Threat Actor Characterization
You’re viewing the read-only version.
Sign in for analyst tools (editors, promote draft, file/relations management, etc.)

TEAM BD CYBER NINJA
ID: 7d5f3563d7e07144ed31dd017b11454c
Hacktivist Group
Hacktivism
Threat types: Hacktivism, Black-Hat, Defacement, Data Leak, Propaganda
Progress: 95%
Completeness: 100%
Freshness: 100%
Operation zone: Bangladesh, Brazil, India
Aliases
Limited alias preview
| Bangladesh Black-Hat Cyber Team | TBCN | TB****************************** | Te***************** |
| Te**************** | — | — | — |
Showing 2 of 5 aliases in free preview.
Actor Network Graph
Open Network GraphMITRE ATT&CK®
confidence: medium
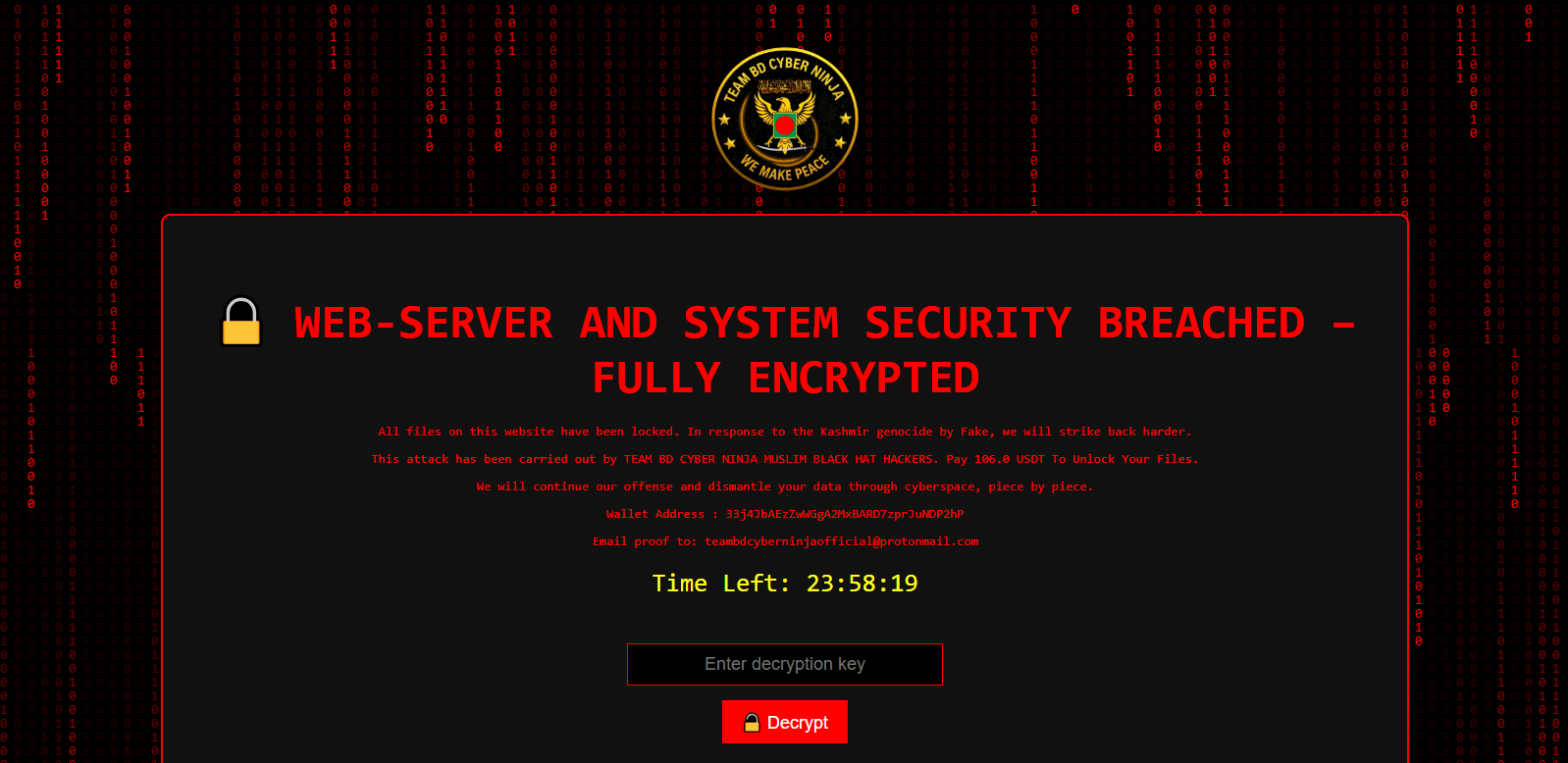
Bangladesh-linked hacktivist collective associated in OSINT with website defacement campaigns and public claims, primarily targeting Bangladesh and India; occasional extortion/ransomware claims exist but are inconsistently corroborated.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1595 | Active Scanning | TA0043 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1110 | Brute Force | TA0006 |
|
| T1491.002 | External Defacement | TA0040 |
|
| T1567.002 | Exfiltration to Cloud Storage | TA0010 |
|
| T1486 | Data Encrypted for Impact | TA0040 |
|
Executive brief
now
Saved successfully.
Hunting Playbook — TEAM BD CYBER NINJA
Priority: High for organizations with public-facing web portals (education, government, local services) in South Asia; Medium elsewhere. This playbook focuses on detecting opportunistic web compromise leading to external defacement and related coercion signals attributed to TEAM BD CYBER NINJA-style activity.
Tip: Hover the section title to learn what’s included in Analyst / Premium plans.
Hunting Playbook
now
Saved successfully.
IOC Appendix
now
Saved successfully.
OSINT Library
now
Saved successfully.