Threat Actor Characterization

CROCUS RAT
ID: a1532a72862ef57d39753da10c242ef701894Actor Network Graph
Open Network GraphMITRE ATT&CK®
CROCUS RAT is a newly surfaced Windows remote access trojan publicly advertised in March 2026 by the handle shinyenigma. Open sources currently support its existence as a commercially sold crimeware tool with HVNC, keylogging, credential theft, wallet-data theft, and remote PowerShell capabilities, but not yet a mature public campaign record.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1497 | Virtualization/Sandbox Evasion | TA0005 TA0007 |
|
| T1059.001 | PowerShell | TA0002 |
|
| T1056.001 | Keylogging | TA0006 TA0009 |
|
| T1555 | Credentials from Password Stores | TA0006 |
|
| T1539 | Steal Web Session Cookie | TA0006 |
|
| T1005 | Data from Local System | TA0009 |
|
| T1113 | Screen Capture | TA0009 |
|
| T1123 | Audio Capture | TA0009 |
|
| T1204 | User Execution | TA0002 |
|
| T1547 | Boot or Logon Autostart Execution | TA0003 TA0004 |
|
| T1529 | System Shutdown/Reboot | TA0040 |
|
CROCUS RAT — Commercially advertised Windows RAT / HVNC-enabled crimeware
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Malware / Remote Access Trojan (RAT) / Crimeware-for-sale — Origin: Unknown
Author: iQBlack CTI Team
Executive Summary
CROCUS RAT is a newly surfaced Windows remote access trojan publicly advertised in March 2026 by the handle shinyenigma. Publicly available material is limited and currently centers on marketplace-style sales posts rather than incident reporting, malware reverse engineering, or broad victim disclosure.
