Threat Actor Characterization

Killada
ID: 3badcb15c587d360409ed9154b88249958379| Killada Ransomware | Killada Sec | Ki******** | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Killada is an emerging ransomware brand first publicly tracked in March 2026. Current public evidence supports a functional criminal extortion workflow, but the wider operator structure and campaign scope remain unclear.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1486 | Data Encrypted for Impact | TA0040 |
|
| T1204.002 | Malicious File | TA0002 |
|
| T1566 | Phishing | TA0001 |
|
| T1083 | File and Directory Discovery | TA0007 |
|
| T1059 | Command and Scripting Interpreter | TA0002 |
|
Killada — Emerging Ransomware Brand with Sparse but Actionable Early Telemetry
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Cybercrime / Ransomware - Origin: Unknown
Author: iQBlack CTI Team
Executive Summary
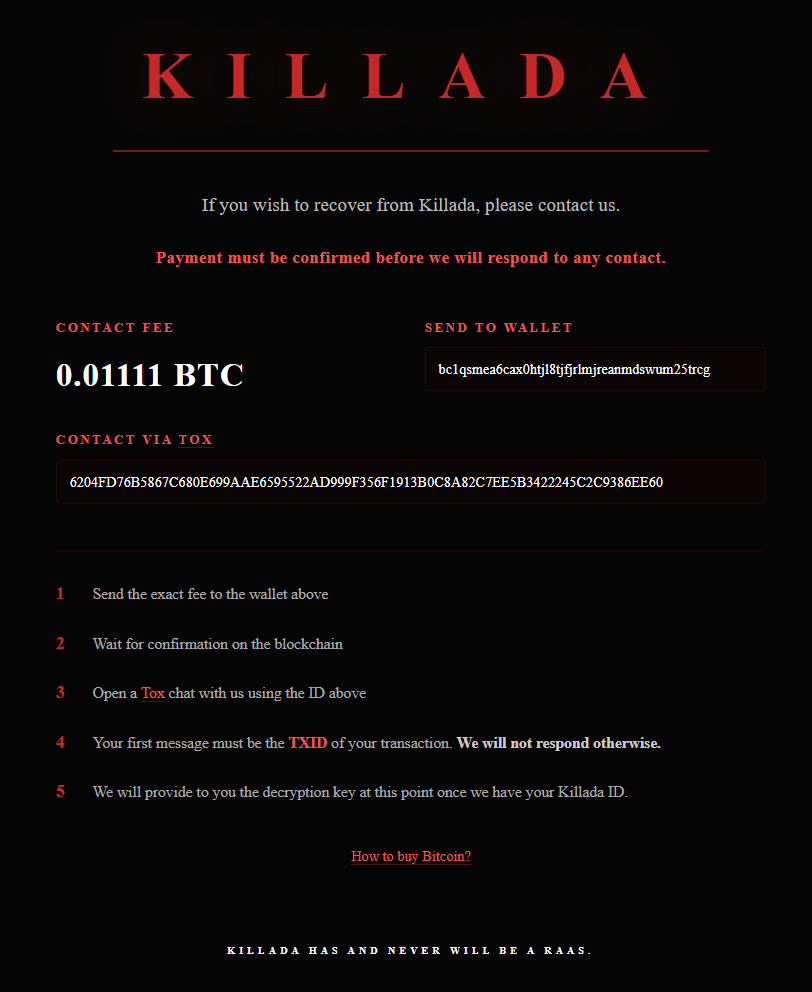
Killada is an emerging ransomware brand first publicly tracked in March 2026. Open reporting is still thin, but multiple public indicators already support treating it as a real ransomware operation rather than a purely speculative label: a dedicated set of onion extortion links, a named ransom note, a BTC wallet, a TOX identifier, and at least two publicly observed samples associated with the brand.
At this stage, the operation appears immature or early in its lifecycle. Available public references do not yet show a stable victim corpus, a mature leak-site narrative, or a deeply documented affiliate ecosystem. That limits confidence on strategic attribution, country of origin, and operator structure.