Threat Actor Characterization

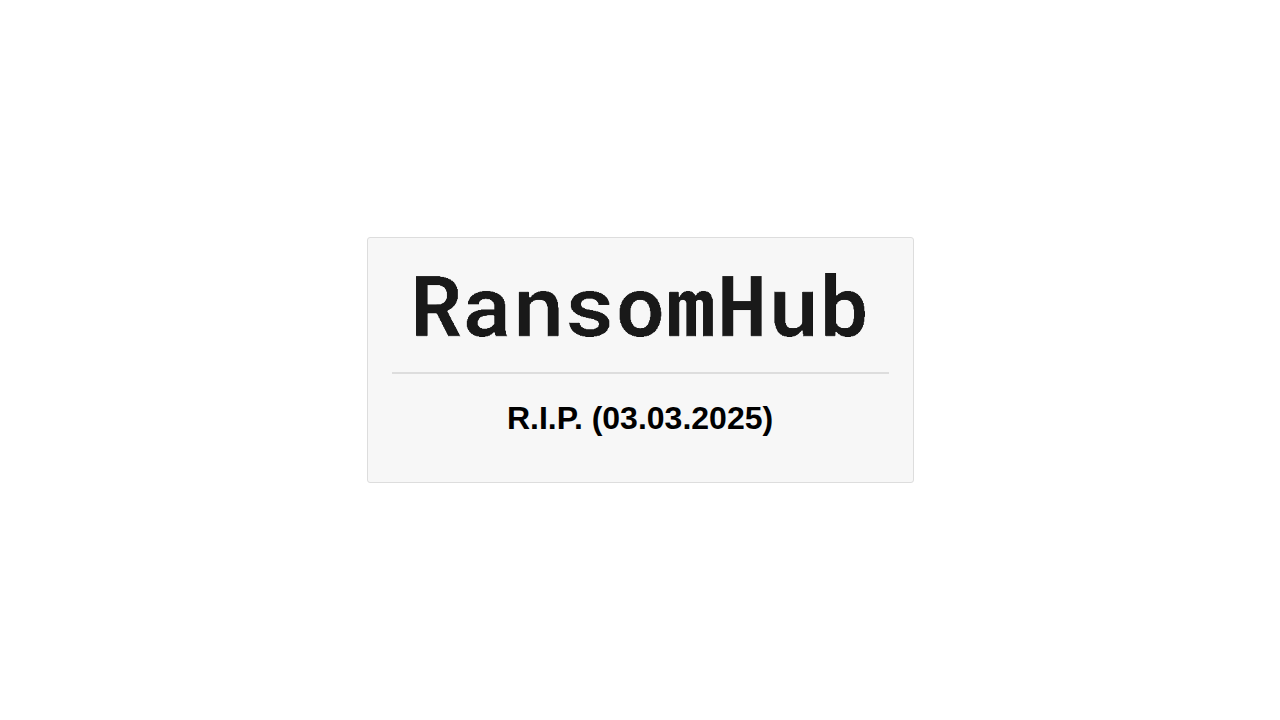
RansomHub
ID: 400cac598c390f6f5f478ca7b58adcd891597| Ransomhub Group | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
RansomHub is a Ransomware-as-a-Service (RaaS) operation active since early 2024, enabling affiliates to conduct double-extortion intrusions that combine data theft and encryption; reporting highlights defense-evasion steps (including anti-EDR tooling) and enterprise-scale lateral movement prior to impact.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1562.001 | Disable or Modify Tools | TA0005 |
|
| T1068 | Exploitation for Privilege Escalation | TA0004 |
|
| T1070.001 | Clear Windows Event Logs | TA0005 |
|
| T1490 | Inhibit System Recovery | TA0040 |
|
| T1021.002 | SMB/Windows Admin Shares | TA0008 |
|
| T1048.003 | Exfiltration Over Unencrypted Non-C2 Protocol | TA0010 |
|
