Threat Actor Characterization
You’re viewing the read-only version.
Sign in for analyst tools (editors, promote draft, file/relations management, etc.)

Cyb3r Drag0nz
ID: 741b9c48141d50c355bd01dc51eeeb3582254
Hacktivist Group
DDoS Crew
Hacktivism
Threat types: Hacktivism, Intrusion, Defacement, DDoS Attack, DoS, data Leak, Pro-Hamas, Anti-Israel
Progress: 94%
Completeness: 96%
Freshness: 90%
Operation zone: Israel, Morocco
Aliases
Limited alias preview
| Cyb3r Army | Cyb3r Drag0nz TeaM | Cy************** | Cy**************** |
| Cy*********** | Cy*********** | — | — |
Showing 2 of 6 aliases in free preview.
Actor Network Graph
Open Network GraphMITRE ATT&CK®
confidence: medium
Cyb3r Drag0nz (Cyb3r Drag0nz Team) is a hacktivist brand widely described as pro-Hamas/anti-Israel, associated with DDoS/DoS disruption, website defacement, and data leak claims. In early 2026 escalation reporting, it is described as reactivated/emerging and claiming coalition alignment with an 'Islamic Resistance Axis' operations room. Activity is claim-led and should be validated by telemetry.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1585 | Establish Accounts | TA0042 |
