Threat Actor Characterization

RuskiNet Group
ID: 9cd749301d8b2fcbd1efb402a05cd5d018322| RuskiNet | RuskiNetGroup | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
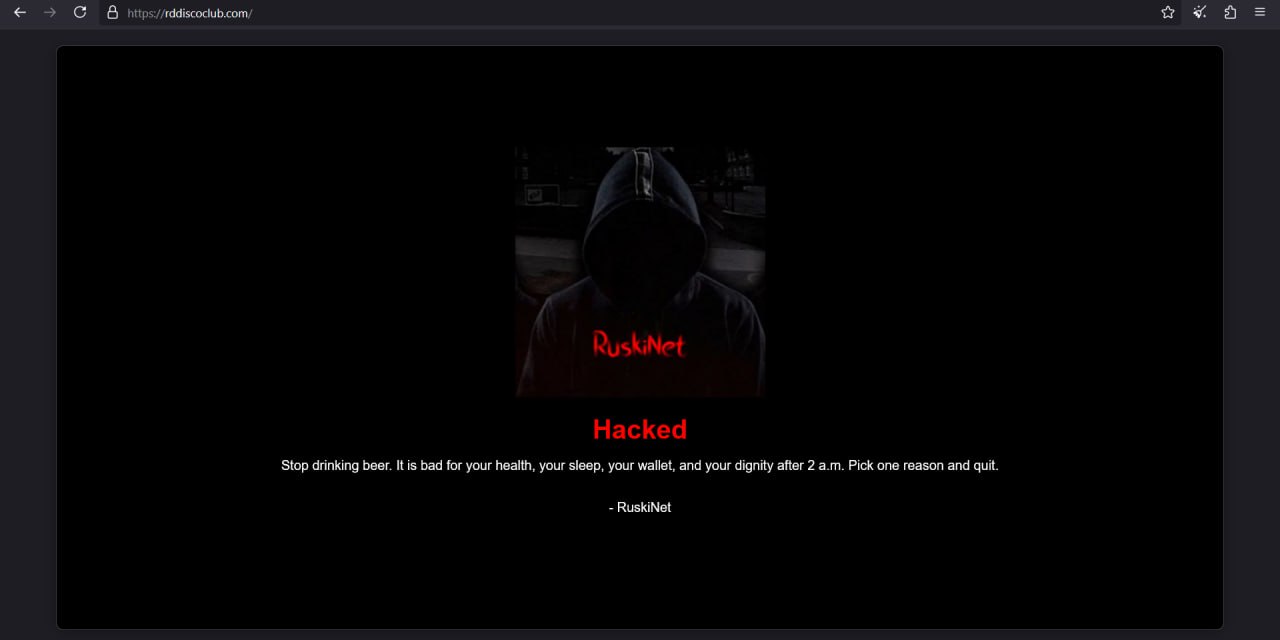
RuskiNet Group is a hacktivist brand first reported in early 2025, linked to pro-Russia-aligned narratives and event-driven campaigns featuring DDoS/defacement claims and opportunistic hack-and-leak messaging via social platforms and forums.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1589 | Gather Victim Identity Information | TA0043 |
|
| T1567 | Exfiltration Over Web Service | TA0010 |
|
| T1654 | Log Enumeration | TA0007 |
|
RuskiNet Group — pro-Russian-aligned hacktivist brand associated with disruptive operations and opportunistic “hack-and-leak” claims
Classification: TLP:WHITE — Open Source Intelligence (OSINT)
Category: Hacktivism / Hybrid cyber influence (DDoS + breach/leak claims) — Origin: INFERENCE (confidence: medium) Eastern Europe / Russia-aligned online milieu
Author: iQBlack CTI Team.
Executive Summary
RuskiNet Group (“RuskiNet”) is an online hacktivist brand first observed in early 2025, linked in vendor reporting to a pro‑Russian / Russia‑aligned information environment and to opportunistic disruption campaigns. Reporting describes a pattern of publicly claimed DDoS activity, website defacements, and “hack‑and‑leak” / breach claims, frequently distributed via social media and underground forums, often around geopolitical flashpoints.
Multiple sources emphasize that many hacktivist breach claims across this ecosystem are difficult to verify and sometimes involve recycled data. Group‑IB assessed RuskiNet as “low reliability” and documented an example where a RuskiNet‑affiliated persona (“YK3”) posted a purported SAP Israel dataset that showed overlap with an older (2023) leak dataset, consistent with data recycling patterns observed in hacktivist leak narratives.
Operationally, RuskiNet should be treated as a volatility amplifier: it can generate short‑notice disruption attempts (commonly DDoS/defacement claims) and reputational pressure through leak narratives, even when technical depth is limited. Defensive focus should prioritize resilience to denial‑of‑service, rapid triage/verification of leak claims, and tight controls on exposed web services and identity.
Hunting Playbook — RuskiNet Group
Purpose: Operational hunting ideas aligned to RuskiNet Group’s assessed hacktivist tradecraft (DDoS/defacement/hack-and-leak-style claims) plus adjacent pro-Russia/pro-ideology hacktivist patterns. Use as a starting point; tune thresholds to your baseline.
IOC Appendix (TLP:WHITE) — RuskiNet Group
This appendix lists OSINT-observed identifiers associated with the RuskiNet brand. Because the actor’s public narrative contains unverifiable claims and potential data recycling, treat these items as pivot points (tracking / collection) rather than confirmed intrusion infrastructure.