Threat Actor Characterization

V For Vendetta Cyber Team
ID: 73c8b02d2786934ce41c756164d6863d66403| Project_Vendetta | VENDETTA CYBER TEAM | VF***** | V**** |
| VF******** | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
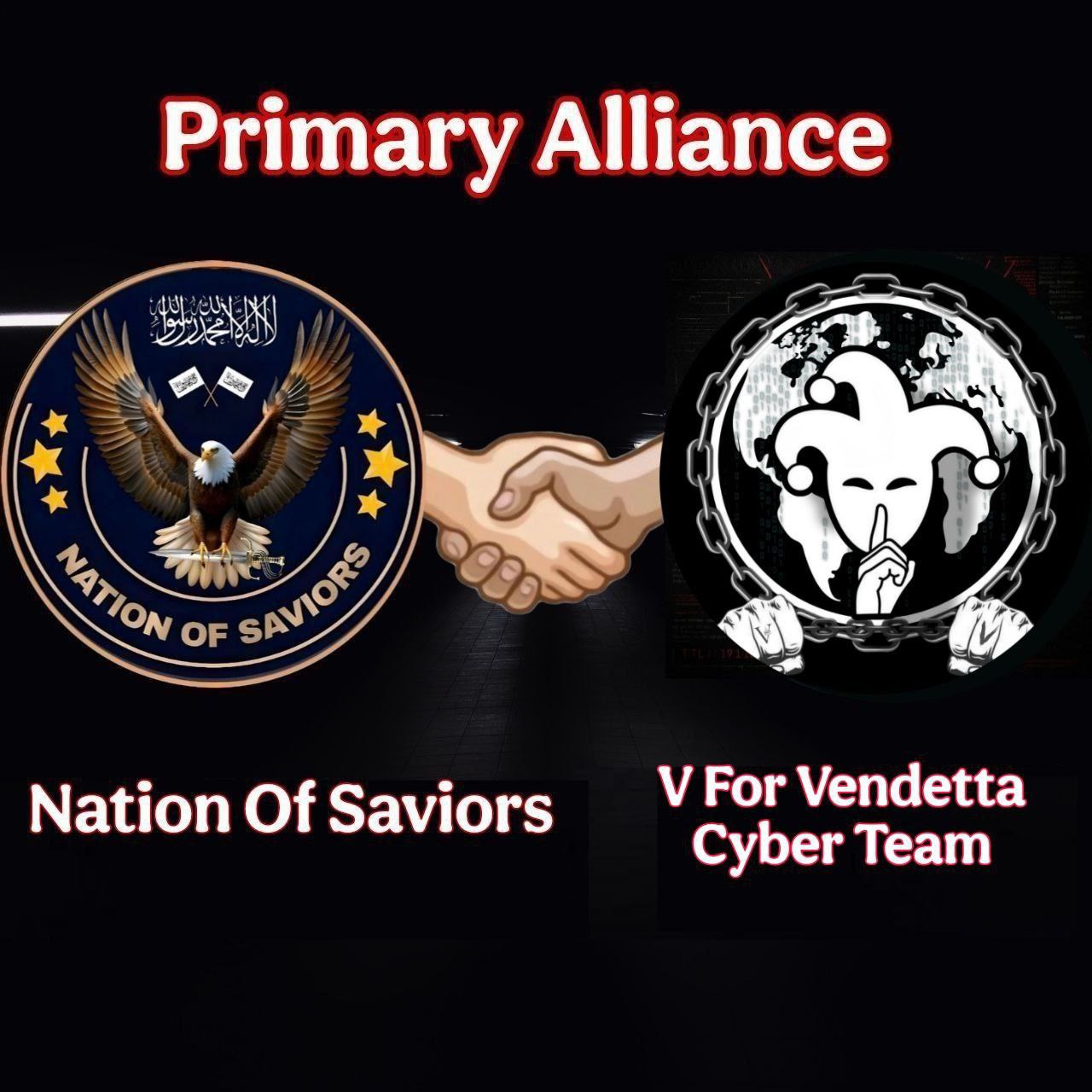
V For Vendetta Cyber Team (VFVCT) is an Anonymous-themed hacktivist / hybrid actor that conducts web application compromises, defacements, and database leaks against government and organizational websites, with campaigns framed around political and social causes (e.g., environmental protests in Indonesia, pro-Palestinian messaging). Recent OSINT also lists VFVCT as an emerging ransomware group, suggesting possible overlap between hacktivism and profit-motivated extortion, though detailed crypto-ransomware TTPs are not yet publicly documented.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1491.002 | External Defacement | TA0040 |
|
| T1213 | Data from Information Repositories | TA0009 |
|
| T1585.001 | Social Media Accounts | TA0042 |
|
| T1585.003 | Cloud Accounts | TA0042 |
|
| T1587.001 | Malware | TA0042 |
|
| T1486 | Data Encrypted for Impact | TA0040 |
|
V For Vendetta Cyber Team (VFVCT)
Classification: TLP:WHITE — Hacktivist / Multi-cause
Status: Active (at least 2025–present)
Author: iQBlack Team
Executive Summary
V For Vendetta Cyber Team (VFVCT), also branded as VFVCT Team or Vendetta Cyber Team, is an emerging, Anonymous-styled hacktivist collective claiming operations against government and organizational websites worldwide. Publicly observed activity as of 2025 is dominated by website defacements and database breaches with data leaks, framed as protests against corruption, environmental harm and geopolitical causes such as “Free Palestine”.
A notable 2025 incident includes the breach of the North Sulawesi Provincial Government (Indonesia) legal documentation portal (jdih.sulutprov.go.id), where VFVCT allegedly exfiltrated and leaked a database (~4MB) containing admin credentials and government records, citing environmental plans in Raja Ampat as motivation. Public defacement pages and a dedicated blog present VFVCT as “digital revolutionaries” and a “resistance” against perceived injustice, explicitly aligned with the V for Vendetta / Anonymous visual and narrative style.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
