Threat Actor Characterization

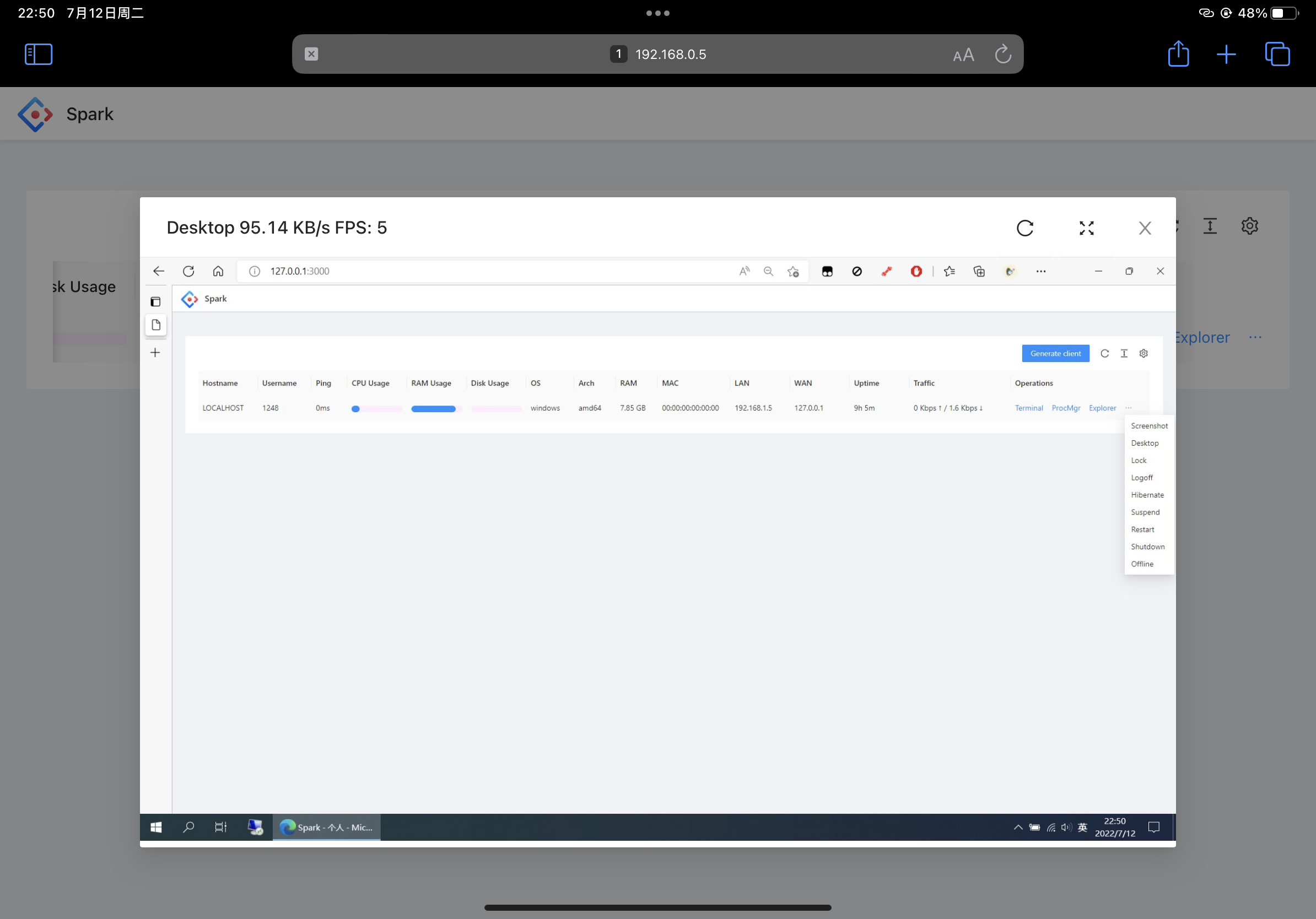
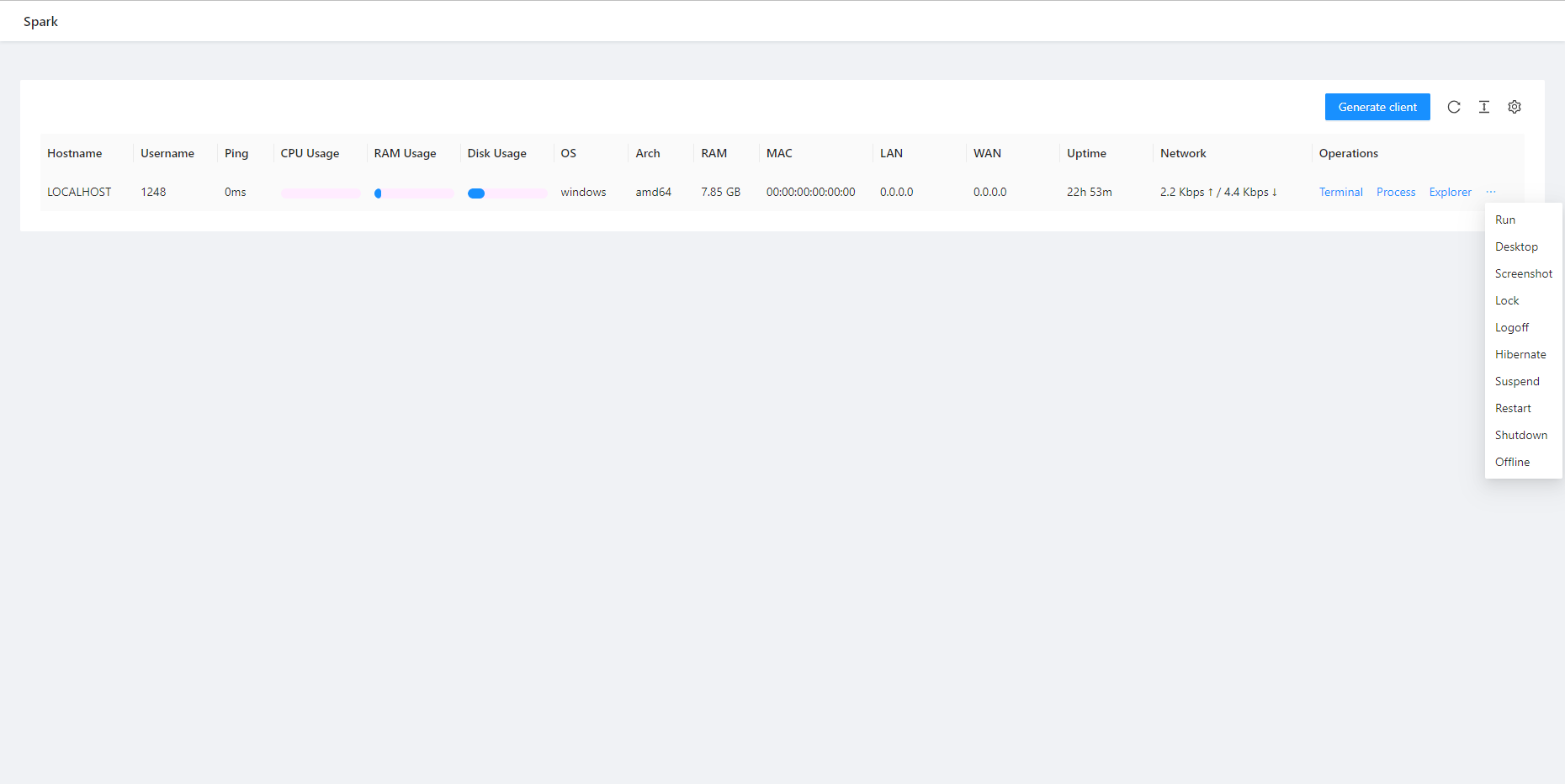
SparkRAT
ID: ad0437fa157c5a6a576424134e671cae32408| Spark | Spark RAT | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
