Threat Actor Characterization

Ukrainian Cyber Alliance
ID: 59ac0d103560fd5e71607c1e90776709| Alianza Cibernética Ucraniana | UCA | Uk******************** | У** |
| Ук********************* | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1499 | Endpoint Denial of Service | TA0040 |
|
| T1041 | Exfiltration Over C2 Channel | TA0010 |
|
| T1485 | Data Destruction | TA0040 |
|
CLASSIFICATION: Unclassified / Open Source Intelligence (OSINT)
Category: Cyber / Hacktivism — Origin: Ukraine (formed 2016; activity surged 2022–present)
Executive Summary
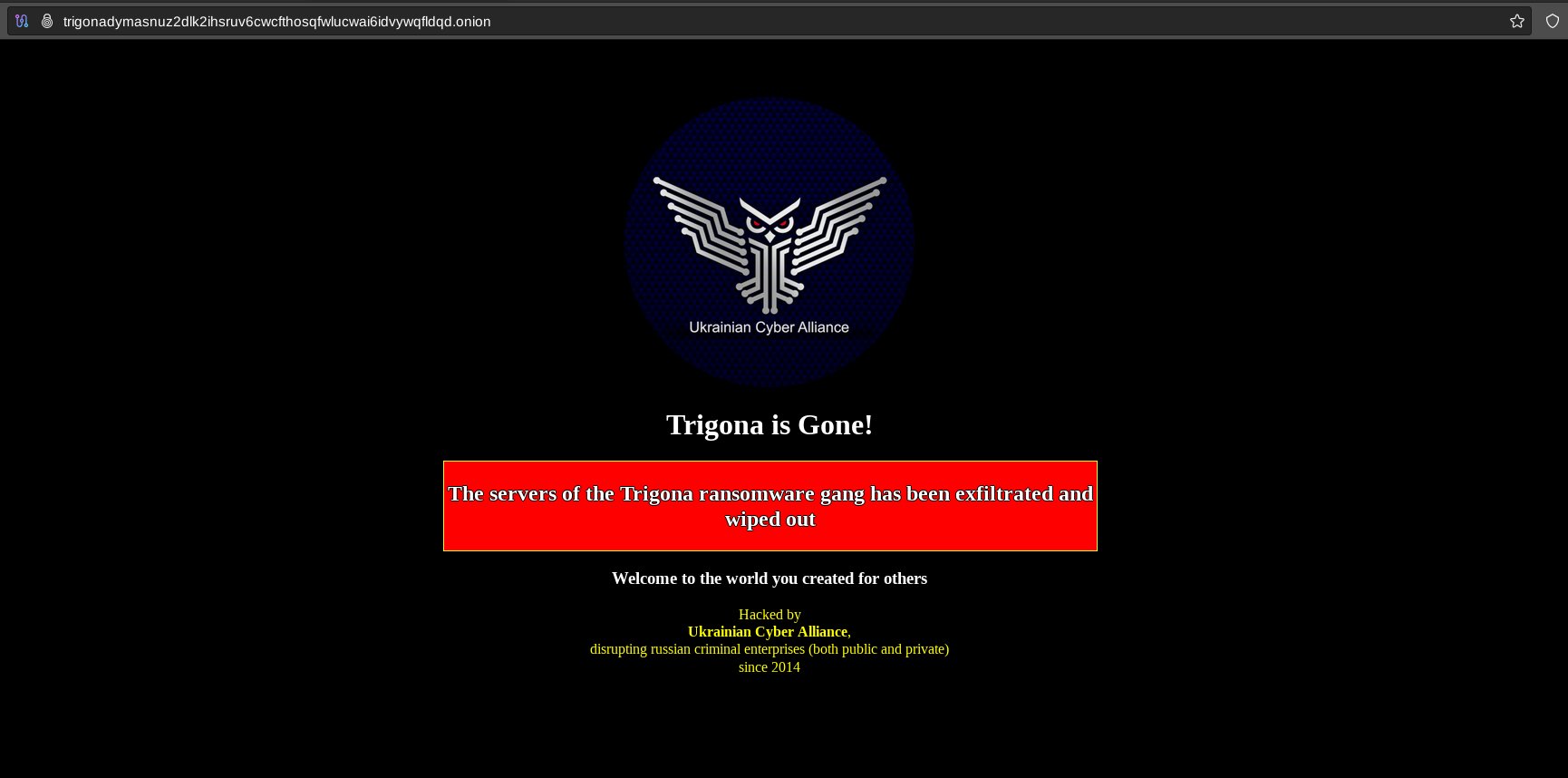
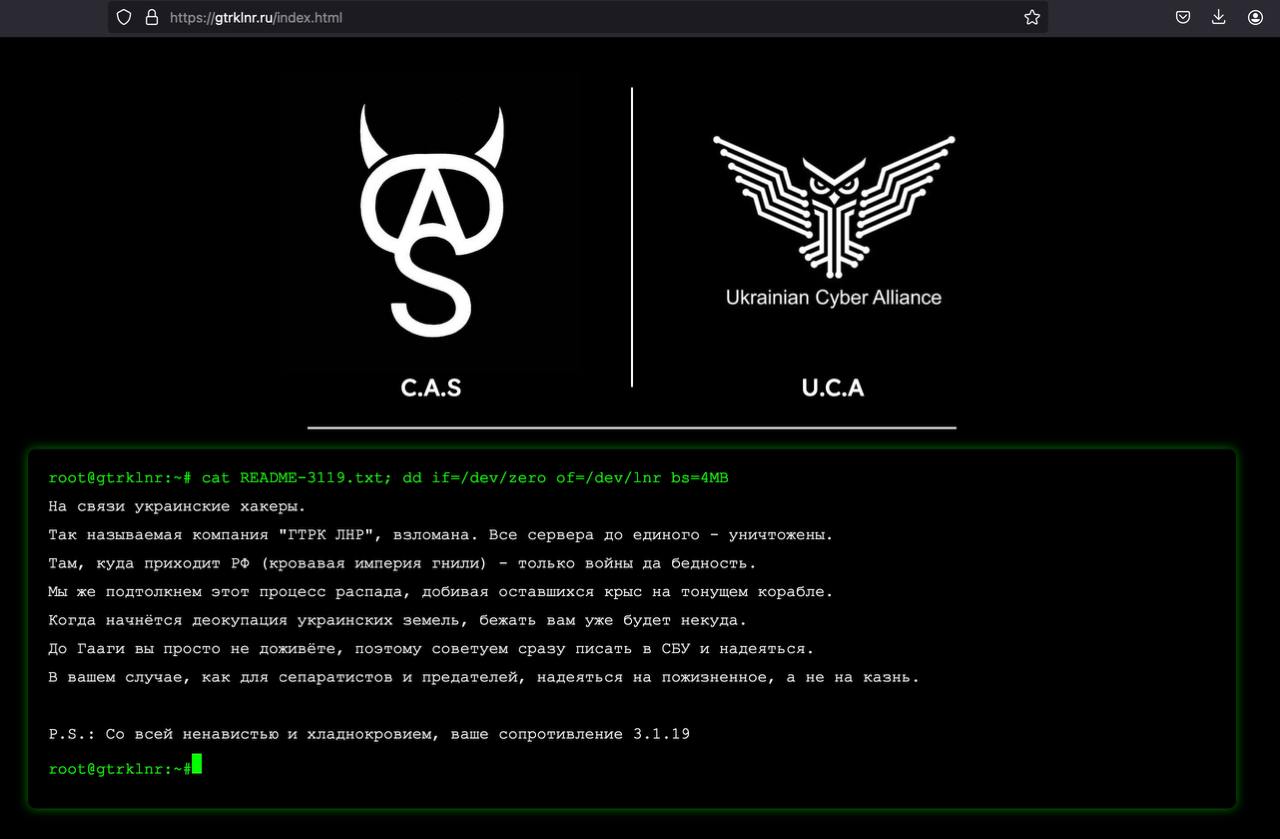
The Ukrainian Cyber Alliance (UCA) is a volunteer, patriotic-aligned hacktivist coalition formed in 2016 through the merger of smaller Ukrainian groups (FalconsFlame, Trinity, RUH8, CyberHunta). UCA conducts offensive cyber-operations—web defacements, data exfiltration/leaks, and destructive intrusions—primarily against Russian state, military, and commercial targets, and occasionally Belarusian entities. The group publicly claims many operations via Telegram and allied channels; some of its campaigns have been corroborated by victim statements and vendor reporting. Since 2022 the UCA has operated inside a broader Ukrainian volunteer ecosystem (including the loosely coordinated “IT Army”) that increased both operational tempo and public visibility for pro-Ukraine hacktivism. UCA accepts cryptocurrency donations and has been linked in open reporting to at least six-figure crypto flows traced in early 2022. Analytical confidence on historical formation, public claims and key incidents is high; confidence on internal governance and precise command relationships inside the volunteer ecosystem is medium.
- Industries / Sectors: Government ministries/agencies; telecommunications and Internet providers; state media; defense-industrial firms; finance/payment rails; local/regional administrations inside Russia/occupied territories.
- Geography (Region): Primary: Russia and Russian-controlled/occupied territories; secondary: Belarus, Russian-service providers with regional ties.
- Timeframe: 2016 (formation) – present, with marked surge in offensive operations and public claims from 2022-02 onward.
Executive Analyst Brief for CISO
Who / What: Ukrainian Cyber Alliance (UCA) — volunteer pro-Ukraine hacktivist coalition (2016→) that publicly claims data theft, destruction and defacement operations primarily against Russian targets; active surge since 2022.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
