Threat Actor Characterization

Z-Pentest Alliance
ID: 4324563b5322b38d31833a74c88177ab| Alianza Z-Pentest | The Western Front | Th******************** | Z-******** |
| З-**************** | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
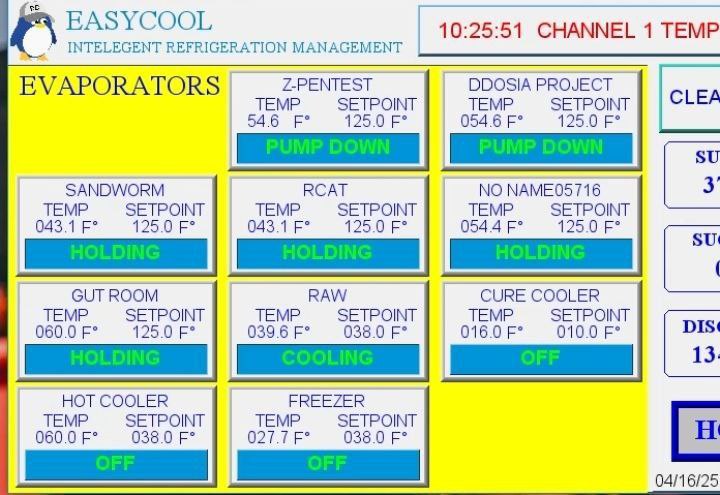
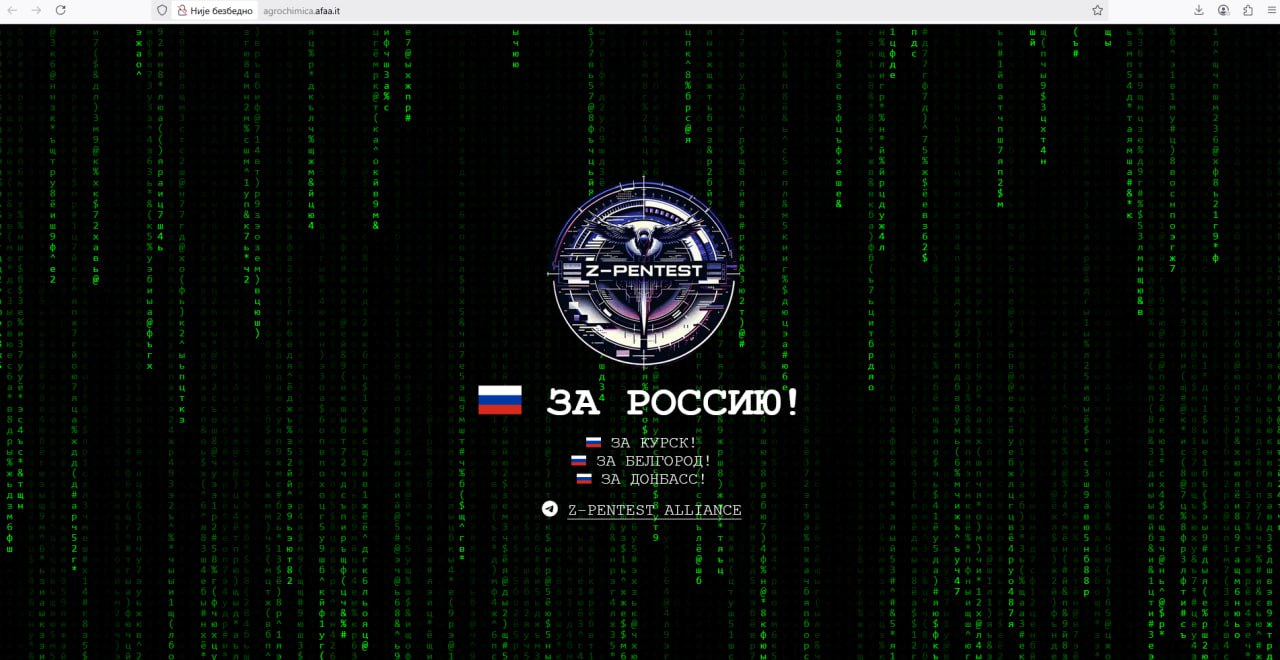
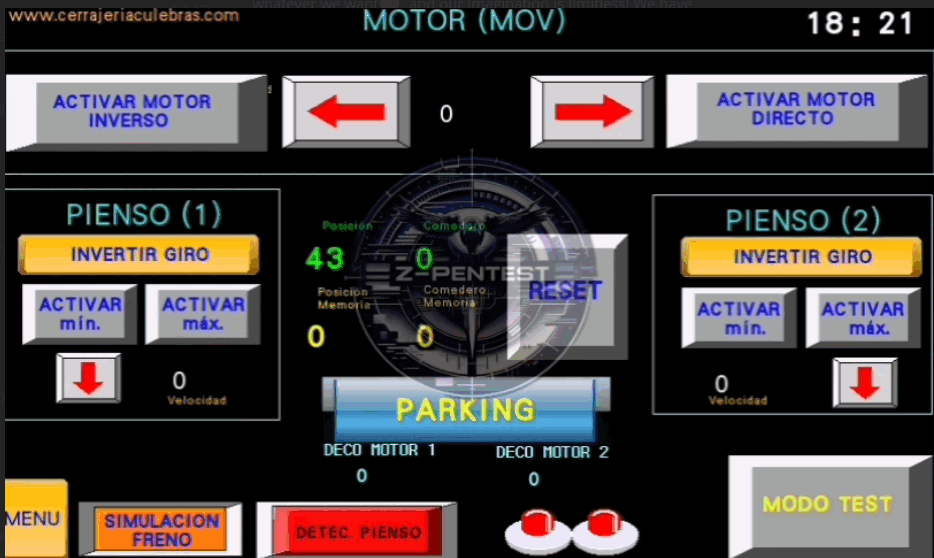
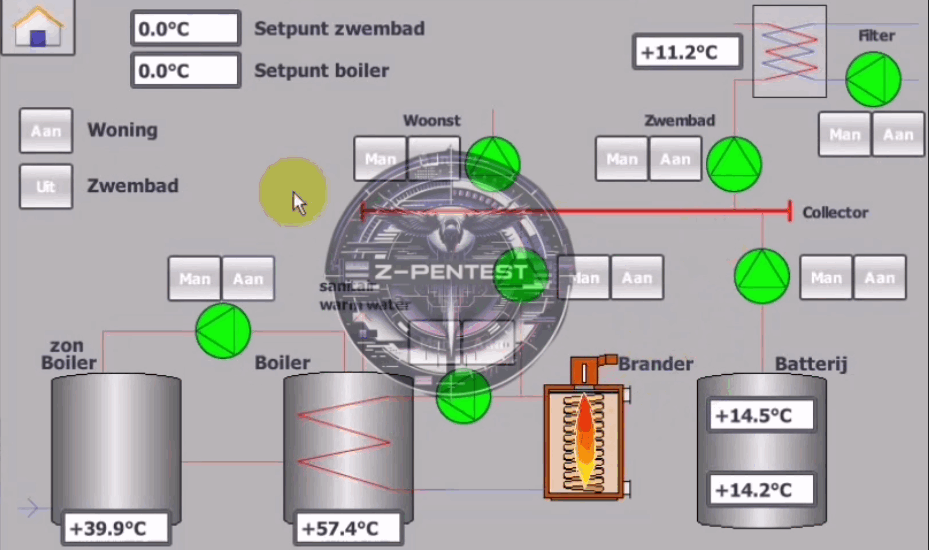
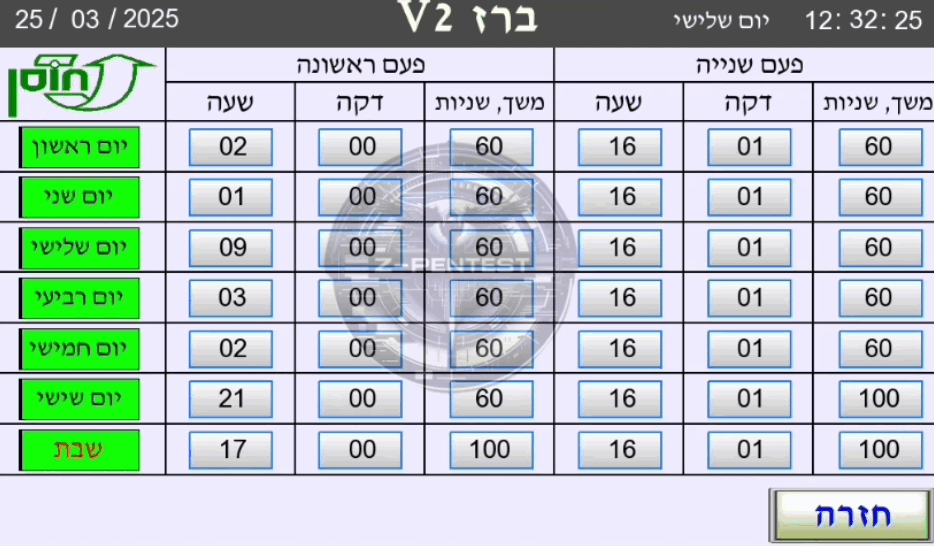
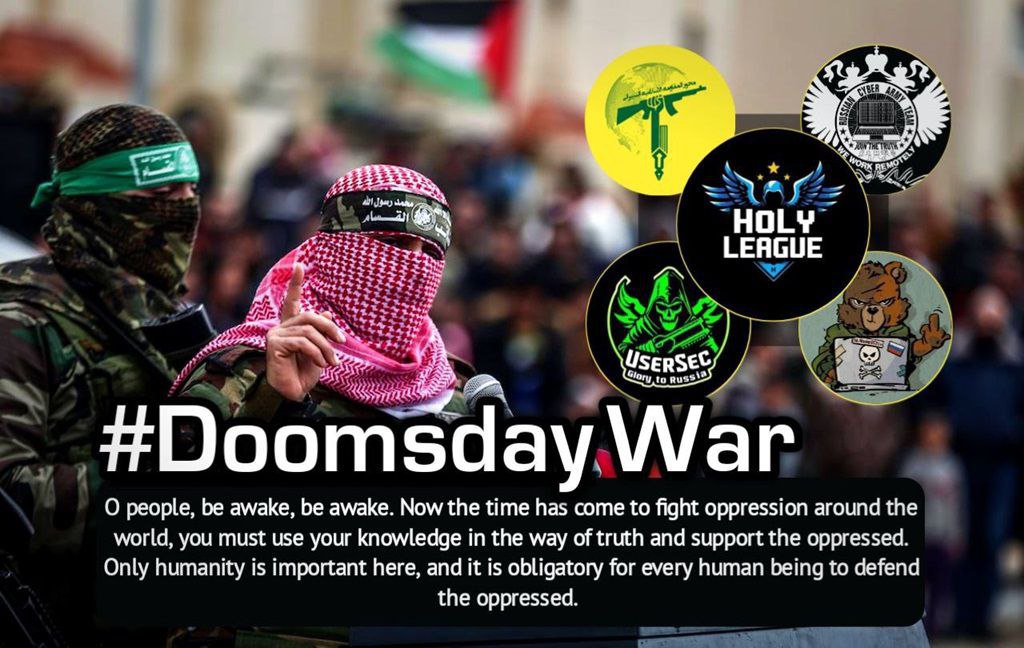
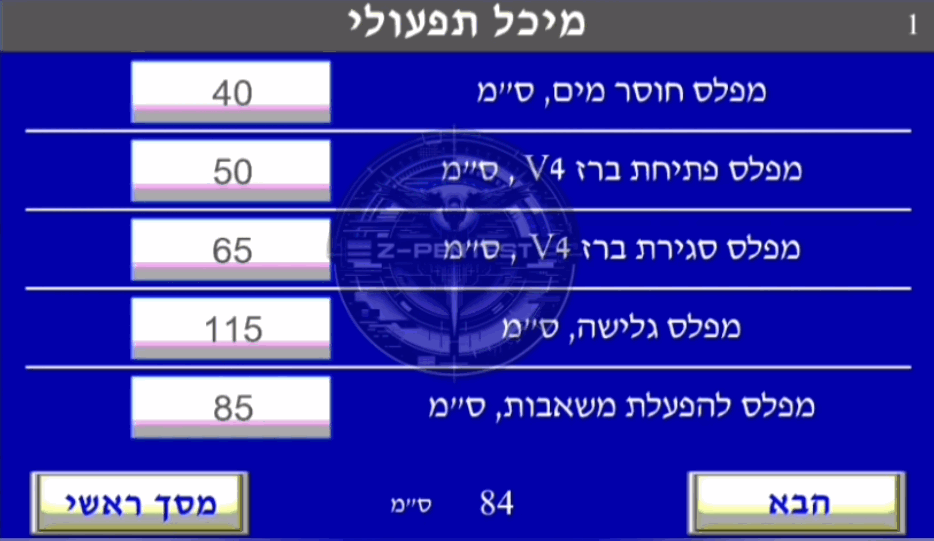
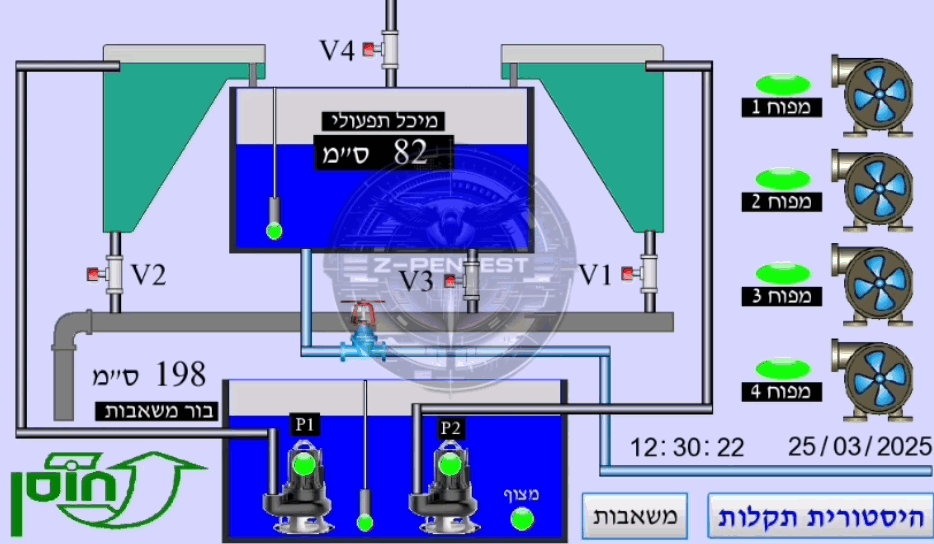
Z-Pentest Alliance is a pro-Russia-aligned hacktivist coalition brand widely cited in OSINT for targeting critical infrastructure, especially energy and water, and for publishing OT/ICS proof-of-access artifacts to amplify psychological impact. Government and partner reporting