SparkRAT is an open-source, cross-platform Go-based RAT and server/panel used as a post-compromise remote administration capability across multiple threat clusters and campaigns.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
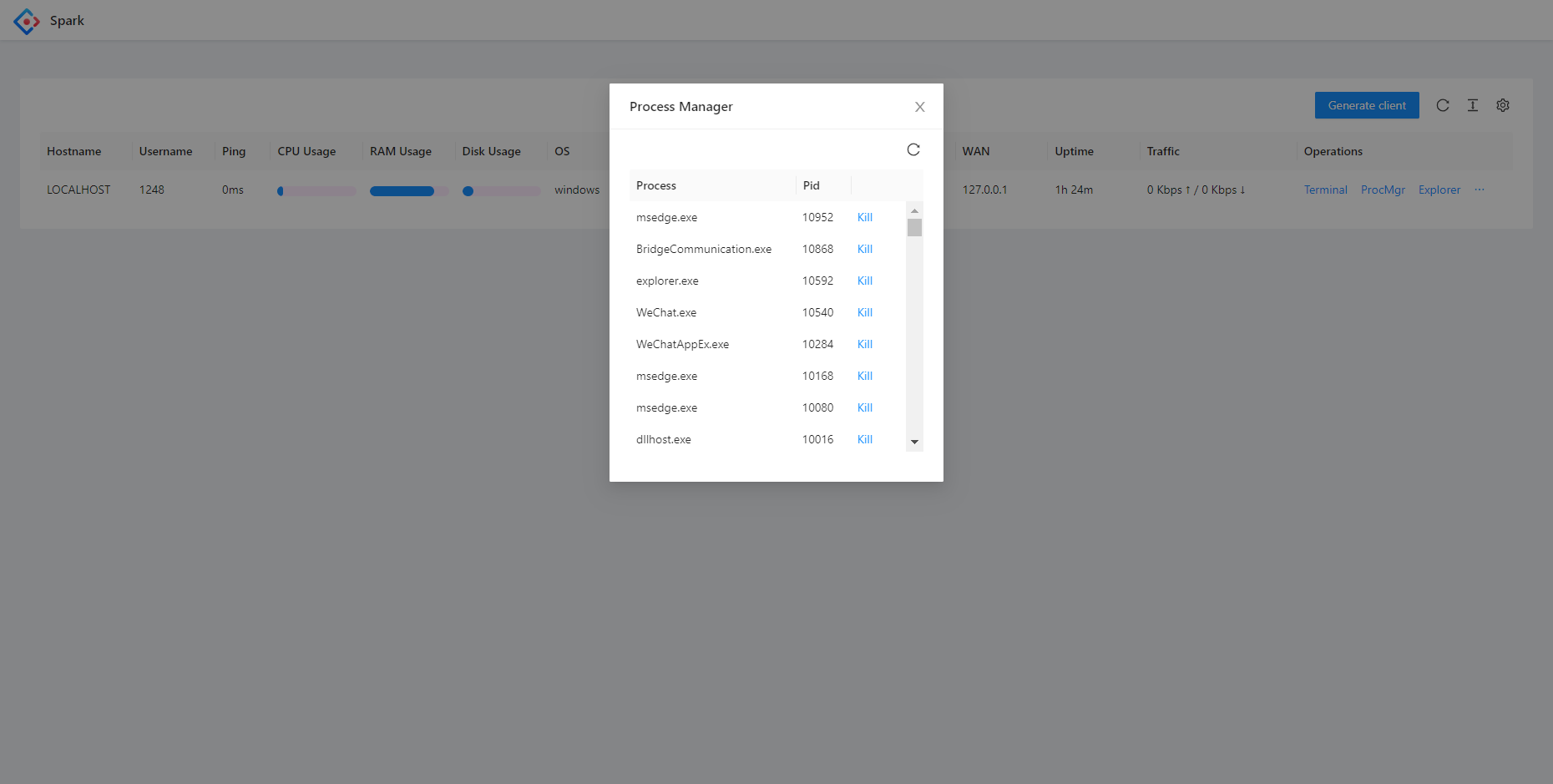
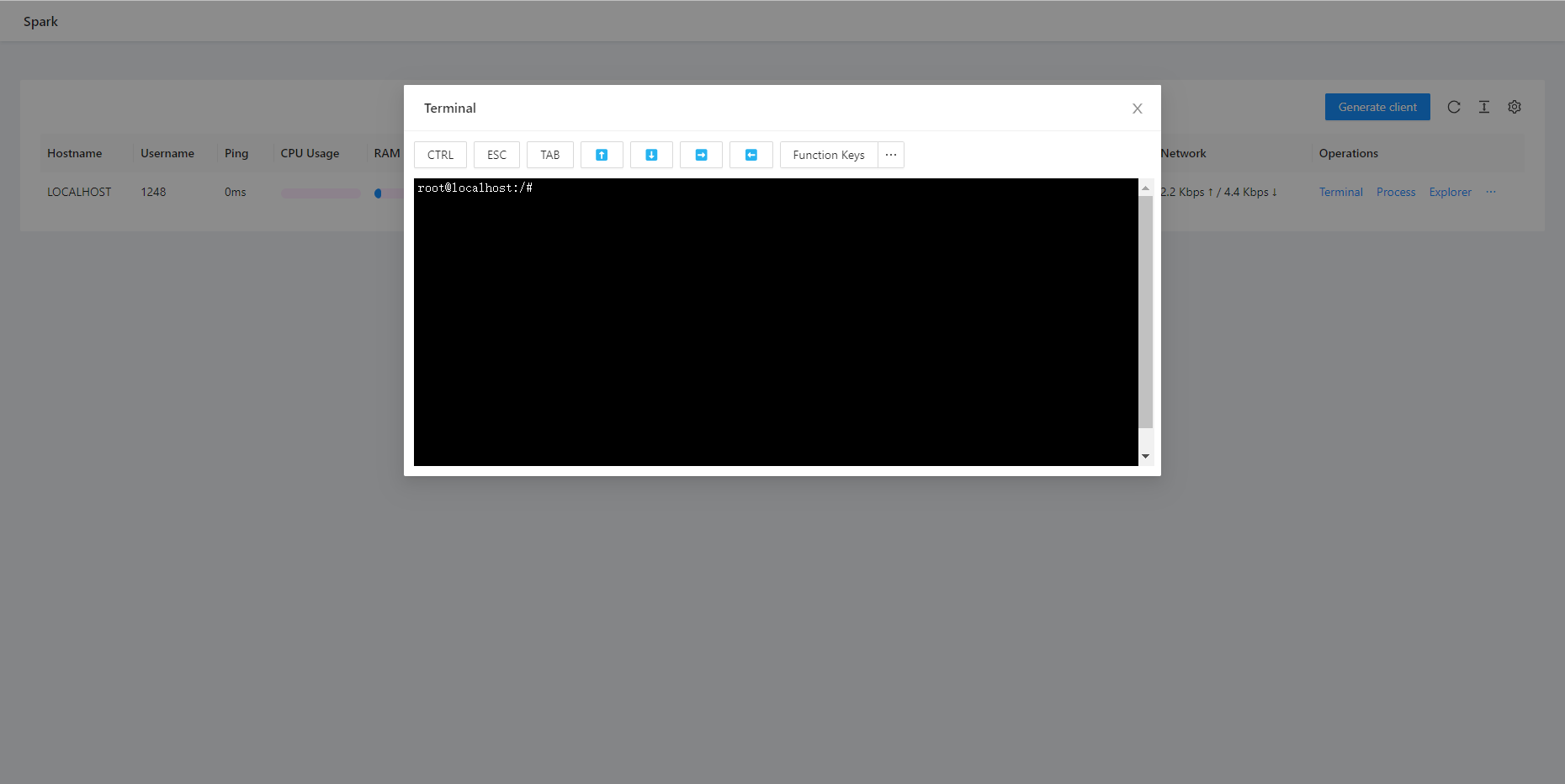