| T1486 | Data Encrypted for Impact | TA0040 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1583.001 | Domains | TA0042 |
|
| T1105 | Ingress Tool Transfer | TA0011 |
|
RansomHub — RaaS ransomware operation (affiliate ecosystem)
Classification: TLP:WHITE — Open Source Intelligence (OSINT)
Category: Cyber — Ransomware-as-a-Service (RaaS) / Double-extortion — Origin: likely Russian-speaking ecosystem (INFERENCE, confidence: medium)
Author: iQBlack CTI Team
Executive Summary
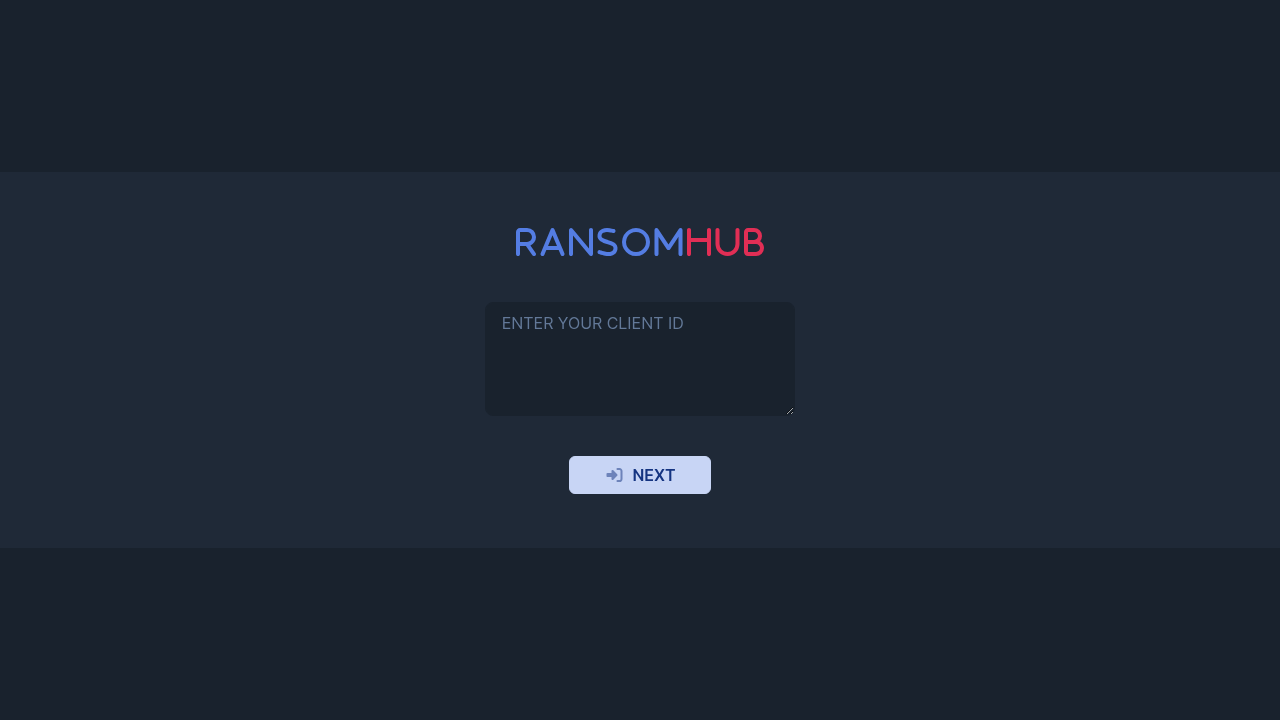
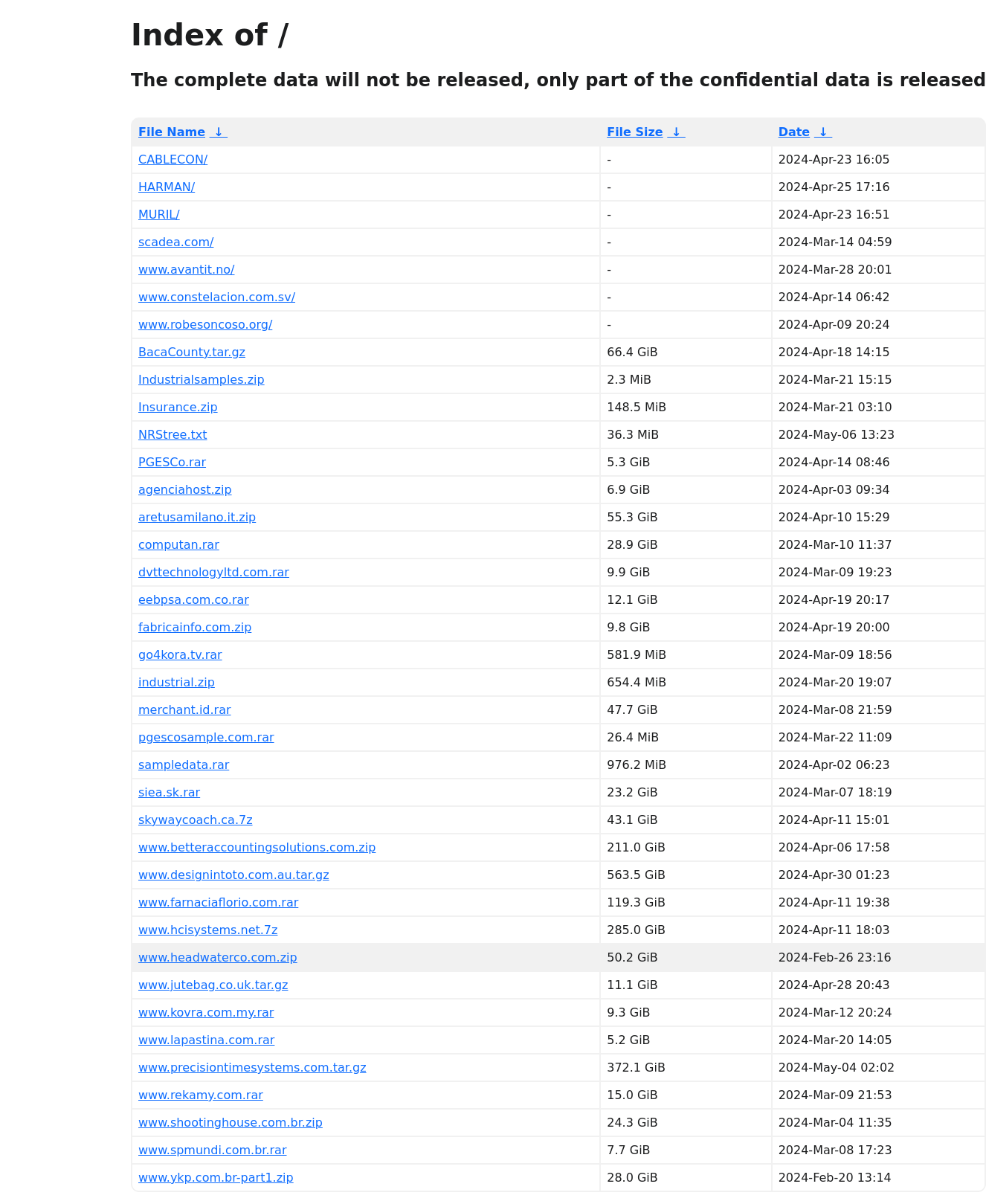
RansomHub is a ransomware-as-a-service (RaaS) operation that emerged publicly in early 2024 and rapidly scaled through an affiliate program model. Public reporting and casework consistently describe a double‑extortion workflow: affiliates obtain initial access, conduct internal discovery and credential access, exfiltrate sensitive data, and then deploy encryption at scale while threatening public release via a dedicated leak site.
RansomHub is frequently described as having lineage overlap with the earlier “Knight” ransomware family, with multiple vendors assessing strong code similarity and evolution rather than a wholly new codebase. This matters operationally because lineage often implies reuse of deployment conventions, configuration structures, and encryption implementation choices that remain stable across rebrands.
A defining operational theme across reporting is “defense evasion as a first‑class objective.” Multiple sources describe anti‑EDR and endpoint tampering, including the use of an “EDR killer” tool commonly referred to as EDRKillShifter, alongside commodity post‑exploitation tooling and living‑off‑the‑land (LOLBIN) execution. This creates a predictable defensive posture requirement: visibility and response controls must be resilient against driver/process termination and policy tampering, not only against the final ransomware binary.