Threat Actor Characterization
XakNet Team
ID: 851fdc290bdddd300a25d108bd83b22198602| XakNet | XakNet_Team | Xa******** | X***** |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
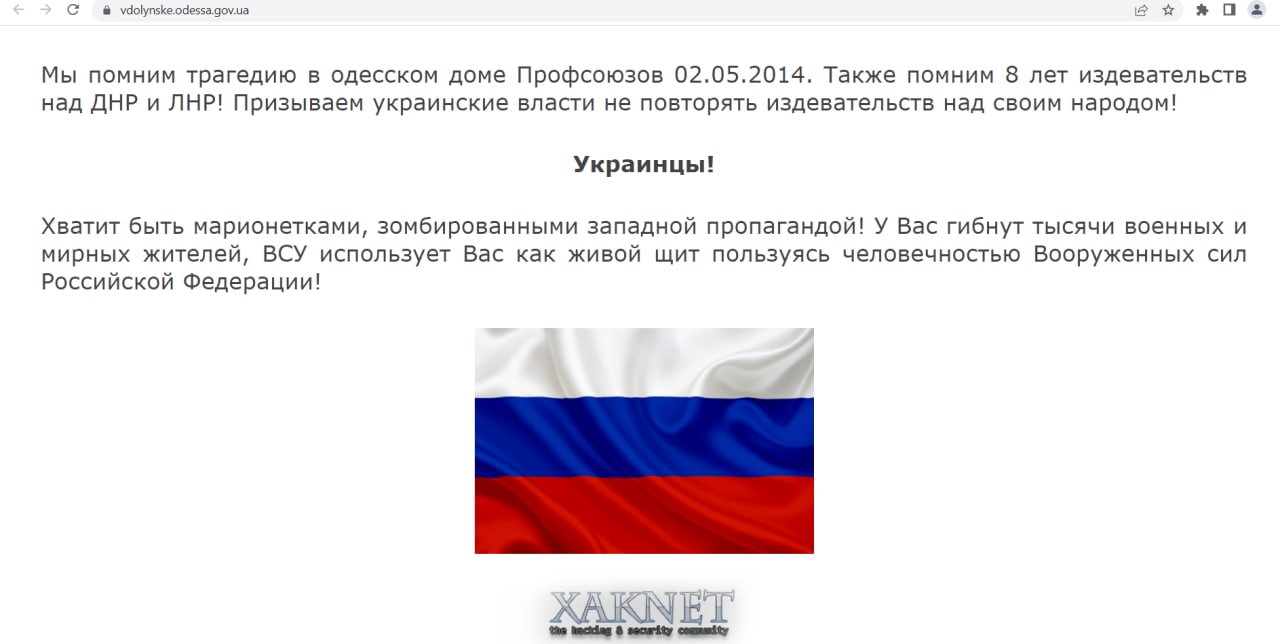
XakNet Team is a pro-Russia hacktivist collective active since March 2022 that conducts hack-and-leak operations and propaganda-driven DDoS claims against Ukraine and pro-Ukraine entities; government and vendor reporting record a late-March-2022 email leak from a Ukrainian official and assess coordination with GRU in selected cases.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1565.002 | Transmitted Data Manipulation | TA0040 |
|
| T1498 | Network Denial of Service | TA0040 |
|
CLASSIFICATION: Unclassified / Open Source
Executive Summary
XakNet Team is a pro-Russia hacktivist collective that surfaced in 2022-03 during the full-scale invasion of Ukraine, conducting hack-and-leak operations and propaganda-heavy DDoS claims against Ukrainian government entities and countries supporting Ukraine. A U.S.-led joint advisory on 2022-05-09 recorded that, in late March 2022, XakNet leaked the email contents of a Ukrainian government official accompanied by a political statement, indicating a hack-and-leak/IO nexus. Independent government and vendor reporting subsequently assessed coordination/affiliation with Russian state interests: Mandiant (2022-09-23) identified evidence connecting XakNet administrators to the GRU through timing and provenance of Ukrainian intrusions and leaks. Overall confidence in these core facts is high based on official advisories and primary vendor analysis.
- Industries/Sectors: Government ministries and agencies; political/foreign affairs; (secondarily) public-facing services and media properties tied to Ukraine or pro-Ukraine coalitions.
- Geography (Region): Primarily Ukraine, with spillover targeting of supporting states (NATO/EU members) through opportunistic DDoS/IO.
- Countries (if available): Ukraine (MFA, senior officials); broader “pro-Ukraine” countries (various claims).
- Timeframe: 2022–2025 (first public activity March–May 2022; continued mentions in government/vendor reporting through 2024–2025).