Threat Actor Characterization
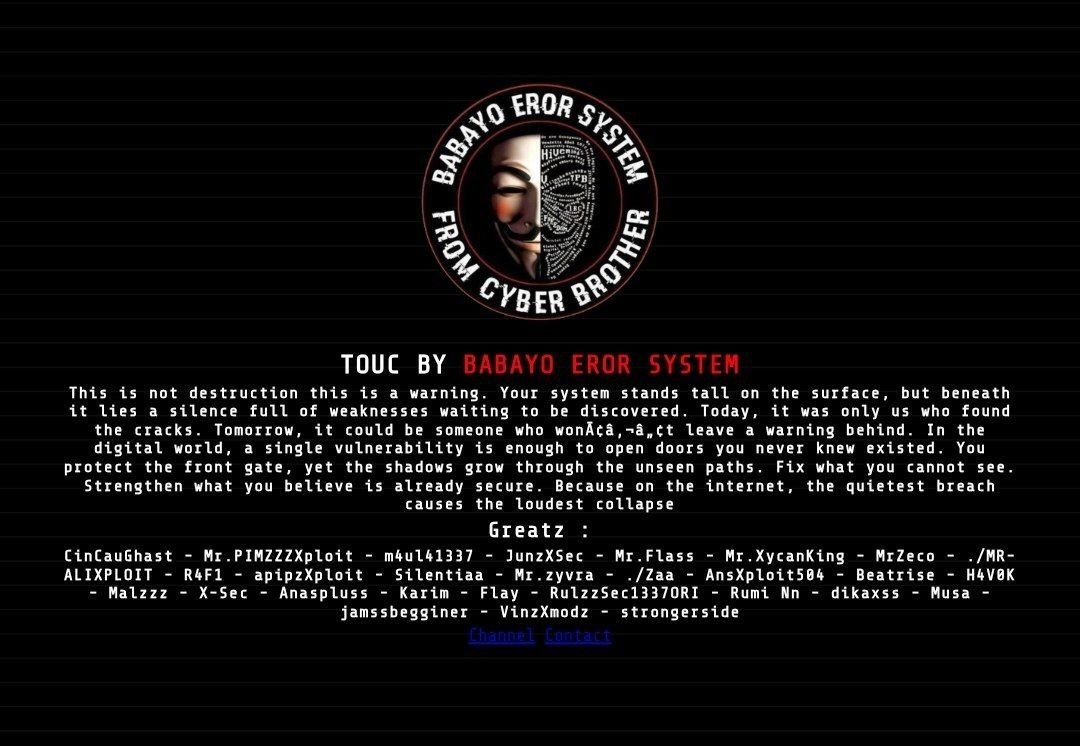
BABAYO EROR SYSTEM
ID: 3df81a17317be130b3ac3e7d5226b09534506| BabayoErorSyteam | — | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
BABAYO EROR SYSTEM is an emerging hacktivist / defacement-and-claims cluster with visible Telegram infrastructure, recurring defacement archive presence, and lower-confidence DDoS claim activity tied to wider geopolitical campaigns.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 | |
| T1491.001 | Internal Defacement | TA0040 | |
| T1498 | Network Denial of Service | TA0040 | |
| T1595 | Active Scanning | TA0043 |
|
| T1585.001 | Social Media Accounts | TA0042 |
|
BABAYO EROR SYSTEM — Emerging Hacktivist / Defacement-and-Claims Cluster
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Hacktivism / Defacement / DDoS Claims
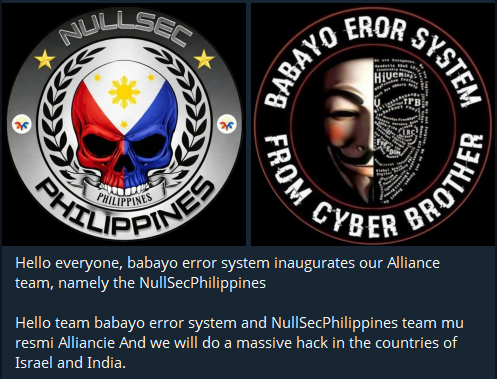
Assessed origin / home base: Unknown; probable Southeast Asia / Indonesia nexus with later opportunistic alignment to broader anti-Israel / anti-U.S. campaign narratives.
Author: iQBlack CTI Team
Executive Summary
BABAYO EROR SYSTEM is an emerging hacktivist brand with visible public infrastructure on Telegram and a measurable footprint in defacement archives and attack-claim monitoring during 2025–2026. The actor is most consistently associated with website defacement, claimed DDoS activity, and noisy propaganda-oriented targeting rather than with deeply documented stealth intrusions or long-term access operations.
Public evidence supports treating BABAYO EROR SYSTEM as a real cluster rather than a one-off alias. Multiple archive services record defacement activity attributed to the team, public Telegram directories expose a named channel for the brand, and threat-tracking commentary repeatedly lists the actor among active hacktivist groups involved in anti-Israel, pro-Palestinian, and later anti-U.S. / anti-Israel narrative campaigns.