on pro-Russia hacktivism emphasizes opportunistic abuse of exposed remote access (including VNC) to reach OT devices. Evidence strongly supports intimidation/disruption posture; true operational impact of OT manipulation claims varies and should be validated with victim telemetry. Techniques involving OT manipulation are marked as INFERENCE where not corroborated.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1021.005 | VNC | TA0008 |
|
| T1210 | Exploitation of Remote Services | TA0008 |
|
| T1585.001 | Social Media Accounts | TA0042 | |
| T1498 | Network Denial of Service | TA0040 |
|
| T0889 | Modify Program | TA0110 |
|
Z-Pentest Alliance — Pro-Russia-aligned Hacktivist Alliance (OT/ICS Intrusion & Disruption)
Classification: TLP: WHITE — Open Source Intelligence (OSINT)
Category: Cyber / Hybrid — Hacktivism with OT/ICS focus; intimidation and disruption
Assessed home base: Serbia-linked in self-presentation; operationally embedded in a broader pro-Russia-aligned ecosystem
Executive Summary
Z-Pentest Alliance is a pro-Russia-aligned hacktivist coalition brand frequently cited in OSINT as a high-tempo actor focused on critical infrastructure narratives and, notably, internet-exposed OT/ICS environments. Multiple OSINT sources describe a shift beyond traditional hacktivist DDoS and defacement toward unauthorized access to industrial control interfaces (HMI/SCADA) and the public release of videos to amplify psychological impact.
Government and international reporting on pro-Russia hacktivism highlights opportunistic exploitation of weak remote-access exposures (including VNC) to access OT devices and conduct disruptive operations. In this context, Z-Pentest is consistently positioned among the more prominent pro-Russia-aligned brands targeting critical infrastructure.
Confidence is high that the Z-Pentest Alliance brand is used within pro-Russia hacktivist ecosystems and is strongly associated with OT/ICS-themed intimidation and disruption narratives. Confidence is medium regarding the true operational impact of claimed OT “sabotage,” as several sources assess some claims as primarily psychological and not necessarily resulting in material operational disruption.
IOC Appendix (TLP:WHITE) — Z-Pentest Alliance
Note: Open sources emphasize an exposure-driven OT access pattern and intimidation artifacts rather than stable malware infrastructure. This appendix prioritizes behavioral indicators and scoping cues over static IOCs.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
