Threat Actor Characterization
You’re viewing the read-only version.
Sign in for analyst tools (editors, promote draft, file/relations management, etc.)

BD Anonymous Team
ID: 9f9ab2a2d4c5a8002326eac8fb84a615
Hacktivist Group
Hacktivism
Threat types: Hacktivism, Defacement, Intrusion, DDoS Attack
Progress: 92%
Completeness: 88%
Freshness: 100%
Operation zone: Denmark, Greenland, Israel, Italy, Romania, United Arab Emirates, United Kingdom
Aliases
Limited alias preview
| BangladeshAnonymous | BangladeshAnonymousTeam | BD********** | BD********************* |
| BD*************** | BD********* | BD************* | Th************** |
Showing 2 of 8 aliases in free preview.
Actor Network Graph
Open Network GraphMITRE ATT&CK®
confidence: medium
BD Anonymous is a Bangladesh-associated hacktivist brand active in Telegram-centric campaign ecosystems (e.g., OpIsrael and other themed ops). OSINT links the actor to claimed/reported DDoS/DoS activity and, in ecosystem mappings, to data collection/doxxing themes targeting Israeli entities. Activity is often claim-led and should be validated with telemetry.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1585 | Establish Accounts | TA0042 | |
| T1498 | Network Denial of Service | TA0040 | |
| T1595 | Active Scanning | TA0043 |
|
| T1567.002 | Exfiltration to Cloud Storage | TA0010 |
|
Executive brief
now
Saved successfully.
Hunting Playbook
now
Saved successfully.
IOC Appendix
now
Saved successfully.
OSINT Library
now
Saved successfully.
Showing 1–12 of 15 images
 Free Preview
Free Preview
Alliance with Nation Of Saviors
 Free Preview
Free Preview
Alliance with Tunisian Maskers Cyber Force
 Free Preview
Free Preview
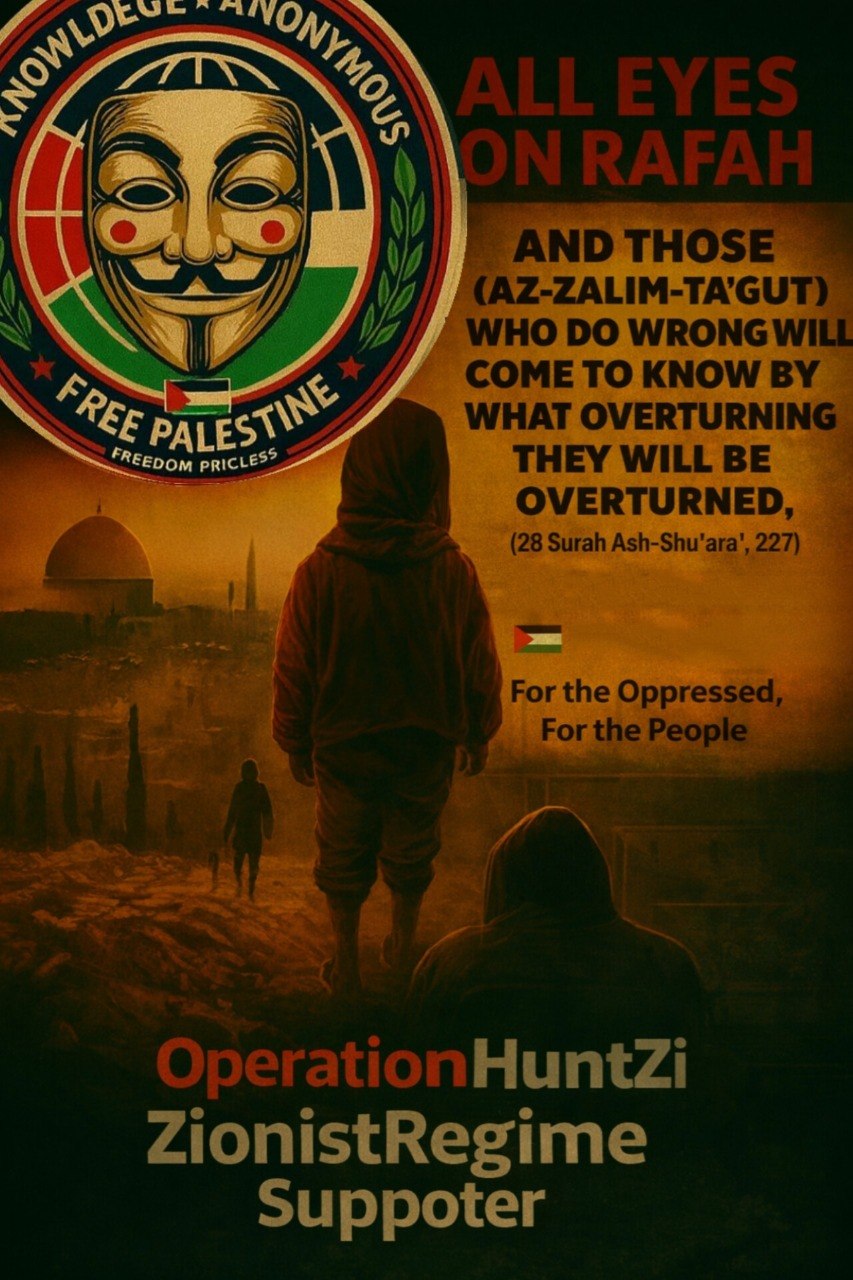
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Alliance with Wolves of Turan
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Alliance with BadakSecTeam
 Free Preview
Free Preview
Propaganda - Logo
Showing 4 of 15 images in preview mode. Additional evidence is restricted for Analyst and Premium plans.
