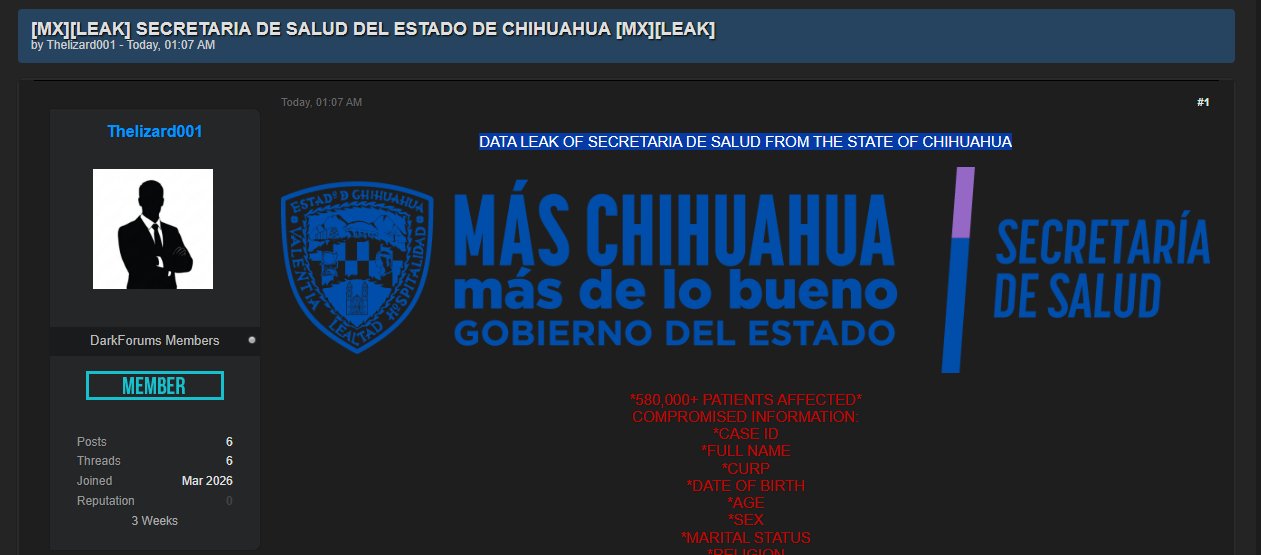
Threat Actor Characterization

Lizard
ID: 2f7569e00c4d97aef5f2c2b3a4d2213f03521| Lizard001 | The Lizard 001 | Th********** | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
Lizard is a Chronus Team-linked operator/persona associated with data-leak and public-pressure activity affecting Latin American public institutions. Available evidence supports treating the alias as part of a semi-decentralized collaborative ecosystem rather than as a standalone intrusion organization.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1078 | Valid Accounts | TA0001 TA0003 TA0004 TA0005 |
|
| T1005 | Data from Local System | TA0009 |
|
| T1567 | Exfiltration Over Web Service | TA0010 |
|
| T1491.001 | Internal Defacement | TA0040 |
|
Lizard — Chronus Team-linked operator
Classification: Unclassified / Open Source Intelligence (OSINT) + Limited Human Intelligence (HUMINT) — TLP:WHITE
Category: Cybercrime / Hacktivism-adjacent intrusion and data-leak activity - Origin: Mexico (assessed, not confirmed)
Author: iQBlack CTI Team
Executive Summary
Lizard is assessed as a public-facing operator or participant associated with the broader Chronus Team ecosystem, a Latin American intrusion-and-leak cluster that has repeatedly targeted public-sector and quasi-public institutions for reputational pressure, data exposure, and propaganda value. Available reporting does not support treating Lizard as a standalone organization; rather, the alias is best placed inside a semi-decentralized brand environment in which multiple named participants claim or co-sign operations under the Chronus label.
Current confidence is medium regarding Lizard’s membership or active participation in Chronus Team operations, and medium-high regarding the actor’s role in a concentrated set of data-leak claims affecting Argentine institutions in late March 2026. Newly supplied internally collected reporting ties Lizard to a broad cluster of Argentine government, security, education, health, and financial-sector related releases, materially increasing the alias’s operational relevance inside the Chronus graph.