Threat Actor Characterization

Yemen Electronic Army
ID: 428c2b256666ec5cf86f7617b2777ffa74589| Ciberejército de Yemen | Y.C.A | Y** | Y***** |
| Y** | Ye************** | Ye************ | Ye***************** |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
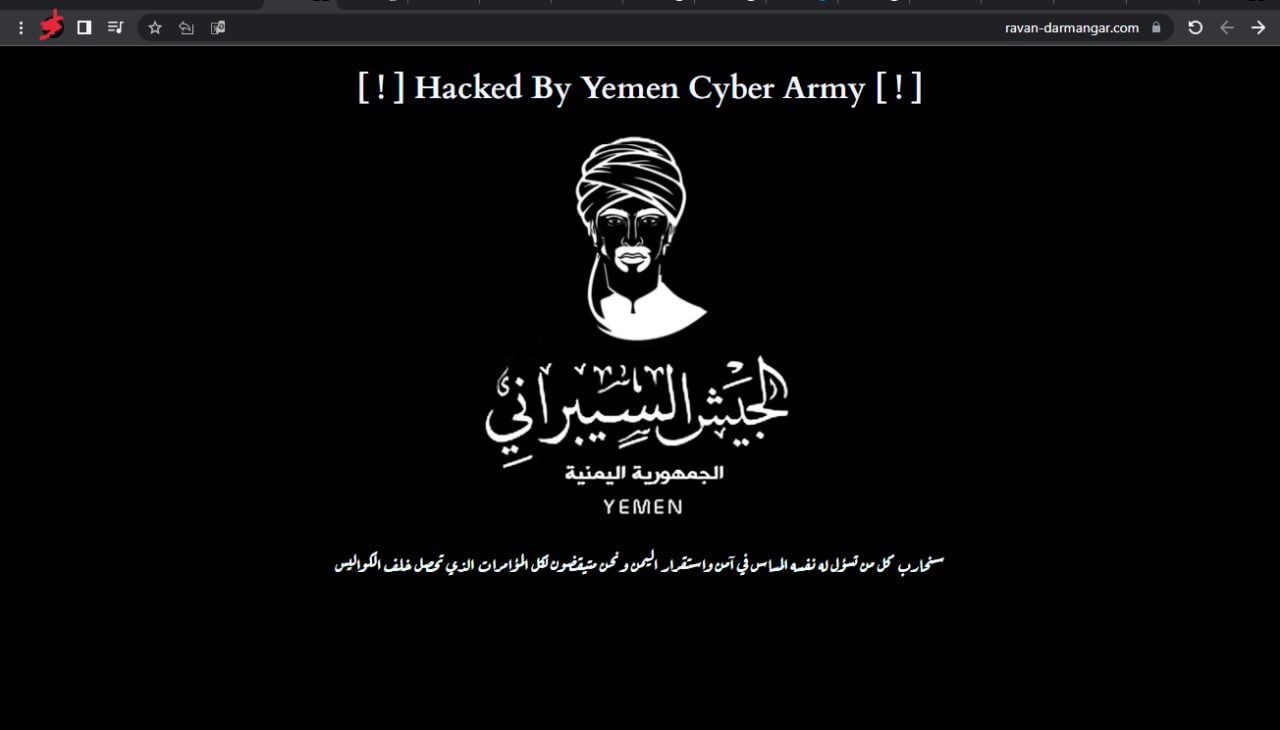
Yemen Electronic Army (YEA) — pro-Yemeni/Pro-Houthi hacktivist label often overlapping with Yemen Cyber Army; 2015 defacement of Al-Hayat and Saudi MFA data leaks used for propaganda.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1491.002 | External Defacement | TA0040 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1041 | Exfiltration Over C2 Channel | TA0010 |
|
CLASSIFICATION: Unclassified / Open Source
Executive Summary
Open sources suggest that “Yemen Electronic Army” (YEA) surfaced around 2015 and is frequently conflated with or considered an alias/label variant of the Yemen Cyber Army (YCA). Operations attributed in that period include the defacement of Al-Hayat (London-based, pro-Saudi) and subsequent data theft from Saudi Arabia’s Ministry of Foreign Affairs, later publicized via WikiLeaks mirrors. Multiple analyses assessed possible Iranian linkages (infrastructure, Persian language indicators), framing the activity within Iran–Saudi proxy dynamics during the Yemen war. Public cases resurfaced in 2025 with the UK sentencing of a YCA-linked defacer. Overall capability: low–moderate (defacement/exfil via opportunistic vectors); Confidence: medium for YEA as a distinct brand, high that the operations are real under the YCA/YEA umbrella.
Pro-Yemeni/Pro-Houthi hacktivist posture; messaging targets Saudi and allied interests during the conflict. Several researchers describe Iranian support/enablement as plausible.
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
 Free Preview
Free Preview
