Threat Actor Characterization
You’re viewing the read-only version.
Sign in for analyst tools (editors, promote draft, file/relations management, etc.)
Anonymous Russia
ID: 71baa6e296e685bb269cd958f3fd86a599046
Hacktivist Group
Hacktivism
Threat types: DDoS, Operational Disruption, Propaganda
Progress: 63%
Completeness: 51%
Freshness: 90%
Operation zone: —
Aliases
Limited alias preview
No aliases registered.
Actor Network Graph
Open Network GraphMITRE ATT&CK®
confidence: medium
Anonymous Russia — pro-Russia hacktivist label coordinating Telegram-driven DDoS campaigns and public call-outs; impact mostly short-lived outages and narrative pressure.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 |
|
| T1585 | Establish Accounts | TA0042 |
|
| T1102 | Web Service | TA0011 |
|
| T1589 | Gather Victim Identity Information | TA0043 |
|
Anonymous Russia — Pro-Russia Hacktivist Label (DDoS / Campaign Signaling)
CLASSIFICATION: Unclassified / Open Source
Executive Summary
Anonymous Russia is a pro-Russia hacktivist brand that coordinates DDoS campaigns and threat signaling via Telegram, often in concert with other labels (e.g., KillNet, NoName057(16)). OSINT shows event-driven operations (e.g., ad-hoc campaigns against Azerbaijan in August 2022) and coalition dynamics typical of the post-2022 ecosystem. Claims sometimes exceed demonstrable technical depth; impact is primarily short-lived availability disruption and attention capture. Confidence: medium (vendor analyses and incident reporting).
- Identity & posture. Pro-Kremlin messaging; Telegram-centric recruitment/tasking; no verified state C2, though ecosystem overlaps with prominent pro-Russia banners. INFERENCE (medium) synthesized across sources. secalliance.com
- Leadership volatility. Open reporting noted arrests/infighting in 2023 in the KillNet orbit affecting Anonymous Russia branding and cohesion. Flashpoint
- Objectives. Punitive/retaliatory DDoS keyed to political triggers (e.g., national incidents, sanctions, war milestones), plus perception shaping through public “victim lists.”
- Influence model. Public call-outs → claimed outages → amplification via allied channels and media. INFERENCE (medium).
Executive brief
now
Saved successfully.
Hunting Playbook
now
Saved successfully.
IOC Appendix
now
Saved successfully.
OSINT Library
now
Saved successfully.
Showing 1–5 of 5 images
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Logo variant
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
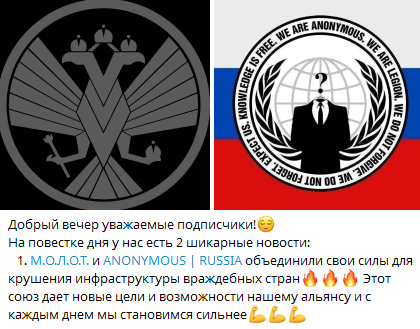
Affiliation with another group
 Free Preview
Free Preview
Affiliation with another group
Showing 4 of 5 images in preview mode. Additional evidence is restricted for Analyst and Premium plans.
