Threat Actor Characterization

Abo Omar
ID: 2c5e9d7d9c904bb71fa38130a565bc4438308| Abu Omar | Brother Abu Omar | Ge************** | M**** |
| M***** | T*** | — | — |
Actor Network Graph
Open Network GraphMITRE ATT&CK®
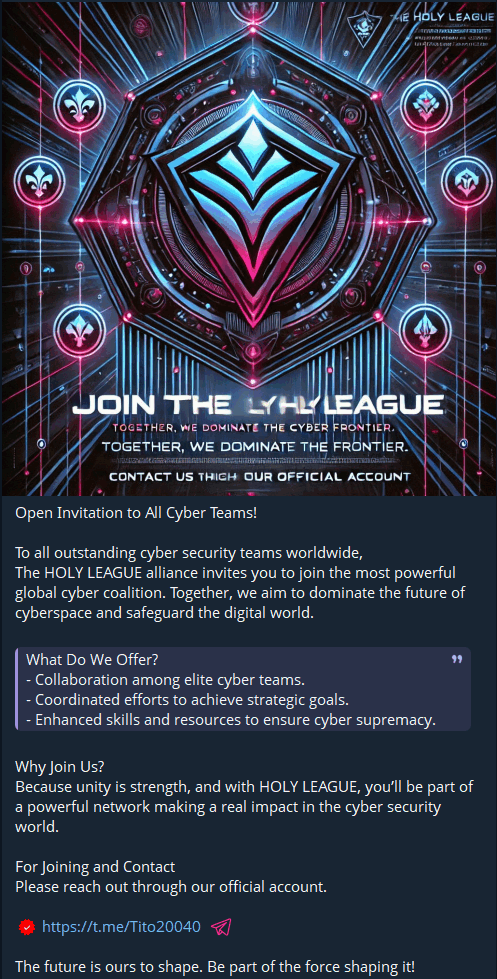
Abo Omar, also referenced as Tito and linked to the Mhwear Telegram handle family, is assessed as a public command persona within the Cyber Islamic Resistance / Holy League ecosystem. He appears to coordinate messaging, coalition signaling, and public attribution of disruptive cyber activity rather than acting as a fully resolved standalone intrusion operator.
| Technique | Technique name | Tactics | Evidence |
|---|---|---|---|
| T1595 | Active Scanning | TA0043 |
|
| T1190 | Exploit Public-Facing Application | TA0001 |
|
| T1498 | Network Denial of Service | TA0040 | |
| T1491.001 | Internal Defacement | TA0040 | |
| T1567 | Exfiltration Over Web Service | TA0010 |
|
Abo Omar / Tito / Mhwear — Public Command Persona within the Cyber Islamic Resistance / Holy League Cluster
Classification: Unclassified / Open Source Intelligence (OSINT) — TLP:WHITE
Category: Cyber / Hybrid Hacktivist-Extremist Persona — Origin: Unresolved; likely embedded in the Iraq–Syria–Lebanon-facing “axis of resistance” online ecosystem
Author: iQBlack CTI Team
Executive Summary
Abo Omar, also referenced as Tito and associated with the Mhwear Telegram handle family, is best assessed not as a fully resolved real-world individual but as the central public command persona used to brand, coordinate, and legitimize activity under the Cyber Islamic Resistance / Islamic Resistance Axis / Holy League stack. Public channel language repeatedly presents him as a commander, leader, or principal voice of that ecosystem. Multiple Telegram identities in the @Mhwear* family appear to operate as a surrounding communications architecture rather than independent actor brands.
The persona’s intelligence value lies less in attributed hands-on-keyboard tradecraft than in what it reveals about cluster organization. Abo Omar appears to serve as the narrative anchor through which coalition messaging, target signaling, mobilization appeals, ideological framing, and selective operational claims are packaged for public consumption. In practical terms, he functions as a command mask, propaganda focal point, and likely coordinator for a broader anti-Israel cyber-propaganda environment with visible pro-Iran, pro-Hezbollah/Hamas-adjacent, and at times pro-Russian convergence.