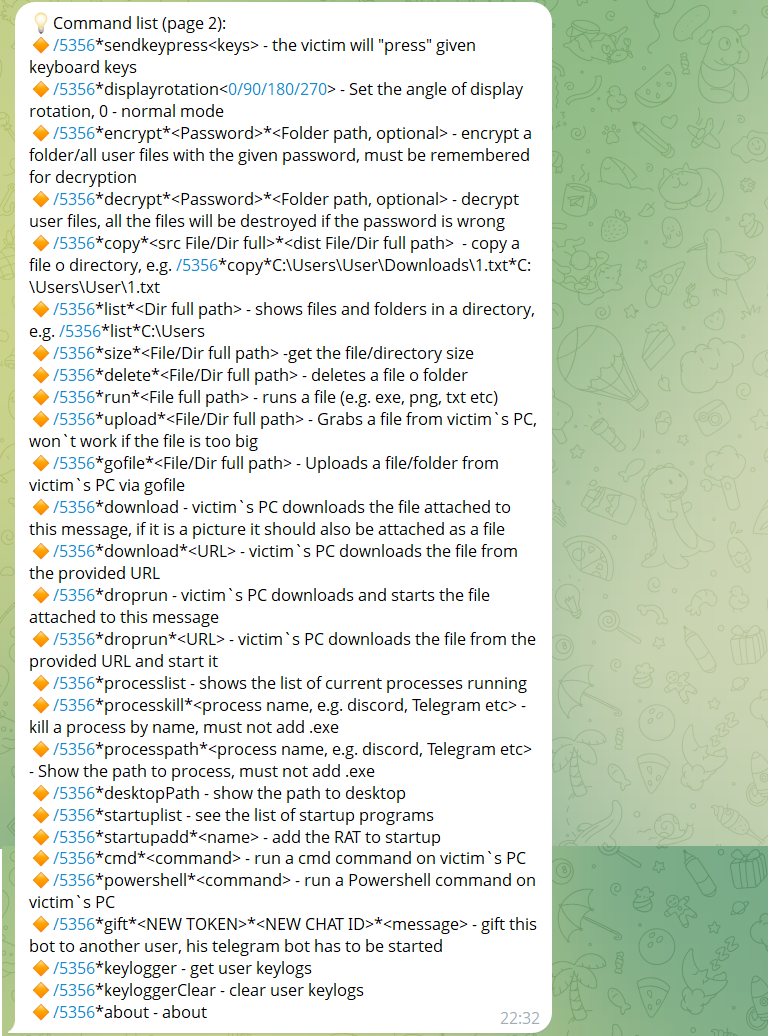
Millenium RAT is a Windows-focused commodity remote access trojan and stealer publicly marketed through GitHub-linked exposure, a dedicated website, and direct-contact channels. Public reporting and operator-controlled sources show Telegram-based control, credential theft, keylogging, anti-analysis features, and optional persistence and disruptive functions.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1102.002 | Bidirectional Communication | TA0011 |
|
| T1555 | Credentials from Password Stores | TA0006 | |
| T1539 | Steal Web Session Cookie | TA0006 |
|
| T1056.001 | Keylogging | TA0006 TA0009 | |
| T1082 | System Information Discovery | TA0007 | |
| T1497.001 | System Checks | TA0005 TA0007 | |
| T1622 | Debugger Evasion | TA0005 TA0007 |
|
| T1059.001 | PowerShell | TA0002 |
|
| T1059.003 | Windows Command Shell | TA0002 |
|
| T1547.001 | Registry Run Keys / Startup Folder | TA0003 TA0004 |
|
| T1125 | Video Capture | TA0009 |
|
| T1005 | Data from Local System | TA0009 |
|
| T1204 | User Execution | TA0002 |
|
| T1486 | Data Encrypted for Impact | TA0040 |
|
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Malware / Remote Access Trojan (RAT) / Stealer — Origin: Unclear; public sales and developer-facing channels are openly exposed online.
Author: iQBlack CTI Team
Executive Summary
Millenium RAT is a commodity Windows remote access trojan and stealer family publicly marketed through GitHub-linked exposure, a dedicated website, and direct messaging channels. Public reporting from late 2023 first documented versions 2.4 and 2.5, while operator-controlled infrastructure visible in 2025–2026 indicates continued development into the 4.x branch.
The malware is notable less for elite tradecraft than for accessibility, modularity, and the low barrier it creates for less-skilled operators. Publicly advertised features include Telegram-based command-and-control, browser credential and cookie theft, Discord token theft, Telegram data access, keylogging, webcam/microphone capture, privilege elevation, startup persistence, anti-VM and anti-debug logic, and optional destructive or disruptive actions such as encrypting user files or forcing a BSOD.