|
| T1498 | Network Denial of Service | TA0040 |
|
| T1491.002 | External Defacement | TA0040 | |
| T1567.002 | Exfiltration to Cloud Storage | TA0010 |
|
| T1595 | Active Scanning | TA0043 |
|
Executive brief
now
Saved successfully.
Hunting Playbook — Cyb3r Drag0nz
Goal: detect DDoS/DoS and defacement activity, quantify real impact vs claim noise, and catch opportunistic compromise attempts that may occur during disruption windows.
Tip: Hover the section title to learn what’s included in Analyst / Premium plans.
Hunting Playbook
now
Saved successfully.
IOC Appendix
now
Saved successfully.
OSINT Library
now
Saved successfully.
Showing 1–5 of 5 images
 Free Preview
Free Preview
Reference image
 Free Preview
Free Preview
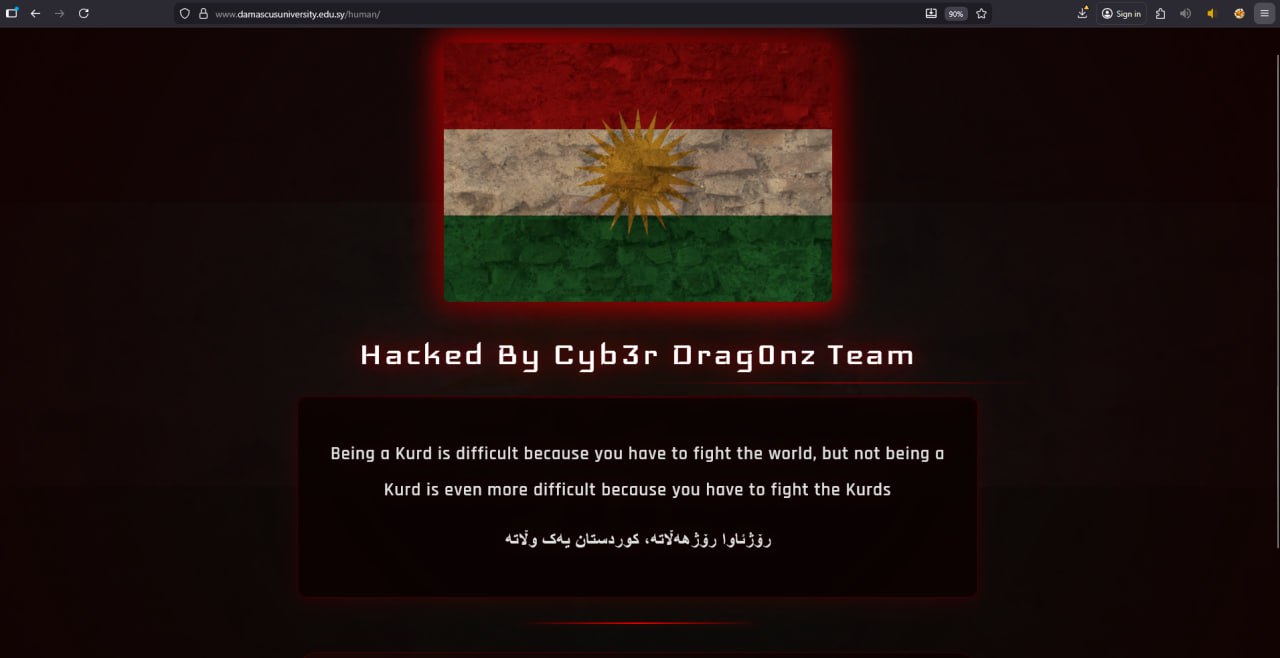
Hacked website
 Free Preview
Free Preview
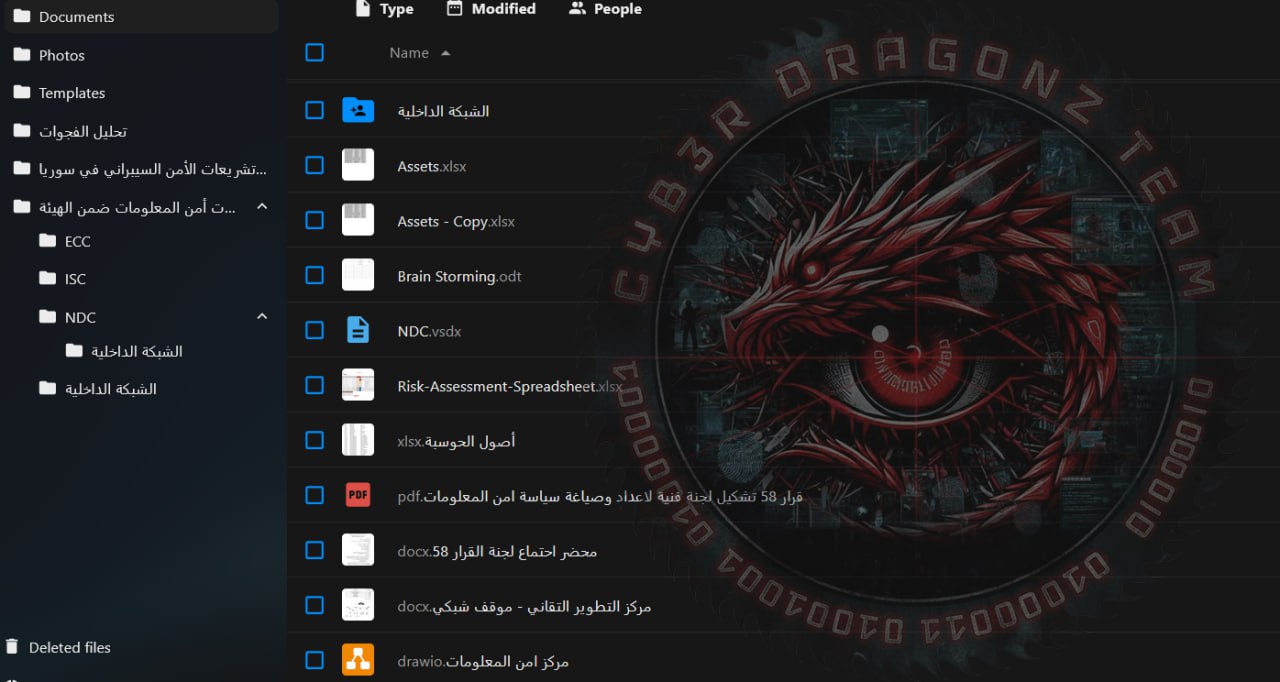
Intrusion / Propaganda
 Free Preview
Free Preview
Hacked website
 Free Preview
Free Preview
Propaganda
Showing 4 of 5 images in preview mode. Additional evidence is restricted for Analyst and Premium plans.
