Threat Actor Characterization
You’re viewing the read-only version.
Sign in for analyst tools (editors, promote draft, file/relations management, etc.)

CGPLLNET NETWORK
ID: 6c51ba61ddb47af6cced9cc005e4ebea78708
Hacktivist Group
Hacktivism
Threat types: Hacktivism, Intrusion
Progress: 94%
Completeness: 92%
Freshness: 100%
Operation zone: Finland, Ukraine
Aliases
Limited alias preview
| CGPLLNET | CGPLLNET Legion | CG************** | CG*********** |
| Cy*********************************************** | Гл***************************************** | От************ | — |
Showing 2 of 7 aliases in free preview.
Actor Network Graph
Open Network GraphMITRE ATT&CK®
confidence: medium
CGPLLNET NETWORK is an OSINT-described Telegram-centric hacktivist/cybercrime-adjacent collective referenced in public reporting around the 2024 #FreeDurov/#OpDurov campaign. The primary observed activity is coordinated DDoS targeting and claim amplification via Telegram. Infrastructure is likely high-churn; defenders should prioritize surge resilience and telemetry-first claim validation over static blocklists.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 |
|
| T1585.001 | Social Media Accounts | TA0042 |
|
| T1585.002 | Email Accounts | TA0042 |
|
Executive brief
now
Saved successfully.
Hunting Playbook
now
Saved successfully.
IOC Appendix
now
Saved successfully.
OSINT Library
now
Saved successfully.
Showing 1–6 of 6 images
 Free Preview
Free Preview
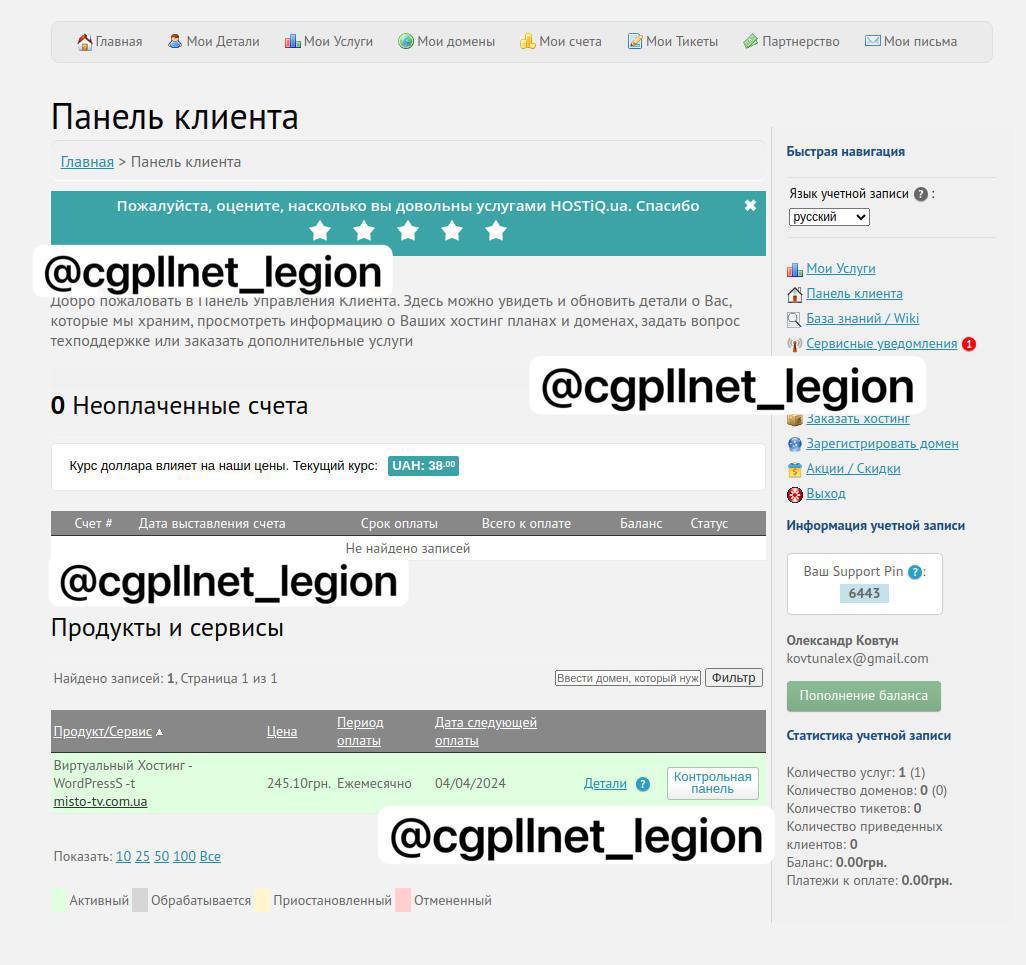
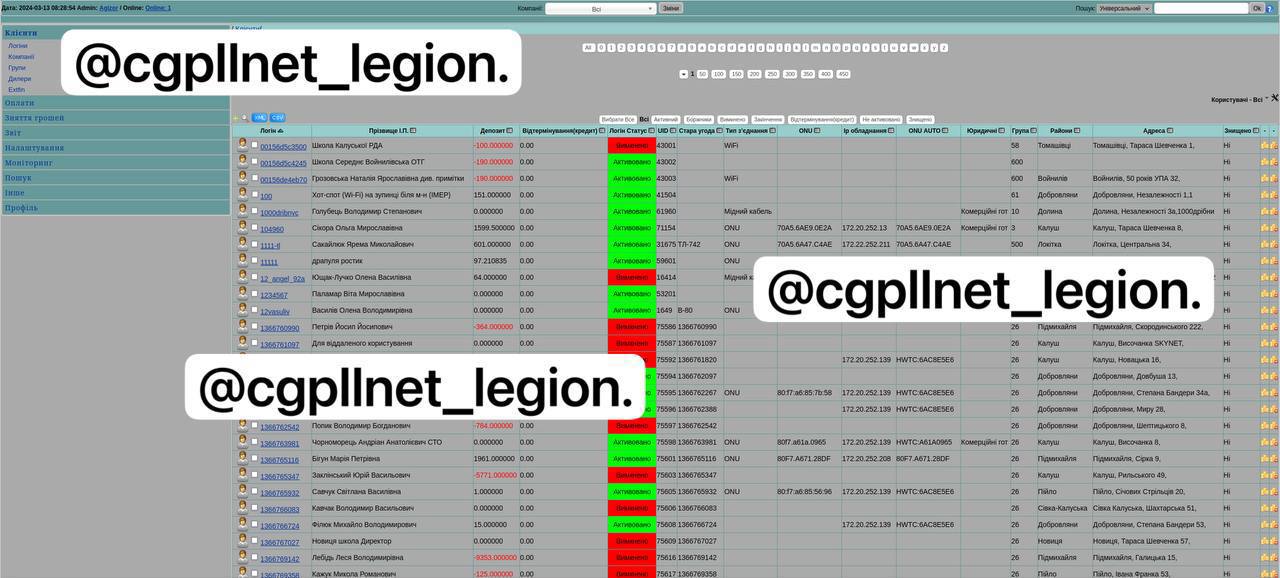
Hacked resource
 Free Preview
Free Preview
Hacked resource
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Propaganda
 Free Preview
Free Preview
Logo
Showing 4 of 6 images in preview mode. Additional evidence is restricted for Analyst and Premium plans.