| T1059 | Command and Scripting Interpreter | TA0002 |
|
| T1071.001 | Web Protocols | TA0011 |
|
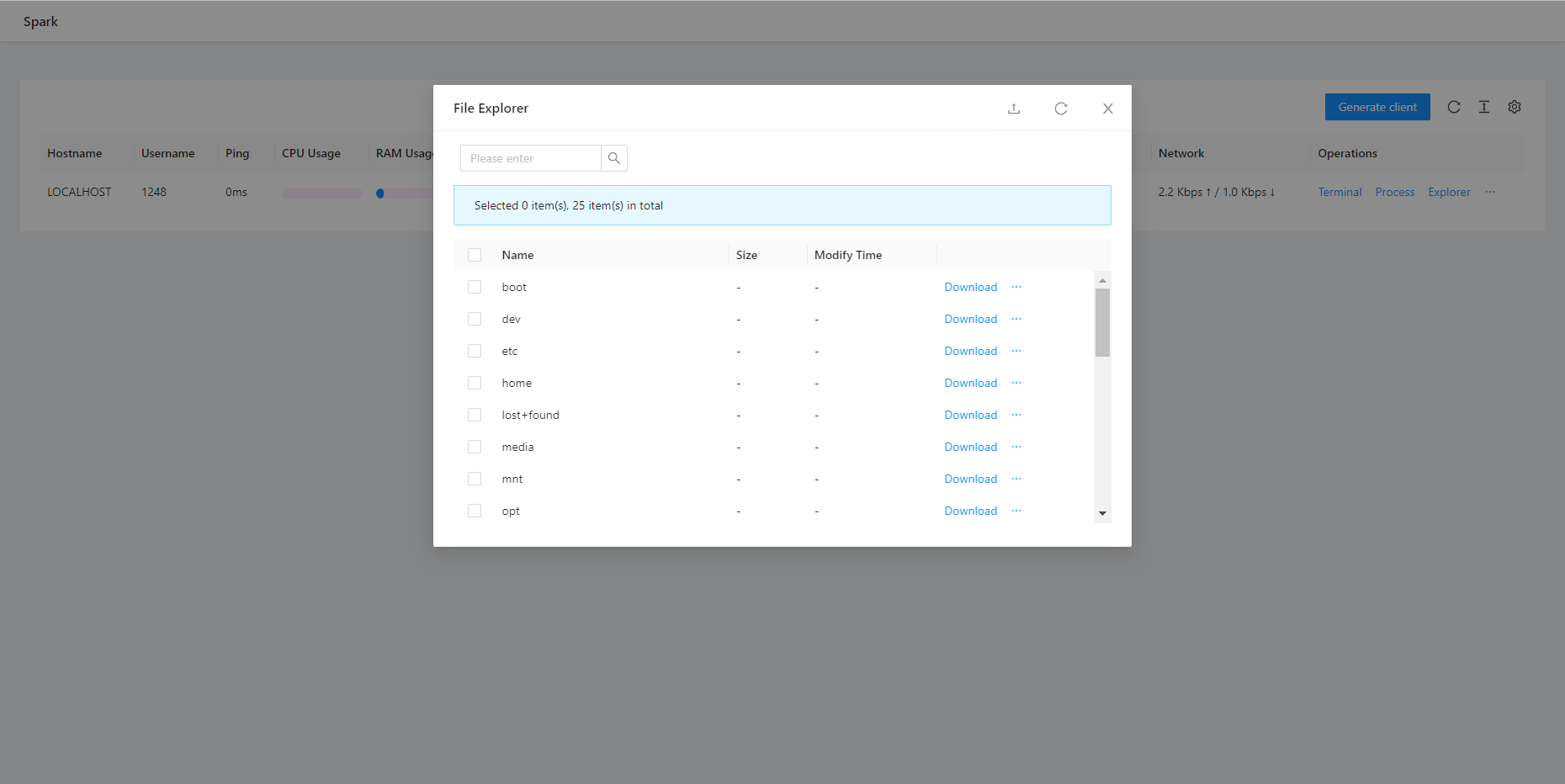
| T1105 | Ingress Tool Transfer | TA0011 |
|
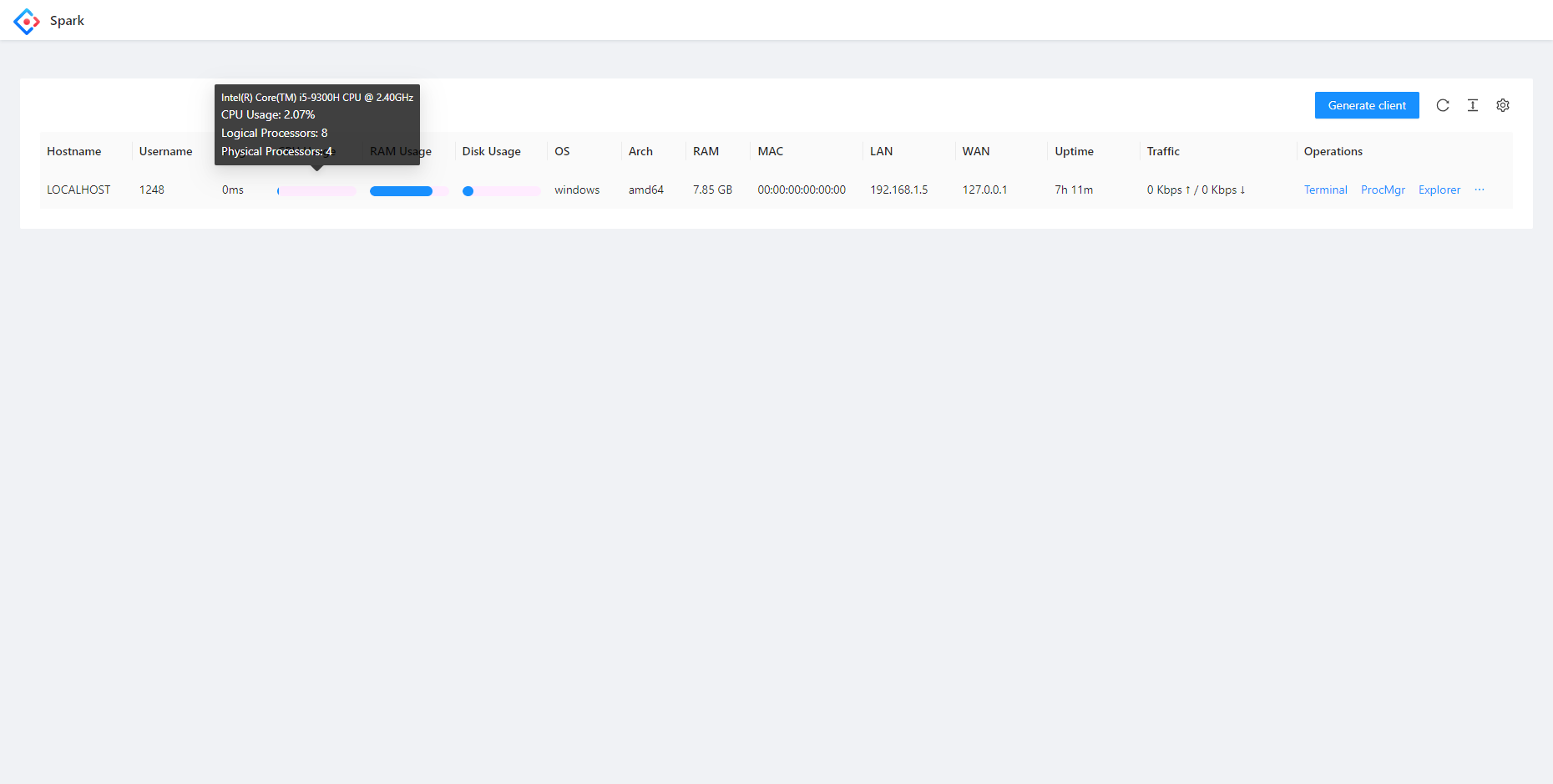
| T1082 | System Information Discovery | TA0007 |
|
| T1083 | File and Directory Discovery | TA0007 |
|
| T1571 | Non-Standard Port | TA0011 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1547 | Boot or Logon Autostart Execution | TA0003 TA0004 |
|
SparkRAT (Open-source, cross-platform RAT)
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Malware / Remote Access Trojan (RAT) — Origin: Unknown (tool used by multiple threat clusters)
Author: iQBlack CTI Team
Executive Summary
SparkRAT is a cross-platform Remote Access Trojan (RAT) written in Go and distributed as an open-source toolset (agent + C2/server). Public reporting consistently frames it as a commodity post-compromise capability rather than a single-actor-exclusive implant, which complicates attribution at the ‘actor’ level and shifts analysis toward campaigns and clusters that deploy it.
