Threat Actor Characterization
You’re viewing the read-only version.
Sign in for analyst tools (editors, promote draft, file/relations management, etc.)

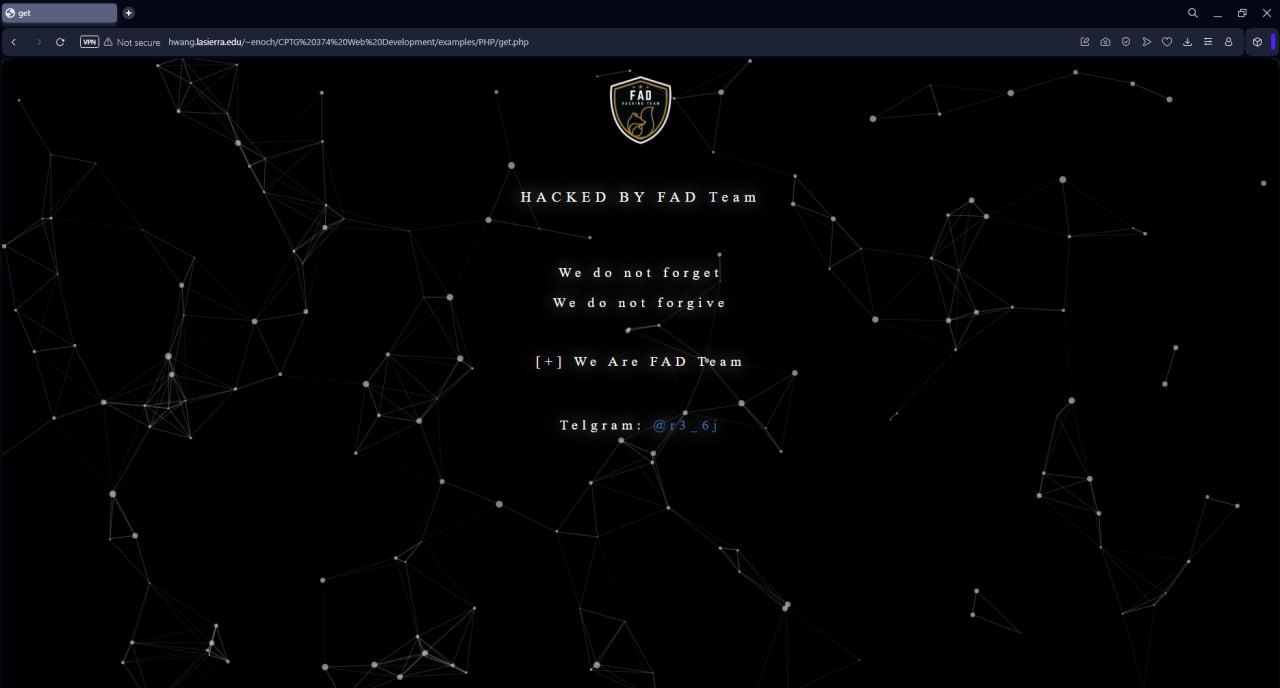
FAD Team
ID: 3412c085cd48f2aac22c28d06be5d8ec94981
Hacktivist Group
Hacktivism
Threat types: Hacktivism, Intrusion, Data Theft, Data Leak, SQLi, Pro-Iran
Progress: 91%
Completeness: 92%
Freshness: 90%
Operation zone: Israel
Aliases
Limited alias preview
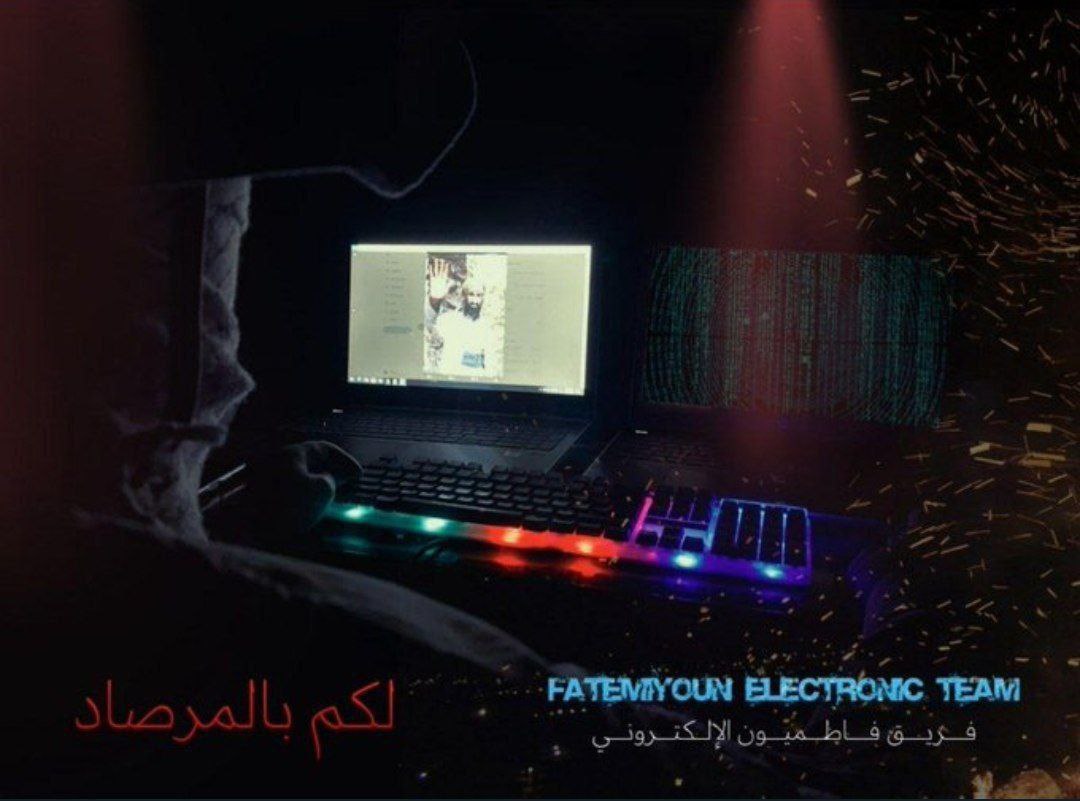
| Alien Team | Equipo Electrónico de Fatimiyoun | FA************** | Fa*********************** |
| Fa***************** | Fa******** | Fa************************ | Ir******************* |
| Th************ | فا***** | فر********************* | — |
Showing 2 of 11 aliases in free preview.
Actor Network Graph
Open Network GraphMITRE ATT&CK®
