Threat Actor Characterization

Keymous Team
ID: 5bdc43b396660424f321fa796614a9f726437| Keymous | Keymous Plus | KE******* | Ke********* |
| K** | KM******* | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Hacktivist/hybrid DDoS-focused collective assessed to originate in North Africa (primarily Algeria) and active since late 2023; notable for high-visibility DDoS claims, alliance signaling, and suspected linkage to DDoS-for-hire (EliteStress).
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1498 | Network Denial of Service | TA0040 | |
| T1583 | Acquire Infrastructure | TA0042 |
|
| T1071 | Application Layer Protocol | TA0011 |
|
| T1588 | Obtain Capabilities | TA0042 | |
| T1650 | Acquire Access | TA0042 |
|
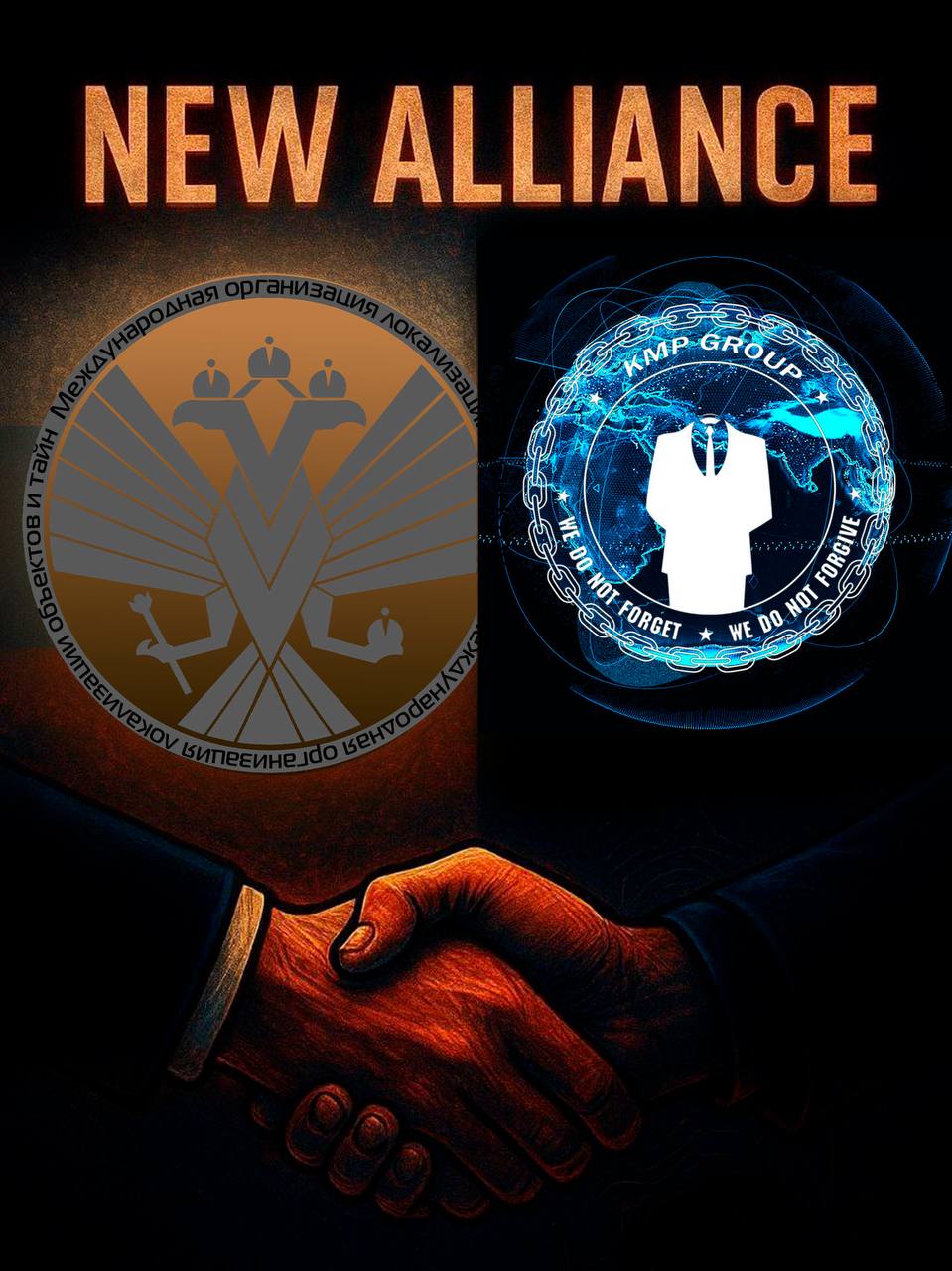
Keymous Team (Keymous+, KMP Group, KEYMOUSE+)
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Hacktivism / Hybrid DDoS Operations (with suspected DDoS-as-a-Service monetization)
Author: iQBlack CTI Team
Executive Summary
Keymous+ (also referenced as KMP Group / Keymous Plus / KEYMOUSE+) is a high-visibility hacktivist-aligned collective that emerged in late 2023, with early public activity linked to DDoS claims against a Moroccan e‑Visa portal (November 2023).
Across 2024–2025, the group scaled into a sustained, opportunistic disruption campaign footprint spanning Europe, North Africa, the Middle East, and parts of Asia, primarily via high-volume DDoS operations and public ‘claim’ messaging on Telegram/X.
Multiple vendors assess the actor as ‘hybrid’—mixing political narratives (e.g., pan‑Arab solidarity / ‘Hack for Humanity’) with signs of commercialization, including promotion or close affiliation with a stressor / DDoS‑for‑hire service branded as EliteStress.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