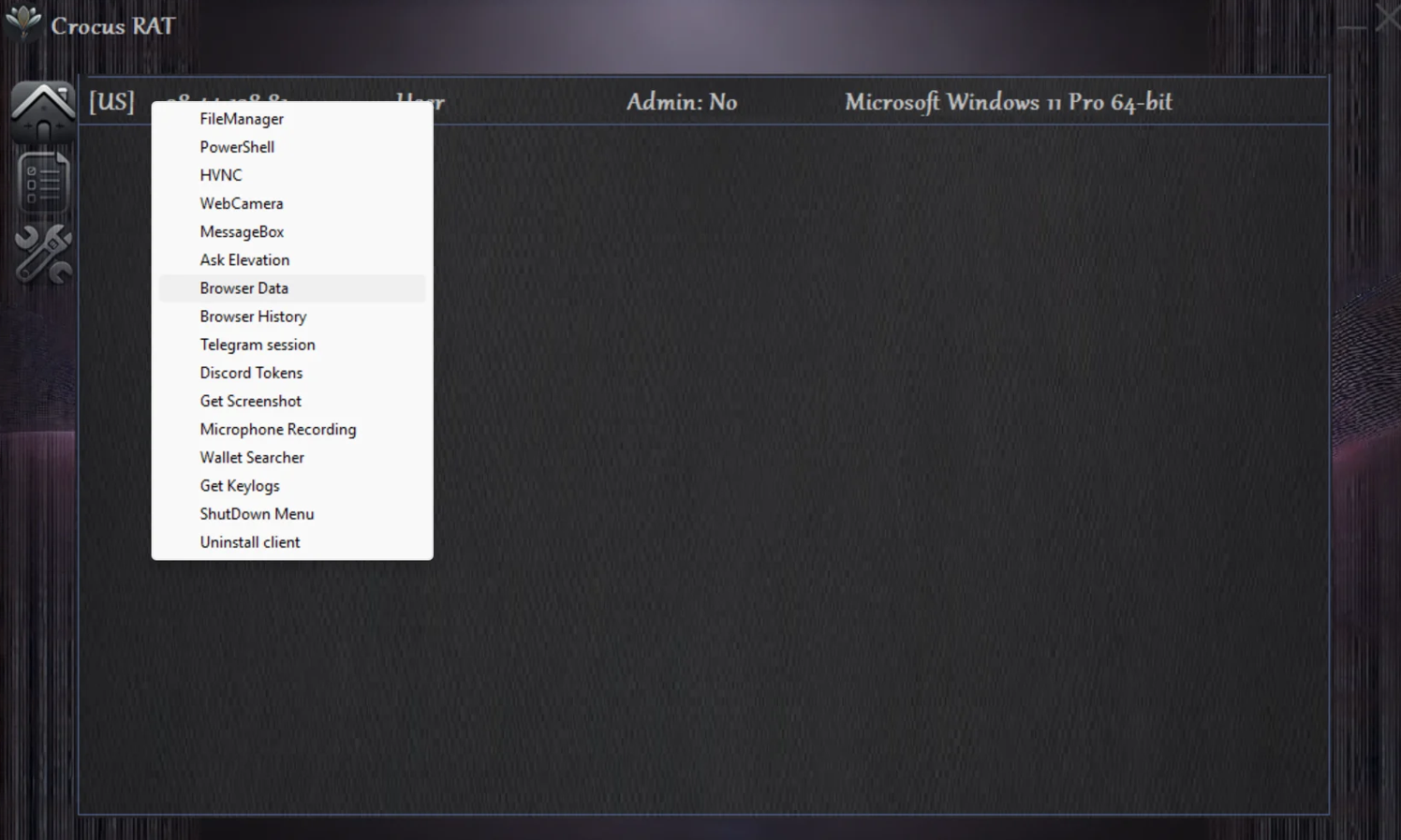
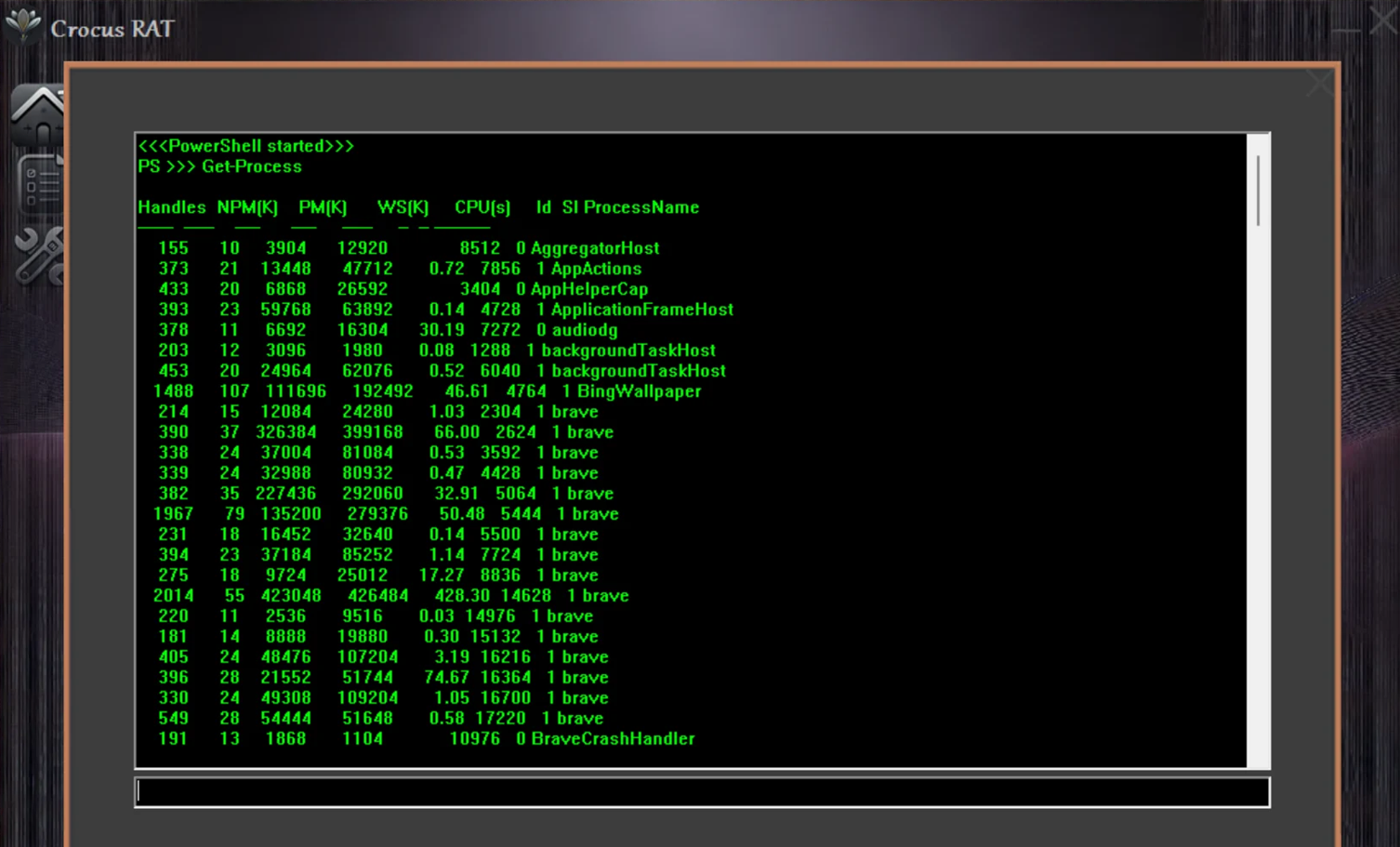
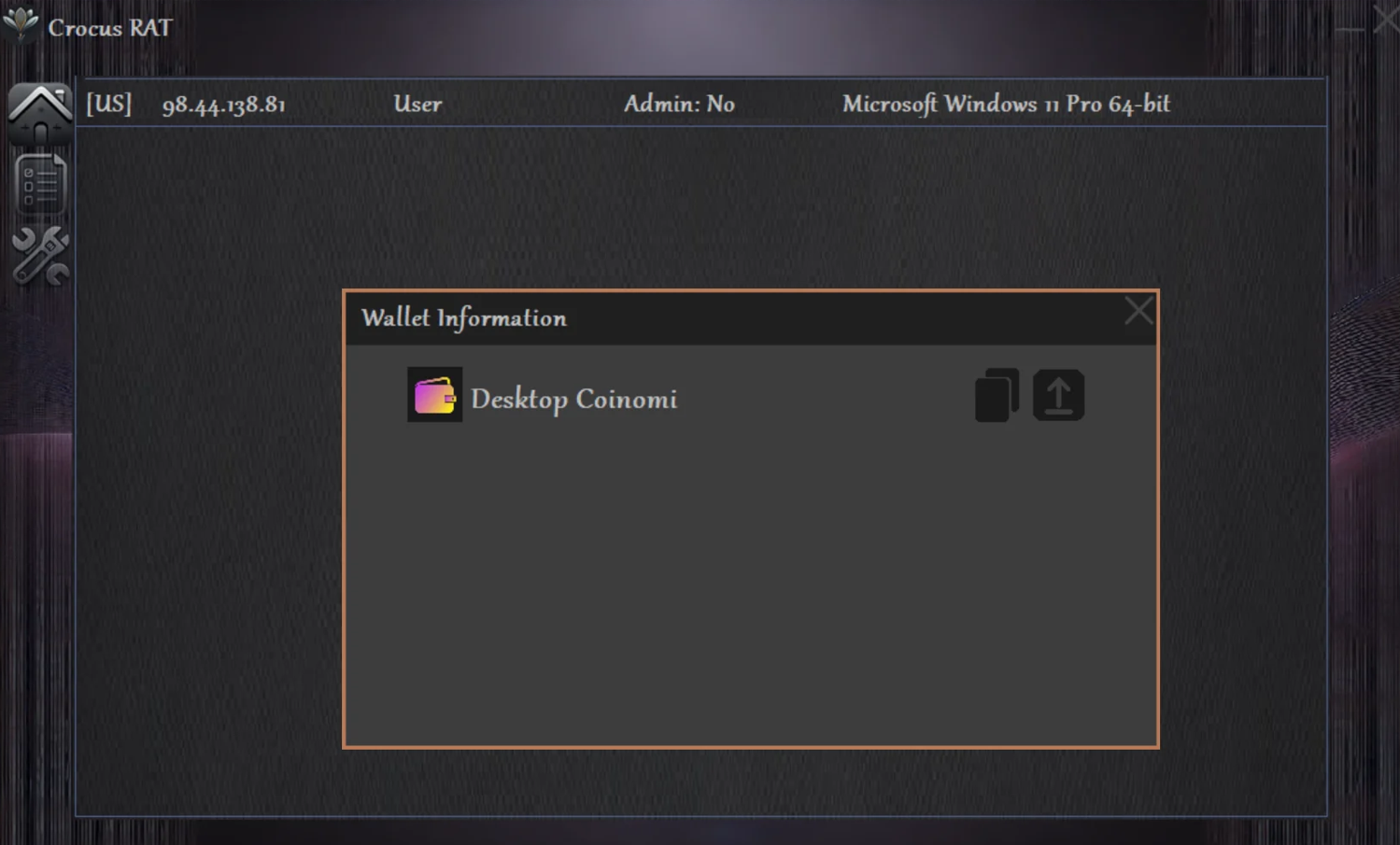
The advertised feature set positions the malware as a multi-function commodity intrusion tool rather than a narrow single-purpose RAT. Claimed capabilities include file management, remote PowerShell execution, HVNC, webcam and microphone access, browser and wallet data recovery, keylogging, Telegram session theft, Discord token theft, privilege elevation, and anti-VM options. That mix is consistent with a general-purpose access-and-theft operator toolkit.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