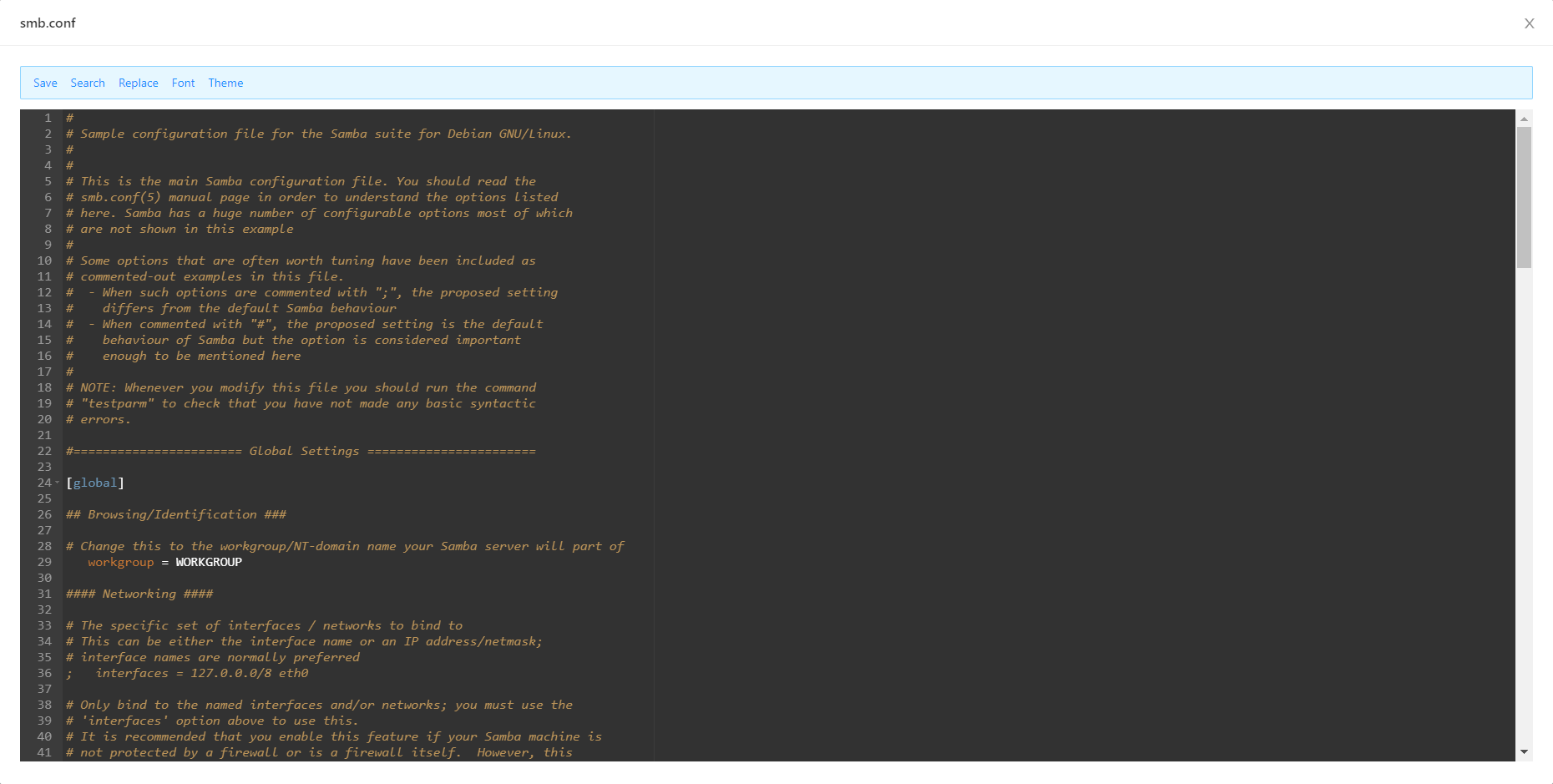
Operationally, SparkRAT functions as an interactive remote administration capability (command execution, file operations, system profiling and other operator-driven actions). As an open-source RAT, its code can be modified, recompiled, and refactored, meaning static indicators (strings, file hashes) are brittle and must be paired with behavior-based hunting.
Public reporting links SparkRAT use to multiple intrusion contexts, including espionage-oriented activity where SparkRAT was loaded by an intermediate Go-based loader (LESLIELOADER) and operated via infrastructure documented in open reporting. Separately, early distribution has been observed via trojanized installers, illustrating that SparkRAT may appear both as a primary payload and as a secondary tool delivered post-access.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
