Threat Actor Characterization
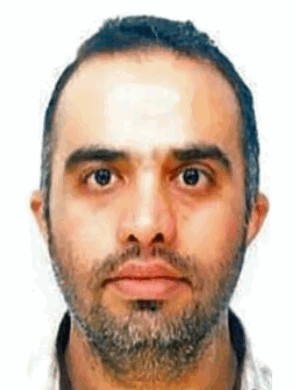
Reza Mohammad Amin Saberian
ID: 8e1b51115cf9f23a27dc1e40755faace18409| Saberian | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Reza Mohammad Amin Saberian is a publicly named senior official of Iran's IRGC-CEC. Public reporting ties him to the command environment behind CyberAv3ngers-linked critical infrastructure activity, but does not provide strong evidence of him as an individually documented hands-on operator.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1078.001 | Default Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
| T1565.001 | Stored Data Manipulation | TA0040 |
|
| T1587.001 | Malware | TA0042 |
|
| T1583.001 | Domains | TA0042 |
|
Reza Mohammad Amin Saberian — IRGC-CEC senior official linked to CyberAv3ngers
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: State cyber official / command-enablement profile - Origin: Iran
Author: iQBlack CTI Team
Executive Summary
Reza Mohammad Amin Saberian is publicly identified by the U.S. Department of the Treasury as a senior official of the Islamic Revolutionary Guard Corps Cyber-Electronic Command (IRGC-CEC). Public U.S. government material does not provide a detailed biography, role title, or individually attributed intrusion history for Saberian. The strongest defensible assessment is therefore institutional rather than personal: he is part of the command structure publicly linked to malicious cyber operations against critical infrastructure through the CyberAv3ngers persona.
The operational significance of Saberian comes from his location inside the IRGC-CEC ecosystem at the time that CyberAv3ngers activity became a major public concern, particularly the compromise of internet-exposed Unitronics PLCs and the broader Iran-linked OT/ICS targeting narrative that followed. Public reporting and later research tie that ecosystem to weak/default credential abuse, public defacement and intimidation, and, in later reporting, the IOCONTROL malware family targeting OT/IoT/Linux-based platforms.
IOC Appendix — Reza Mohammad Amin Saberian
Scope & Caveats. This appendix is intentionally conservative. Publicly available information on Reza Mohammad Amin Saberian is primarily institutional and sanctions-oriented, not sample-rich or personally infrastructure-rich. As a result, most hard indicators below are linked to the IRGC-CEC / CyberAv3ngers operational ecosystem rather than to Saberian as an individually observed operator.