confidence: medium
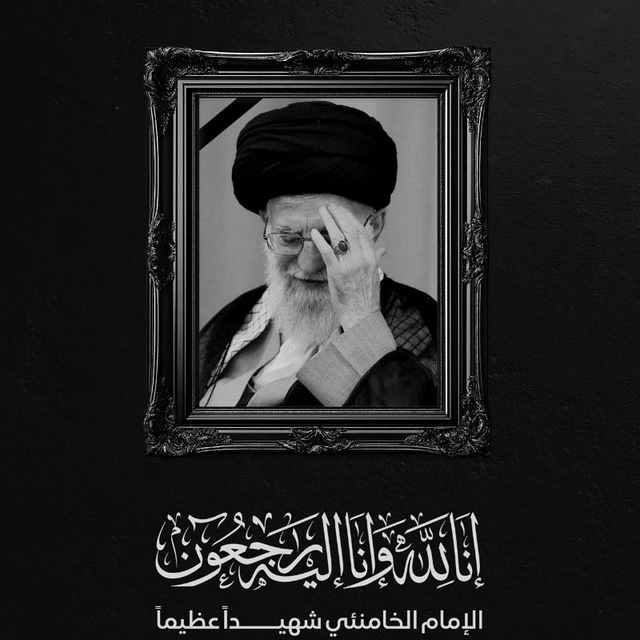
FAD Team is referenced in early 2026 reporting as an Iran-aligned hacktivist brand (Fatimiyoun/Fatimion cyber team / Resistance Hub). Reporting associates the group with SQL injection and code injection claims leading to data theft/PII leaks, alongside a destructive posture characterized by vendor reporting as wiper-focused permanent data destruction.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 | |
| T1005 | Data from Local System | TA0009 |
|
| T1485 | Data Destruction | TA0040 |
|
| T1498 | Network Denial of Service | TA0040 |
|
| T1585 | Establish Accounts | TA0042 |
|
Executive brief
now
Saved successfully.
Hunting Playbook
now
Saved successfully.
IOC Appendix
now
Saved successfully.
OSINT Library
now
Saved successfully.